
Itroduction
NIS2 requires organizations to submit an early warning within 24 hours of detecting a significant incident — yet the average manual incident investigation takes longer than that just to establish basic facts.
The directive doesn't care. The clock starts at detection. And for security teams already running at capacity, that gap between what the regulation expects and what's operationally possible is exactly where compliance breaks down.
The 72-hour notification and 30-day final report add further layers of documentation, severity assessment, and cross-border impact analysis. All while the incident itself may still be active. Manual workflows weren't designed for this. The question is which parts to automate, and how.
This article maps the full 24–72–30 reporting framework against specific automation capabilities, identifies which tasks can be safely delegated to tooling, and defines where human judgment remains non-negotiable.
Key takeaways
- NIS2 Article 23 mandates a three-stage reporting process — early warning within 24 hours, incident notification within 72 hours, and a final report within 30 days. Each deadline carries specific content requirements.
- Automation is a regulatory expectation — NIS2 Article 29 addresses supervisory arrangements for cybersecurity, and ENISA's implementing guidance under the directive recommends automated monitoring and reporting as part of a mature compliance program.
- The EU faces a structural staffing gap of approximately 299,000 cybersecurity professionals — understaffed teams cannot sustain manual compliance workflows alongside active threat response. Automation removes the tasks that shouldn't require human judgment in the first place.
- The financial case for automation is measurable — organizations using AI and automation for compliance report up to a 40% reduction in compliance costs and an 80% reduction in audit preparation time. In breach scenarios, automation saves an average of $2.2 million compared to organizations without it.
- Credential management is a documented NIS2 obligation — Article 21(2)(i) explicitly requires access control policies and asset management; Article 21(2)(j) mandates MFA. Compromised credentials are the most common initial access vector, and regulators treat identity governance as a primary audit target.
- Automation handles data collection, triage, and evidence compilation, humans own the decisions — final sign-off on notifications, root cause determination, and regulatory communication require human accountability. The goal is to ensure security professionals spend their time on what only they can do.
The reality of the NIS2 reporting burden
NIS2 (Directive (EU) 2022/2555) is the EU's primary cybersecurity framework for critical infrastructure. It replaced the original NIS Directive and extended mandatory security and incident reporting obligations to 160,000+ organizations across essential and important sectors — from energy and banking to waste management and food production.
NIS2 compliance reporting places concrete, time-bound obligations on all of them. Meeting those obligations manually, under pressure, with limited staff, is structurally unreliable.
The 24–72–30 reporting framework explained
NIS2 Directive (EU) 2022/2555 Article 23 establishes a three-stage reporting obligation for significant incidents:
| Stage | Deadline | Required content |
|---|---|---|
| Early warning | 24 hours | Notification that a significant incident has occurred or is suspected; indication of whether it may be cross-border |
| Incident notification | 72 hours | Initial assessment: severity, impact, indicators of compromise |
| Final report | 30 days | Full incident description, root cause, remediation steps, cross-border impact |
Each stage builds on the previous one. If the 24-hour early warning is missed or inaccurate, the 72-hour notification is compromised before it begins.
What constitutes a "significant incident"
Under Article 23(3) of Directive (EU) 2022/2555, an incident is significant if it meets either of two criteria: it has caused (or is capable of causing) severe operational disruption or financial loss to the entity, or it has affected (or is capable of affecting) other persons through considerable material or non-material damage.
The test is disjunctive and forward-looking. An incident that has not yet caused harm but is capable of doing so still triggers the reporting obligation. Organizations cannot wait for damage to materialize before notifying their CSIRT.
For digital service providers — including cloud computing services, managed service providers, DNS providers, and data centers — Commission Implementing Regulation (EU) 2024/2690 adds specific quantitative thresholds on top of the Article 23(3) baseline.
| Classification factor | Threshold for "significant" | Source |
|---|---|---|
| Financial loss | Direct loss exceeding €500K or 5% of annual turnover (whichever is lower) | Implementing Regulation (EU) 2024/2690 |
| Service disruption | Core service unavailable or severely degraded for >30 minutes, or any duration affecting critical infrastructure | Article 23(3) |
| Users affected | Significant proportion of service users, or any impact on other entities' downstream operations | Article 23(3) |
| Data compromise | Unauthorized access to or exfiltration of data capable of causing material harm, including trade secrets | Implementing Regulation (EU) 2024/2690 |
| Cross-border impact | Incident affects or could affect services in more than one Member State | Article 23(3) |
| Threat actor profile | Indicators of APT, state-sponsored activity, or nation-state involvement | ENISA guidance |
| Recurring incident | Any incident that is part of a pattern of repeated events | Implementing Regulation (EU) 2024/2690 |
| Physical harm | Incident capable of causing death or considerable damage to a person's health | Implementing Regulation (EU) 2024/2690 |
Sector authorities may apply stricter thresholds on top of these baselines. Cyprus, for instance, requires early warnings within six hours of detection — well ahead of NIS2's 24-hour requirement. For cloud and SaaS providers, any outage exceeding 10 minutes that affects more than one million users (or more than 5% of the user base) triggers immediate escalation.
The operational challenge is that evaluating these thresholds requires real-time data. Without automated monitoring, a security analyst must manually correlate logs, assess scope, and make a severity judgment — often while the incident is still active. That judgment directly determines whether a reporting obligation is triggered. When in doubt, the regulatory principle is unambiguous: over-reporting carries no penalty, under-reporting does.
The resource and talent gap
The EU cybersecurity skills shortage stands at approximately 299,000 professionals, according to ENISA estimates. That gap has direct operational consequences: 81% of organizations view hiring difficulties as a key factor raising their exposure to cyberattacks.
Understaffed teams cannot sustain manual compliance workflows alongside active threat response. Automation doesn't replace security professionals — it removes the tasks that shouldn't require them in the first place.
How automation directly reduces the reporting burden

Automation's value in NIS2 compliance maps to specific tasks at specific points in the reporting timeline.
Automating the 24-hour early warning
At hour zero, a SIEM (Security Information and Event Management) system correlates incoming log data and fires an alert. At hour two, a SOAR (Security Orchestration, Automation and Response) platform runs an initial severity scoring workflow — pulling asset criticality, affected user count, and threat intelligence context automatically.
By hour four, the system has already drafted an early warning notification template populated with available incident data. The analyst reviews, adjusts, and submits.
Streamlining the 72-hour incident notification
The 72-hour notification requires structured evidence: indicators of compromise, affected systems, preliminary impact assessment. Collecting this manually from disparate log sources (firewalls, endpoints, identity providers, cloud platforms) takes hours and introduces transcription errors.
Automated log aggregation pulls this data into a unified incident record. Evidence collection runs in parallel with response, not after it. Template population tools pre-fill the notification structure with verified data points, leaving analysts to validate rather than compile.
Simplifying the 30-day final report
The final report demands a complete incident timeline, root cause analysis, and documented remediation steps. Automated audit trails capture every system state change, access event, and configuration modification throughout the incident lifecycle — creating a timestamped record that maps directly to the report's required structure.
Continuous compliance monitoring tools track remediation progress against defined controls, flagging incomplete actions before the submission deadline.
The automation toolkit for NIS2 compliance
The core automation stack for NIS2 compliance reporting spans four tool categories: SIEM and SOAR for detection and response, GRC platforms for control management, third-party risk monitoring for supply chain obligations, and credential management solutions for access evidence.
Each addresses a distinct gap in the manual reporting workflow. Credential management is covered in detail in the section below — it closes the audit evidence gap that SIEM and GRC tools leave open: who had access, to what, and when.
One structural risk worth naming upfront: fragmented tooling. Organizations that assemble compliance workflows from disconnected point solutions — a separate SIEM, a standalone GRC spreadsheet, a manual credential inventory — create visibility gaps between systems.
An incident that touches three tools with no shared data model produces three partial records, none of which alone satisfies the evidentiary standard for a NIS2 notification. Integration between tools is what makes the evidence chain coherent.
SIEM and SOAR integration
SIEM platforms provide real-time threat detection by aggregating and correlating event data across the environment. SOAR platforms extend this by automating response workflows, isolating affected systems, notifying stakeholders, and initiating evidence collection without manual intervention. Together, they compress the time between detection and documented early warning from hours to minutes.
GRC platforms
A GRC platform (Governance, Risk, and Compliance) centralize policy management, map controls to regulatory frameworks, and track compliance status continuously. For NIS2, this means maintaining a live view of which Article 21 controls are implemented, which are deficient, and which require immediate attention, without manual spreadsheet maintenance.
Supply chain risk monitoring
NIS2 Article 21(2)(d) explicitly requires organizations to address security in supply chains — including the security practices of direct suppliers and service providers. Manual vendor assessments conducted annually do not satisfy this obligation; the directive presupposes ongoing visibility into third-party risk posture.
Automated third-party risk platforms continuously monitor vendor security configurations, certificate validity, and known vulnerability exposure. When a supplier's security posture degrades — a misconfigured endpoint, an unpatched CVE, a lapsed certification — the platform flags it in real time rather than at the next scheduled review. For organizations with dozens or hundreds of suppliers, this is the only operationally viable approach to Article 21(2)(d) compliance.
What NIS2 Article 29 says about automation
Article 29 of Directive (EU) 2022/2555 establishes supervisory arrangements for essential entities, including the authority of competent authorities to require documented evidence of implemented controls.
ENISA's implementing guidance under the directive recommends automated monitoring and reporting mechanisms as part of a mature NIS2 compliance program. Automation is the operational posture that supervisory scrutiny under Article 29 presupposes.

Managing NIS2 compliance across multiple frameworks? Passwork's audit logs and access control features are built for exactly this kind of regulatory overlap. Explore Passwork
Closing the audit evidence gap with Passwork
NIS2 Article 21 requires organizations to implement technical and organizational measures covering access control, credential management, and multi-factor authentication. The most common audit failure is not missing controls — it is missing evidence that those controls operate continuously.
Why credential management is a NIS2 priority
Compromised credentials remain the most common initial access vector in confirmed breaches. Every credential compromise that escalates to a reportable incident traces back to an access control failure — an over-privileged account, a shared password, an unrotated service credential.
The directive is explicit on this point. Article 21(2)(i) of NIS2 Directive (EU) 2022/2555 lists among mandatory cybersecurity risk-management measures: "human resources security, access control policies and asset management." The requirement exists precisely because identity is where most incidents begin — and regulators know it.
The Commission's Implementing Regulation (EU) 2024/2690, which specifies technical and methodological requirements under Article 21, reinforces this directly:
"The relevant entities should establish a policy on the security of network and information systems as well as topic-specific policies, such as policies on access control, which should be coherent with the policy on the security of network and information systems."
Article 21(2)(j) further requires "the use of multi-factor authentication or continuous authentication solutions, secured voice, video and text communications and secured emergency communication systems within the entity." Credential hygiene and access governance are not optional hardening measures.
For a deeper look at how NIS2 password requirements map to Article 21, see the Passwork's dedicated breakdown.
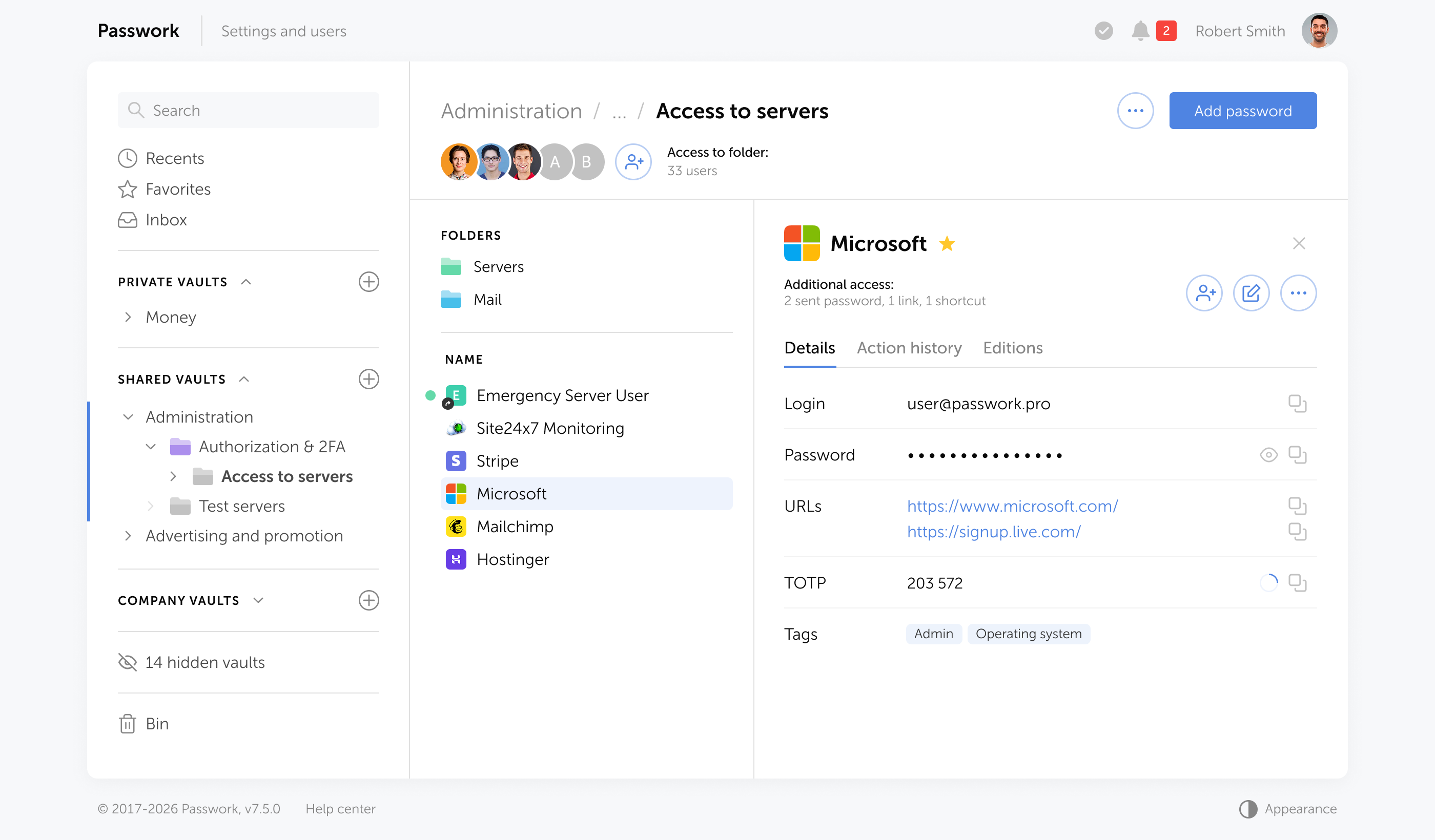
Automated audit trails and immutable logs
Passwork automatically records every password creation, modification, sharing event, and access action — with timestamps, user attribution, and vault context. This activity log is continuous and requires no manual input from administrators. Entries cannot be edited or deleted after the fact, which is what makes the log auditor-reliable.
The regulatory basis for this expectation is clear. Article 21(2)(b) of Directive (EU) 2022/2555 requires entities to implement measures covering "incident handling" — which presupposes the existence of structured, retrievable evidence of what happened, when, and under whose credentials.Without an immutable access log, incident reconstruction is guesswork.
Article 21(2)(f) extends this to "security in network and information systems acquisition, development and maintenance" — covering the systems through which credentials are managed and accessed. Auditors reviewing compliance under this clause will look for evidence that access to sensitive systems was controlled and traceable end-to-end.
The Implementing Regulation (EU) 2024/2690 makes the logging expectation operational: entities must "monitor their network and information systems" and "take actions to evaluate" detected events — a process that is only possible with continuous, structured activity records. Ad hoc or manually assembled logs do not satisfy this standard.
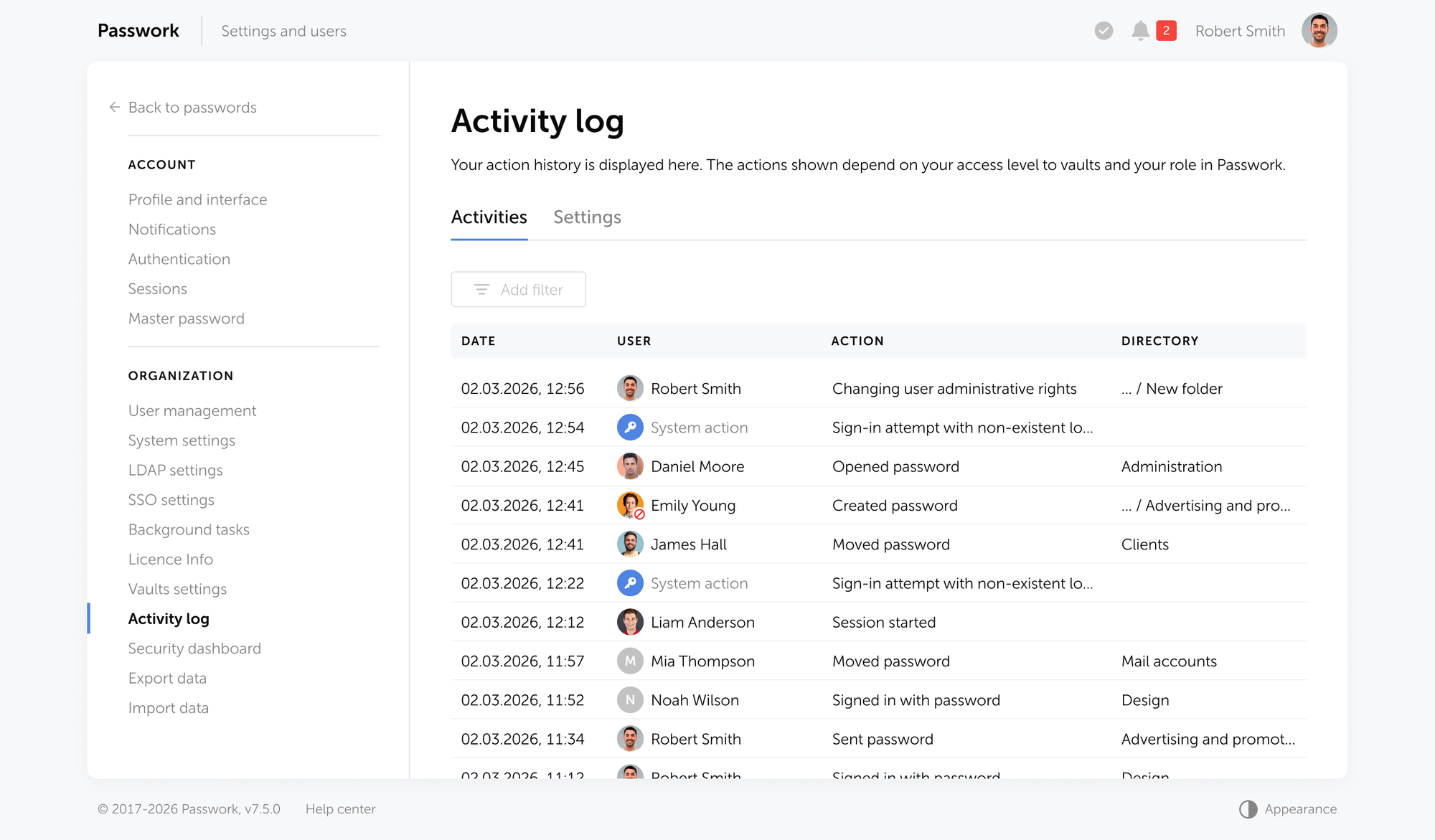
ENISA's guidance on NIS2 implementation further emphasizes that competent authorities, when exercising supervision, will assess whether entities have implemented "technical and methodological requirements" in a documented, verifiable form — meaning audit trails must be exportable and auditor-readable, not merely internally visible.
Passwork's detailed activity reports provide exactly that: a structured, exportable record that maps directly to what regulators ask to see.
Centralized access control and AD/LDAP integration
Centralized access control is an approach where all permissions to systems, credentials, and resources are managed from a single administrative layer — rather than configured separately across individual tools or teams. AD/LDAP integration connects that layer directly to the organization's existing directory service (Active Directory or LDAP), so group memberships and role changes in the directory propagate automatically to downstream access policies.
Passwork's role-based access control (RBAC) allows administrators to assign permissions at the individual user or group level, with AD/LDAP integration synchronizing directory groups to Passwork access policies automatically.
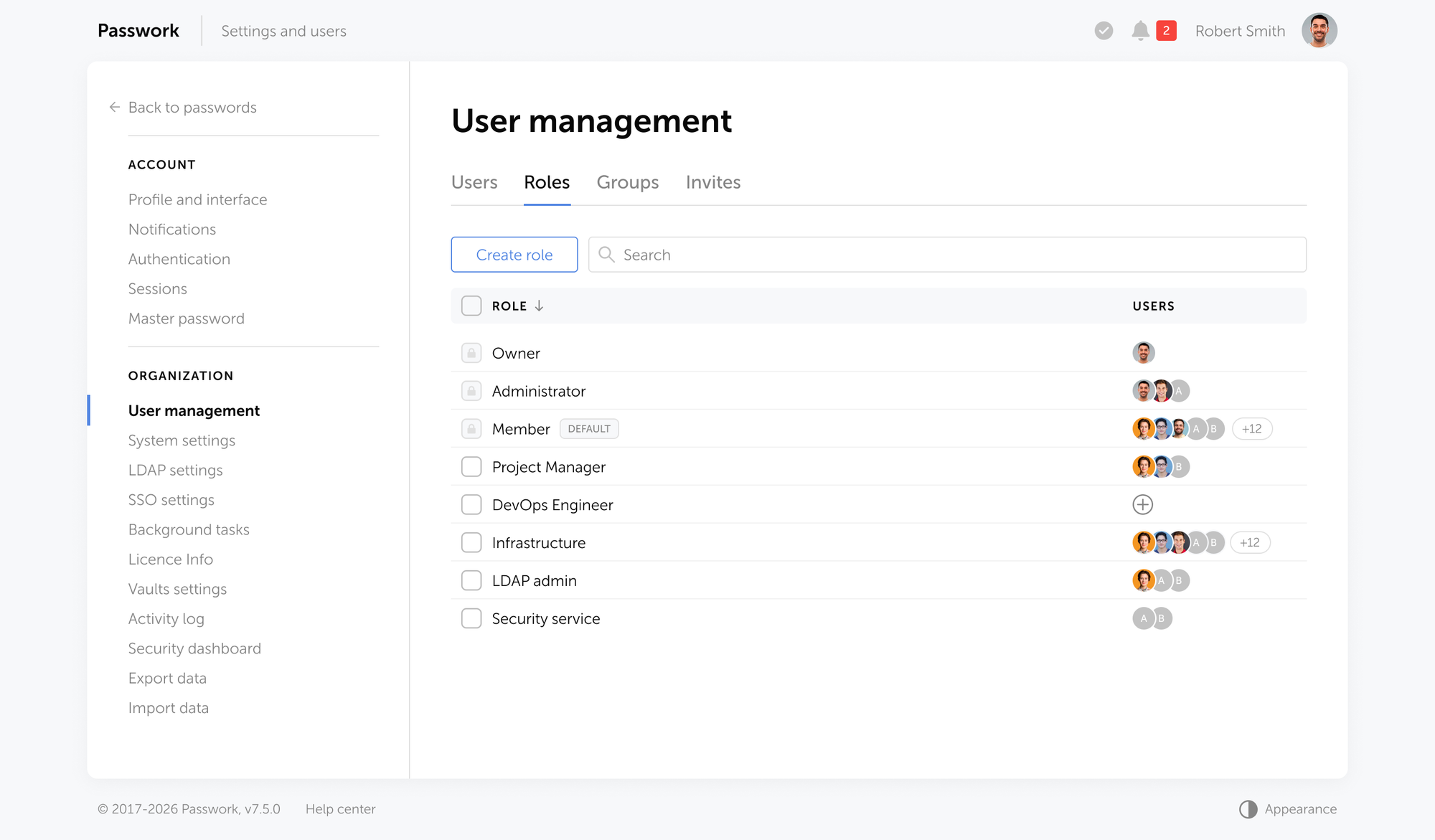
When an employee leaves or changes roles, access is revoked or adjusted through the directory, not through a manual ticket process that may take days.
Relevant entities shall implement access control policies that are coherent with the policy on the security of network and information systems… including identity and access management. — Commission Implementing Regulation (EU) 2024/2690
Passwork's self-hosted deployment model keeps all credential data within the organization's own infrastructure, directly addressing Article 21(2)(i)'s access control requirements and supporting data sovereignty obligations that intersect with GDPR.
Continuous password security analysis
Passwork's security dashboard automatically flags weak, reused, outdated, and compromised credentials across the entire vault. This continuous monitoring posture demonstrates the proactive risk management stance that NIS2 Article 21(2)(a) requires.
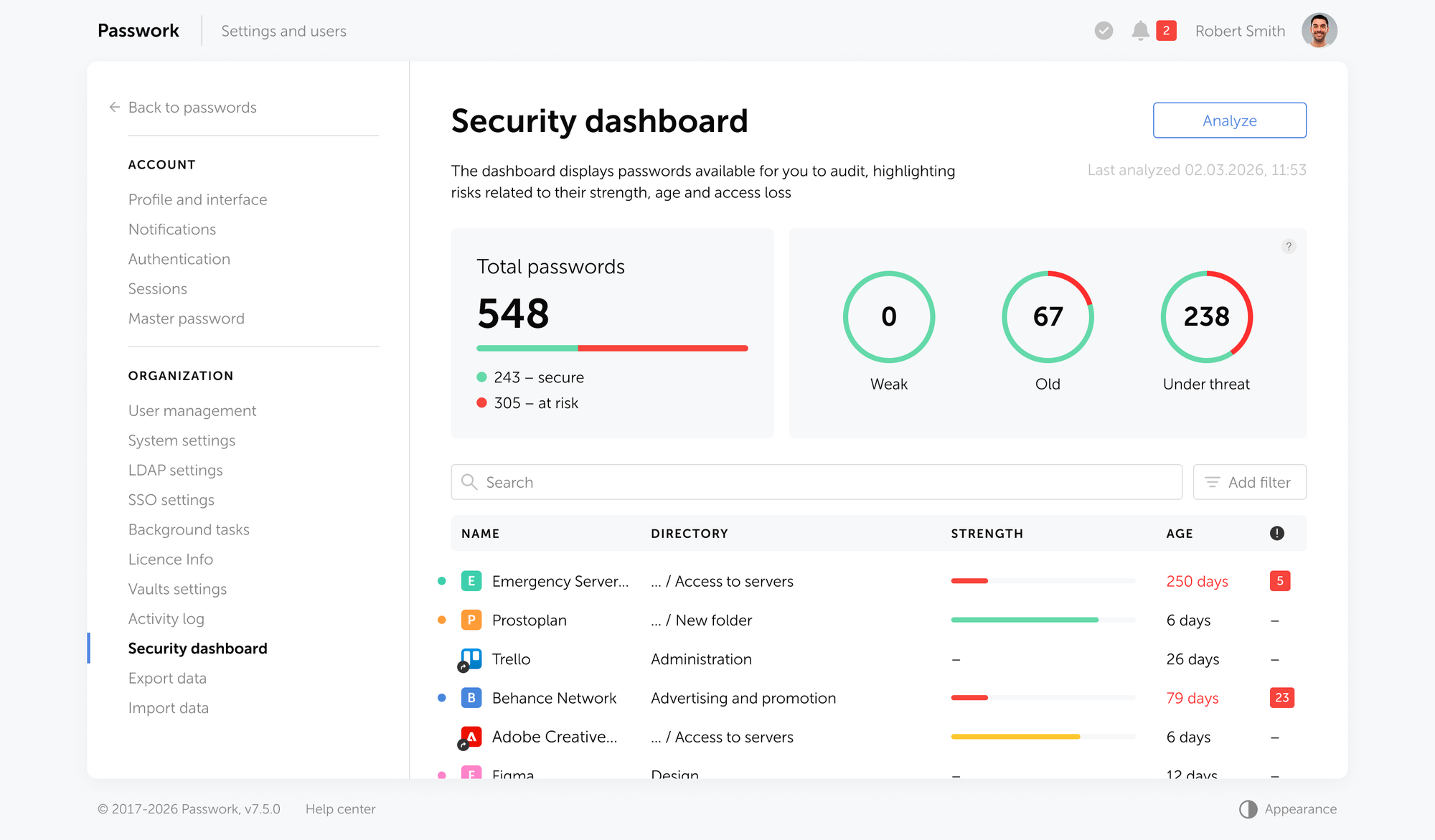
When an auditor asks "how do you know your credential hygiene is maintained?" the answer is a live dashboard and an exportable report.

Passwork provides the audit trail, access control evidence, and credential hygiene reporting that NIS2 Article 21 audits require. See how it works
Quantified benefits of automation for NIS2 compliance
Time savings and cost reduction
Organizations implementing compliance automation report 40–60% lower total compliance costs and up to 80% reduction in audit evidence collection time, according to Forrester research. For a compliance team spending 200 hours preparing for a single audit cycle, that reduction translates directly into capacity for other work.
The global average cost of a data breach stood at $4.44 million in 2025. Organizations with extensive security AI and automation saved an average of $1.9 million per breach compared to those without — and contained breaches 80 days faster. In breach scenarios, average savings from security automation exceed typical implementation costs.
Accuracy and audit readiness
Manual data collection introduces transcription errors, version conflicts, and documentation gaps. Automated evidence collection eliminates these failure modes by pulling data directly from source systems — ensuring that what auditors receive matches what actually happened.
Scalability across multi-framework compliance
NIS2 controls overlap significantly with DORA (Digital Operational Resilience Act), GDPR Article 32, and ISO/IEC 27001. Automating for NIS2 — particularly around audit trails, access control, and incident documentation — builds a compliance infrastructure that serves multiple frameworks simultaneously. The investment compounds.
Modern GRC platforms formalize this overlap through multi-framework compliance orchestration: a single control mapped once, evaluated continuously, and reported against NIS2, GDPR, and ISO 27001 simultaneously.
Without this, compliance teams maintain parallel documentation sets for each framework — a structural inefficiency that multiplies audit preparation time and introduces version conflicts between frameworks. Organizations subject to both NIS2 and DORA, for instance, face near-identical incident reporting obligations; a unified platform handles both from the same evidence base.
Predictive compliance: from reactive to proactive
The next maturity level beyond continuous monitoring is predictive compliance management. AI-driven analytics platforms analyze historical compliance data, control drift patterns, and threat intelligence feeds to surface likely compliance gaps before they materialize into incidents or audit findings.
For NIS2, this means identifying which controls are trending toward deficiency — an access policy not reviewed in 11 months, a credential set approaching its rotation threshold, a supplier whose security score has declined over three consecutive assessments — and flagging them before a regulator does. The shift from reactive remediation to proactive prevention is where automation stops being a reporting tool and starts being a risk management capability.
Automation + human oversight: Finding the right balance

What should be fully automated
The following tasks are appropriate for full automation: log collection and aggregation, initial severity scoring, evidence compilation, notification template population, continuous credential monitoring, access provisioning and deprovisioning via directory integration, and compliance status dashboards.
These are high-volume, time-sensitive, and error-prone when done manually. Automation handles them faster and more consistently than any team.
What must remain human-led
Strategic decisions cannot be delegated to automated systems. Final sign-off on incident notifications, board-level communication, root cause determination, public disclosure decisions, and regulatory negotiation all require human judgment, accountability, and legal authority.
The goal is not to remove humans from the compliance process — it is to ensure humans are spending their time on decisions only they can make.
Implementation roadmap: Getting started with NIS2 reporting automation
Step 1 — Gap assessment and tool selection
Map your current incident detection, documentation, and reporting workflows against the 24-72-30 timeline. Identify where manual steps create the highest delay or error risk. Select tools — SIEM, SOAR, GRC, PAM (Privileged Access Management), credential management — based on integration capability with your existing stack, not feature lists alone.
Step 2 — Integration and workflow design
Connect tools to data sources: endpoints, identity providers, network infrastructure, cloud platforms. Design automated workflows for each reporting stage — what triggers the early warning draft, what populates the 72-hour notification, what feeds the final report. Test each workflow against a simulated incident before go-live.
Step 3 — Testing and continuous improvement
Run tabletop exercises using the automated workflows. Measure time-to-early-warning, evidence completeness, and notification accuracy. Treat each drill as a calibration event — adjust thresholds, templates, and escalation paths based on results. NIS2 compliance is not a project with an end date; it is an operational capability that requires ongoing refinement.

Credential data stays where your policy says it should. Passwork's self-hosted deployment keeps your vault within your own infrastructure — no third-party cloud, no data residency ambiguity, full alignment with GDPR Article 32 obligations. If you're evaluating hosting models for your organization, read our breakdown of self-hosted vs. cloud password manager deployment — and what each means for NIS2 compliance. Read the guide
Conclusion

NIS2's 24–72–30 reporting framework is not designed for manual workflows. The directive sets deadlines that assume continuous monitoring, structured evidence, and documented controls — not spreadsheets assembled under pressure while an incident is still active.
The operational argument for automation is straightforward: at 24 hours, a team that has already aggregated logs, scored severity, and pre-populated a notification template is compliant. A team starting from scratch is not. That gap is a process design problem that technology solves.
Credential governance under Article 21 is a documented obligation — and the evidence that regulators will ask for maps directly to the access control failures where most incidents begin. Audit trails, RBAC, MFA enforcement, and continuous password security monitoring are evidence.
Three things determine whether an organization meets NIS2 reporting obligations under pressure: the speed of detection, the quality of automated evidence collection, and the completeness of access control documentation. Each is addressable with the right tooling. None is addressable with good intentions and a capable team alone.
The organizations that will meet the 24-hour deadline consistently are the ones that built the capability before the incident — not the ones that planned to.

Passwork gives security teams the audit trail, access control documentation, and credential monitoring that NIS2 Article 21 requires. See how Passwork fits into your compliance infrastructure: passwork.pro
Frequently asked questions

What are the NIS2 incident reporting requirements?
NIS2 Article 23 requires essential and important entities to submit a three-stage report for significant incidents: an early warning within 24 hours, an incident notification within 72 hours, and a final report within 30 days. Each stage has specific content requirements covering incident scope, severity, impact, and remediation measures.
How long do organizations have to report a NIS2 incident?
Organizations must submit an early warning within 24 hours of becoming aware of a significant incident. A more detailed incident notification follows within 72 hours. A comprehensive final report — including root cause analysis and remediation steps — is due within 30 days of the initial notification.
What is a "significant incident" under NIS2?
Under Article 23(3), an incident is significant if it causes severe operational disruption, financial loss, or material damage to other entities. ENISA technical guidance adds quantitative thresholds based on the number of affected users, service downtime duration, and geographic scope. Determining significance requires real-time data — which is why automated monitoring is critical.
How can automation help with NIS2 compliance reporting?
Automation compresses the time between incident detection and regulatory notification by handling log aggregation, severity scoring, evidence collection, and template population without manual intervention. It also maintains continuous audit trails and compliance monitoring, ensuring organizations are always in a reportable state rather than scrambling to reconstruct evidence after an incident.
How does a password manager like Passwork help with NIS2 compliance?
Passwork addresses NIS2 Article 21 requirements by providing automated audit logs of all credential access and modification events, role-based access control with AD/LDAP integration, continuous password security analysis, and a self-hosted deployment model that keeps credential data within the organization's infrastructure. These features produce the documented evidence that auditors require under Article 21(2)(b), (f), and (i).
What happens if you miss the NIS2 24-hour reporting deadline?
Missing the 24-hour early warning deadline exposes essential entities to supervisory action by national competent authorities, including binding instructions, fines, and — for essential entities — potential temporary suspension of management functions. Fines under NIS2 reach €10 million or 2% of global annual turnover for essential entities.
What is the difference between NIS2 essential and important entities?
Essential entities operate in high-criticality sectors listed in Annex I of the directive — energy, banking, healthcare, digital infrastructure, and others — and face proactive, regular supervision. Important entities fall under Annex II sectors (postal services, food production, waste management, etc.) and are subject to reactive supervision. Both categories must meet identical technical requirements under Article 21 and the same incident reporting obligations under Article 23.
Table of contents
- Itroduction
- Key takeaways
- The reality of the NIS2 reporting burden
- How automation directly reduces the reporting burden
- The automation toolkit for NIS2 compliance
- Closing the audit evidence gap with Passwork
- Quantified benefits of automation for NIS2 compliance
- Automation + human oversight: Finding the right balance
- Implementation roadmap: Getting started with NIS2 reporting automation
- Conclusion
- Frequently asked questions
Table of contents
- Itroduction
- Key takeaways
- The reality of the NIS2 reporting burden
- How automation directly reduces the reporting burden
- The automation toolkit for NIS2 compliance
- Closing the audit evidence gap with Passwork
- Quantified benefits of automation for NIS2 compliance
- Automation + human oversight: Finding the right balance
- Implementation roadmap: Getting started with NIS2 reporting automation
- Conclusion
- Frequently asked questions
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more
