
DevOps pipelines run on secrets — API keys, tokens, and certificates move through automated CI/CD workflows at high velocity without human oversight. Securing this machine-to-machine access requires a dedicated secrets management strategy built for automation. As infrastructure scales, protecting these credentials becomes essential for continuous, secure delivery.
According to Verizon’s 2025 DBIR, credential abuse accounts for 22% of initial access vectors, and stolen credentials are involved in 88% of basic web application attacks. IBM’s 2025 report puts the global average breach cost at $4.44M with a 241-day lifecycle. For breaches caused by compromised credentials, the average is $4.67M and 246 days.
Key takeaways:
- Secrets encompass API keys, OAuth tokens, Secure Shell keys, and certificates
- Centralized storage with automated rotation prevents theft
- Regulatory compliance, like GDPR, PCI-DSS, and HIPAA, requires proper management
Unlike traditional password tools, DevOps secrets management focuses on machine authentication at scale. It secures credentials in encrypted vaults, injects them into authorized services, rotates them automatically, and maintains audit logs to ensure compliance.
The risks of poor secrets management
In 2024, GitHub's security scans uncovered 39 million exposed secrets across public repositories. Developers had embedded credentials directly in code, a practice that persists because Git preserves complete history. Even "deleted" secrets remain accessible. The problem compounds through secret sprawl.
Critical risks:
- Repository history preserves hardcoded secrets indefinitely
- Scattered secrets eliminate usage visibility
- Extended credential lifespans widen attack windows
- Compliance gaps trigger compliance violations
Common challenges in DevOps secrets management
In dynamic DevOps environments, secrets frequently move across automated systems, creating challenges:
- Secret sprawl. Credentials end up in repositories, config files, environment variables, and notes, making tracking difficult.
- Credential rotation. Regularly updating secrets is essential, but it often leads to deployment failures when overlooked.
- Multi-cloud complexity. Each cloud provider uses unique tools and access controls, leading to fragmented and risky duplication of secrets.
Security measures can slow deployments, pushing developers to hardcode credentials to save time. Solutions like Jenkins, GitHub Actions, and GitLab CI address this by injecting secrets at runtime, ensuring they exist only during deployment. Automated retrieval eliminates delays while maintaining security.
Hybrid and multi-cloud setups scatter secrets across various platforms, each with different access controls. For example, database passwords may reside on one cloud, API keys on another, and certificates on-premise. Without consistent access management, integration becomes complex and error-prone.
Real-world examples of secret exposure incidents
A 2024 U.S. Treasury breach traced to leaked API keys let attackers bypass security. CVE-2025-30066 showed compromised GitHub Actions leaking credentials into logs. Notable incidents affected major enterprises, many involving OAuth tokens.
96% of exposed GitHub tokens had write permissions, meaning attackers could potentially modify repositories rather than only read data. Cloud account compromises originate from exposed credentials: attackers scan GitHub, GitLab, and Bitbucket for API keys granting cloud access.
These data breaches share common patterns: credentials stored where they shouldn't be and valid longer than necessary. Prevention requires centralized storage and automated rotation working together.
DevOps secrets management best practices
Centralized management forms the foundation of secure DevOps environments. Store all credentials in dedicated vaults with AES-256 at-rest encryption. Set up automated rotation policies to expire and replace credentials on schedule, maintaining complete audit logs for compliance. In line with industry standards, OWASP guidance emphasizes standardizing approaches.
Core practices:
- Centralize secrets in dedicated vaults
- Encrypt using AES-256 or stronger
- Automate rotation policies
- Apply zero trust and least privilege
- Maintain complete audit logs
To effectively implement zero-trust and least-privilege principles, organizations should shrink their attack surface by verifying every access request and restricting permissions to role requirements through Role-based access control (RBAC). Identity management systems like Active Directory (AD) or LDAP can enforce these policies, supplemented with multi-factor authentication (MFA) and just-in-time, single-use credentials.
Hardcoded secrets should not be present in the codebase; instead, environment variables or direct vault integrations should be used for runtime access. To prevent credentials from entering repository history, organizations can implement pre-commit hooks with tools like Gitleaks or Talisman. Proper .gitignore configuration is also essential to exclude sensitive files.
Finding and removing hardcoded secrets:
- Scan Git repositories with automated detection tools
- Implement pre-commit hooks blocking secrets before commits
- Use environment variables for runtime credential access
- Rotate discovered passwords and credentials immediately
- Educate developers on secure handling practices
Handling secrets in code repositories
Before Git commits are complete, pre-commit hooks scan for exposed credentials. For continuous monitoring, GitHub, GitLab, and Bitbucket provide native detection that alerts when credentials appear. GitGuardian monitors repositories continuously and catches secrets that bypass initial checks.
In the .gitignore configuration, exclude files containing secrets. Developer education matters equally: private repositories provide insufficient protection — anyone with access can read them.
Pre-commit hook configuration for Gitleaks
#!/bin/bash
# Save as .git/hooks/pre-commit
gitleaks protect --staged --verbose
if [ $? -ne 0 ]; then
echo "! Gitleaks detected secrets"
echo "Remove secrets and retry"
exit 1
fi
Best secrets management tools for DevOps 2026
For teams using a single cloud, native tools simplify operations. For example, AWS Secrets Manager automates credential rotation and integrates with access controls. Setup is quick, taking hours instead of weeks. However, this convenience comes with the downside of being locked into one provider.
In multi-cloud environments, managing secrets becomes fragmented. Credentials for Amazon, Microsoft, and Google services are stored in separate vaults, requiring different integration codes for each platform. Tools like HashiCorp Vault solve this by supporting multiple clouds, but they require specialized expertise to manage.
When managing both employee passwords and application secrets, organizations often use separate tools. This duplication increases costs and complexity, and Passwork handles both.
Developers should also configure .gitignore to exclude files with sensitive data and understand that private repositories alone don’t guarantee security — anyone with access can view their contents.
Open-source vs. commercial solutions
Some secrets management platforms offer both open-source and enterprise versions. Open-source solutions attract teams with transparent code, community support, and no licensing costs. In contrast, enterprise platforms provide dedicated support, compliance certifications, and advanced monitoring.
SaaS deployment removes the need for infrastructure management but adds third-party dependencies. Total costs include not just licensing fees, but also operational expenses.
5 criteria that actually matter when choosing a tool
Start with documented requirements. How many secrets need management, hundreds or thousands?
Evaluation criteria:
- Integration with existing CI/CD tools
- Scalability supporting growth
- Compliance certifications matching requirements
- Deployment flexibility balancing control and operations
- Total cost, including infrastructure and staff time
Managing passwords and DevOps secrets in a single system reduces overhead and improves cost efficiency. Unified role-based access controls simplify administration and mirror your organizational structure.
On-premise deployment keeps all credentials securely within your infrastructure — giving you complete control over sensitive data. The solution integrates seamlessly with Active Directory, LDAP, and SSO protocols.
How to automate secrets management in DevOps
Automation replaces manual updates with scheduled credential rotation. CI/CD pipelines, such as Jenkins, GitHub Actions, and GitLab CI, connect directly to secret platforms via APIs for runtime delivery.
The standard integration flow is secure: runners authenticate with short-lived tokens, retrieve secrets, and inject them as environment variables. Credentials never persist in pipeline definitions or logs.
image: passwork-cli:latest
pipelines:
default:
- step:
name: Deploy with secured credentials
script:
# Get database credentials from Passwork and run database migrations
- passwork-cli exec --password-id "db_credentials" \
python manage.py migrate
# Get API keys from Passwork and run deployment script
- passwork-cli exec --password-id "api_keys,deploy_keys" \
./scripts/deploy.sh
# Notify the team with a direct API call
- passwork-cli api --method POST \
--endpoint "v1/inbox/messages" \
--params '{"recipient":"devops","message":"Deployment completed successfully"}'
services:
- docker
definitions:
services:
docker:
memory: 2048
Regular replacement of secrets reduces exposure windows. Modern secrets platforms generate dynamic credentials on demand through configurable time-to-live (TTL) values. Cloud-native tools automate rotation for their respective services. Different assets require distinct rotation strategies — API keys rotate differently than TLS/SSL certificates or database passwords.
Graceful refresh mechanisms allow applications to retrieve updated credentials without restarts. When requests arrive, vaults create unique credentials valid for that specific session. After disconnection, automatic revocation follows.
Upon compromise detection, revocation processes activate immediately. Rotation should occur when compromise is detected or suspected, or during security incidents.
Building a secrets management strategy
Successful implementation requires strategic planning beyond tool selection. Strategy covers organizational change management, phased rollout, and success metrics.
Organizations must gain stakeholder buy-in from development, security, and infrastructure teams. Phased implementation starts with non-production environments, proves the approach, then expands.
Implementation phases:
- Assessment. Inventory existing secrets, identify security gaps, and document current workflows.
- Planning. Select tools, define policies, establish rotation schedules, and configure access controls.
- Pilot. Deploy to non-production environments, train teams, and refine processes.
- Rollout. Expand to production systems gradually, migrate existing secrets, and monitor adoption.
- Optimization. Tune policies, automate workflows, and measure success metrics.
What a secrets policy must cover
Formal security policies document secrets management requirements and establish governance. Policies should define what constitutes a secret, specify approved storage locations, establish rotation schedules, and outline incident response procedures.
Compliance requirements from GDPR, PCI-DSS, HIPAA, ISO 27001, and SOC 2 mandate specific controls: audit logging, encryption standards, and access restrictions. Involve security, development, and operations teams to craft the proper strategy.
Training and adoption
Technology alone can't secure credentials. Special training for teams should cover the risks of hard-coded credentials, proper tool use, and secure practices. DevSecOps culture integrates security naturally into workflows.
Monitoring and auditing secret usage
For anomaly detection and compliance demonstration, visibility into secret access becomes critical. In every audit entry, details should include who accessed which secrets, when, from which systems, and whether access succeeded.
These logs flow into security analytics platforms. Through Splunk and ELK Stack, teams analyze access patterns. Cloud-native tools integrate with their respective provider monitoring services.
From all sources, SIEM systems aggregate logs, then apply rules and machine learning to detect anomalies.
How to catch credential misuse before it becomes a breach
Between sensitivity and alert fatigue, security alerting finds balance. Through SIEM platforms, rules catch suspicious activities: access from unusual locations, high-value secret retrieval outside business hours, and multiple failed authentications. For baseline deviations, anomaly detection identifies patterns.
With Prometheus, Datadog, and PagerDuty integration, alerts reach teams immediately. Through our advanced admin tools, granular monitoring comes with customizable alerts and compliance reporting built in.
Frequently Asked Questions

What is DevOps secrets management, and why is it important?
DevOps secrets management securely stores, distributes, rotates, and audits credentials like API keys and tokens. Proper management prevents unauthorized access and maintains GDPR and PCI-DSS compliance.
What are the best practices for managing DevOps secrets and credentials?
Core practices include centralizing secrets in vaults, implementing automated rotation, applying zero trust and least privilege, eliminating hardcoded credentials, and maintaining audit logs.
How do you securely manage secrets in your CI/CD pipeline?
Integrate secrets management tools with Jenkins, GitHub Actions, and GitLab CI. Inject secrets at runtime as environment variables. Authenticate pipeline runners using short-lived tokens.
What tools are recommended for DevOps secrets management in 2026?
Cloud-native tools suit single-cloud environments but create vendor lock-in. Cross-platform solutions offer multi-cloud support but require operational expertise. Passwork combines password and secrets management with on-premise deployment and unified credential management.
How do you implement a centralized vault for DevOps secrets?
Select a platform based on integration needs, compliance requirements, and deployment preferences. Configure role-based access controls, establish rotation policies, and implement audit logging.
What are the security risks of improper secrets management?
GitHub detected 39 million leaked secrets in 2024. Risks include data breaches, compliance violations, and secret sprawl.
How do you avoid hardcoding secrets in your applications and infrastructure?
Store secrets in vaults and inject at runtime through environment variables. Use detection tools for continuous monitoring.
How should secrets be managed across multi-cloud environments?
Adopt unified platforms that work consistently across all cloud providers. We provide on-premise and cloud deployment flexibility, letting teams control sensitive secrets.
How do you rotate secrets regularly without disrupting services?
Implement automated rotation through platforms that support graceful updates. Applications need refresh mechanisms to retrieve updated credentials without restarts.

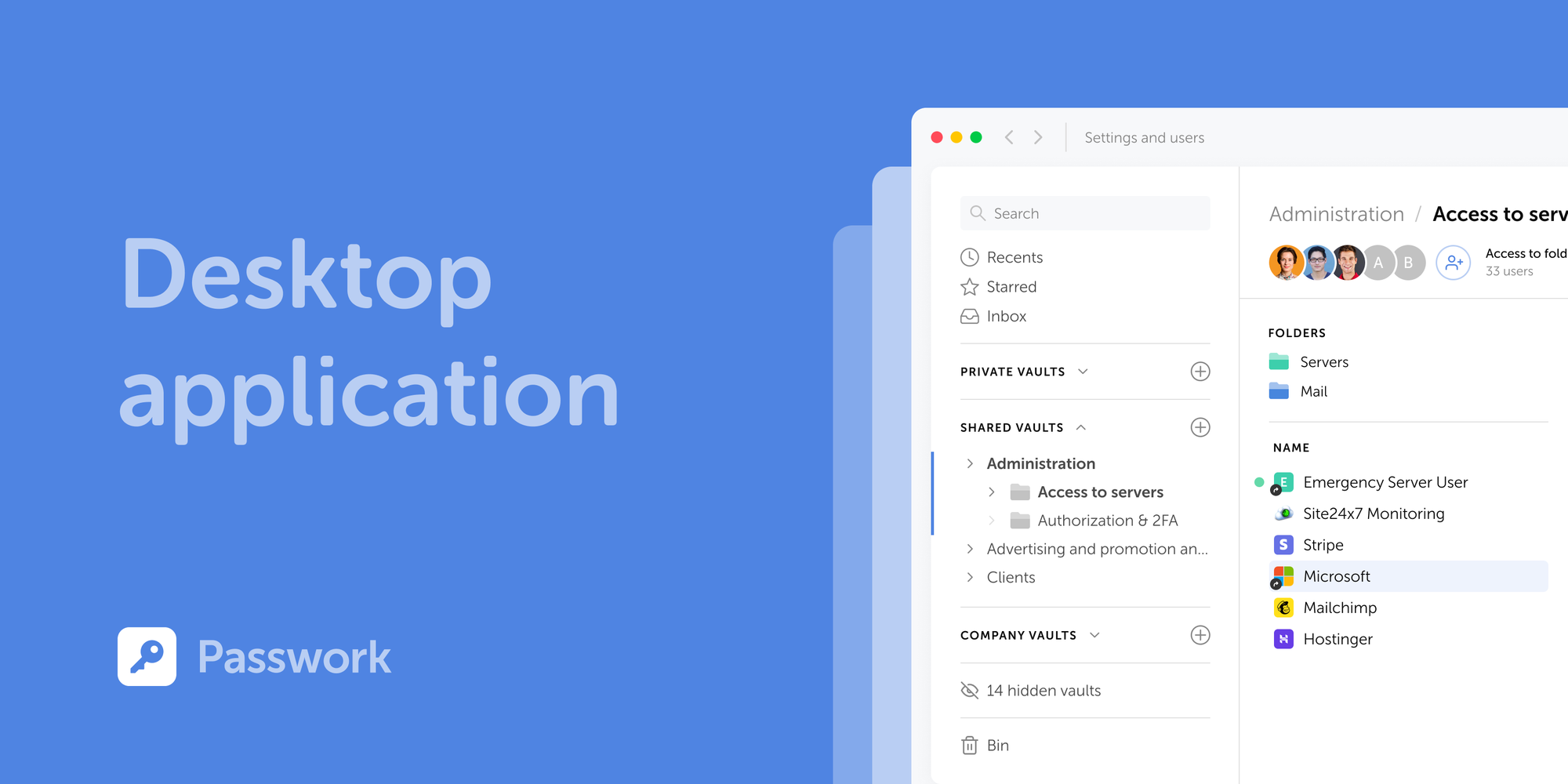
Table of contents
Table of contents
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more



