
April 18, 2026 — Belgium's first NIS2 enforcement deadline. Essential entities were required to submit verified documentation confirming that cybersecurity controls are in place, assessed by an accredited body or the Centre for Cybersecurity Belgium directly. Self-declarations were not accepted.
22 of 27 member states have completed NIS2 transposition. Enforcement is active in Germany, France, and the Netherlands — regulators are auditing, and fines are being applied.
Meanwhile, 84% of organizations facing active enforcement are, by their own admission, not ready — according to CyberSmart's April 2026 survey of 670 in-scope business leaders across eight countries. That number has not moved meaningfully in six months.
This article covers where enforcement stands today, what is coming next, and what IT and security leaders need to address before the next deadline arrives.
Key takeaways
- Belgium set the first deadline. On April 18, 2026, essential entities were required to submit verified self-assessments via CyberFundamentals (CyFun), ISO/IEC 27001, or direct CCB inspection.
- Readiness remains critically low. Only 16% of businesses feel fully prepared, yet 75% see compliance as a competitive advantage. The gap is execution: budget constraints, missing implementation guidance, and supply chain blind spots are the real blockers.
- Poland expanded scope to 42,000 organizations. The amended KSC Act entered into force on April 3, 2026, adding food production, waste management, and other sectors. The official entity list launched April 13, 2026.
- Supply chain risk is the hardest gap to close. Only around 1 in 10 businesses were adequately assessing their suppliers' security posture as recently as 2024 (UK NCSC). NIS2 Article 21 requires documented third-party security obligations and continuous monitoring.
- Board liability is personal. NIS2 Article 20 makes management bodies directly accountable for approving cybersecurity measures and completing relevant training. In Germany, individual managers face fines of up to €500,000 for governance failures — separate from organizational penalties.
- The UK is building a stricter parallel regime — and multinationals must track both. The UK Cyber Security and Resilience Bill introduces two-tier penalties (up to £17M or 4% of global turnover for serious failures), direct MSP regulation, and a broader incident definition that captures potential incidents — not just confirmed ones. A single NIS2 compliance strategy is not sufficient for cross-border operations.
- The controls auditors examine first are also the fastest to implement. Access management, credential policies, and MFA are explicitly required under Article 21 — and they generate the audit trail that satisfies both Article 21 and Article 20 board oversight requirements.
What is NIS2 and who does it cover

NIS2 (Directive EU 2022/2555) is the EU's updated legal framework for network and information security. It replaces the original NIS Directive and expands both the scope of covered entities and the severity of obligations. The directive applies to medium-sized and larger organizations across 18 critical sectors.
You organisation is covered by the NIS2 directive if:
- It operates in a sector listed in Annex I or Annex II of the directive
- It meets the size threshold — at least 50 employees, or an annual turnover and/or annual balance sheet total exceed €10 million (Annex to Recommendation 2003/361/EC)
- It is identified as a critical entity under Directive (EU) 2022/2557 (CER Directive), regardless of its size
Once your organisation is confirmed in scope, its classification as an essential or important entity depends on two factors: the annex your sector falls under, and your organisation's size.
| Essential entity | Important entity | |
|---|---|---|
| Annex | Annex I (high criticality sectors) | Annex II (other critical sectors) |
| Size | Large: ≥ 250 employees, or turnover > €50M, or balance sheet > €43M | Medium: 50–249 employees, or turnover / balance sheet €10–50M |
| Supervision | Proactive, ex-ante — audits and inspections without prior incident | Reactive, ex-post — triggered by incidents or complaints |
| Max fine | €10 million or 2% of global annual turnover | €7 million or 1.4% of global annual turnover |
| Examples | Energy grid operators, hospitals, cloud providers, banks | Food manufacturers, postal services, online marketplaces, chemical producers |
Some organisations fall within NIS2 scope regardless of size:
- A provider of public electronic communications networks or publicly available electronic communications services
- A trust service provider
- A top-level domain (TLD) name registry or DNS service provider
- The sole provider of a service in a Member State that is essential for the maintenance of critical societal or economic activities
- An entity whose disruption could have a significant impact on public safety, public security, or public health
- An entity whose disruption could induce a significant systemic risk, in particular for sectors where such disruption could have a cross-border impact
If your organisation belongs to a larger corporate group, headcount and financials must be aggregated across linked entities — a subsidiary with 40 employees may still be in scope if the parent group exceeds the thresholds.
As of March 2026, 22 of 27 EU member states have adopted national implementing legislation. France, Ireland, Luxembourg, the Netherlands, and Spain remain in the legislative process, according to Skadden's March 2026 analysis.
Top story: Belgium's April 18 deadline

On April 18, 2026, Belgium hit the NIS2 conformity assessment deadline. Essential entities were required to demonstrate active implementation of cybersecurity risk-management measures and submit supporting evidence to the Centre for Cybersecurity Belgium (CCB) — via one of three recognised compliance pathways:
- CyberFundamentals (CyFun®): Obtain at least a Basic or Important verification, or hold a signed agreement with an accredited assessment body.
- ISO/IEC 27001: Submit the certification scope, Statement of Applicability (SoA), and the most recent internal audit report. Full certification must be completed by April 2027.
- Direct inspection: Provide a self-assessment with supporting documentation and formally request a CCB inspection — a pathway that may lead directly to supervisory measures.
Self-attestation alone is not accepted. Failure to submit complete and timely documentation may result in administrative measures, financial penalties, and further supervisory action.
The pattern Belgium has set (formal third-party assessment, documented evidence, management sign-off, personal liability) is the template the rest of the EU is following.
The NIS2 readiness gap: 84% of businesses are not ready
16% of European businesses required to comply with NIS2 feel fully prepared while 11% of in-scope organizations are still unsure what NIS2 is. These figures come from CyberSmart's survey of 670 business leaders across the UK, Poland, the Netherlands, Ireland, France, Germany, Italy, Denmark, and Belgium, conducted in late 2025 — all from organizations within NIS2's scope.
The problem is execution
The obvious assumption that businesses simply aren't taking NIS2 seriously doesn't hold up. 75% of respondents see at least some competitive advantage in compliance, and 27% consider that advantage significant. The top concerns around non-compliance were operational and reputational.
| Fear of non-compliance | Share of respondents |
|---|---|
| Loss of productivity | 18% |
| Reputational loss | 18% |
| Loss of customers | 18% |
| Fines | 16% |
| High legal and remediation costs | 16% |
| Business interruption | 15% |
| Legal repercussions | 14% |
| Investor or stakeholder loss of confidence | 14% |
Only 3% of respondents said they have no concerns about the repercussions of non-compliance at all.
Why organizations are falling short
When asked why they hadn't fully complied, respondents gave consistent answers across every region surveyed. The barriers are practical:
| Barrier | Share of respondents |
|---|---|
| Budget constraints | 20% |
| Lack of guidance on how to implement | 16% |
| Lack of internal expertise and resources | 14% |
| Unsure what NIS2 is or how to comply | 11% |
| Unable to assess supply chain risk | 10% |
Budget is the leading obstacle but it signals something deeper. For a portion of organizations, NIS2 compliance is still not treated as a non-negotiable budget line. The guidance gap is equally telling: 16% lack implementation direction, and 11% are unsure what NIS2 requires of them despite being legally obligated to comply.
Supply chain risk compounds the challenge. Only around 1 in 10 businesses were adequately assessing their suppliers' security measures as recently as 2024, according to the UK's NCSC — and 10% of survey respondents cited inability to assess their full supply chain as the primary reason for non-compliance.
What organizations are actually doing
The picture is one of partial progress. Common security protocols (training, encryption, risk assessments) are being applied, often independently of NIS2. The more demanding requirements (supply chain assessment, formal gap analysis, MFA enforcement) lag significantly behind.
| Measure implemented | Share of respondents |
|---|---|
| Mandatory cybersecurity training for employees | 44% |
| Data encryption | 37% |
| Regular risk assessments (planned) | 35% |
| Secure backups and disaster recovery | 34% |
| Incident response plan | 31% |
| Corporate accountability established | 31% |
| Incident reporting procedure | 30% |
| Timely patching and updates | 26% |
| NIS2 gap analysis conducted | 26% |
| Supply chain assessed | 23% |
| MFA enforced | 23% |
| Regular penetration testing (planned) | 20% |
| None of the above | 2% |

MFA enforcement and access control are among the least-implemented NIS2 measures — yet they're the first thing auditors check. See how Passwork handles credential governance
Regulatory fatigue is real
Organizations operating in the EU can simultaneously face obligations under NIS2, GDPR, DORA, the EU Cybersecurity Act, and ISO 27001. These frameworks overlap significantly, but navigating them still requires time, expertise, and resources that most organizations don't have in-house.
| Regulation | Share of respondents subject to it |
|---|---|
| NIS2 | 42% |
| EU Cybersecurity Act | 34% |
| GDPR | 30% |
| ISO/IEC 27001 | 27% |
| EU Cyber Resilience Act | 24% |
| NIST Cybersecurity Framework | 21% |
| DORA | 12% |
| PCI DSS | 11% |
42% of respondents say there are too many regulations to comply with, 35% say too many overlap, and 27% feel there is too much emphasis placed on them.
Compliance is now a commercial requirement
Regulators are not the only ones demanding proof. Market pressure is building from every direction:
- 42% have been asked to prove NIS2 compliance by partners
- 41% have been asked by investors
- 36% have been asked by customers or prospects
NIS2 is still a relatively new standard. As more organizations embed it into supplier and partner due diligence, demonstrating compliance will shift from exceptional to routine. It is already a condition of doing business in many sectors.
Regional highlights
The survey reveals meaningful differences across markets:
- Poland stands out as the strongest compliance culture: not a single Polish respondent reported spending 5% or less of their IT budget on security. The board or C-suite is responsible for compliance in the majority of Polish organizations.
- Benelux shows a disconnect: CEOs are most commonly accountable (43%), yet 10% of businesses are underspending on security — the joint-highest rate in the survey.
- Germany, France and Italy show the highest regulatory fatigue: 44% say there are too many regulations, 39% say they overlap too much.
- Denmark records the highest regulatory skepticism: 34% do not see a competitive advantage in compliance, and 55% say there are too many regulations — the highest figure across all regions surveyed.
- UK and Ireland show investor pressure as a particularly strong driver: 58% of businesses in the region have been asked by investors to prove NIS2 compliance, compared to 41% across all regions.
The EU vs. UK regulatory divergence: What multinationals must know

For organizations operating across both the EU and the UK, NIS2 compliance is only part of the picture. The UK is advancing its own Cyber Security and Resilience Bill — which passed its second reading in January 2026 and has been progressing through committee stage since February — proposes significant amendments to the NIS Regulations 2018.
The two frameworks share common objectives but differ in ways that make a single compliance strategy insufficient.
Key differences between NIS2 and the UK Bill
| Dimension | NIS2 (EU) | UK Cyber Security & Resilience Bill |
|---|---|---|
| Sector scope | 18 sectors including public administration, space, food, manufacturing | Essential services + digital services + new data centre category |
| MSP regulation | Indirect, via supply chain obligations | Direct — Relevant Managed Service Providers (RMSPs) are a new regulated category |
| "Critical suppliers" | Not directly regulated | Designated competent authorities can directly designate critical suppliers |
| Standard fine | €10M or 2% global turnover | £10M or 2% global turnover |
| Higher fine tier | N/A (single tier) | £17M or 4% global turnover for serious failures (security breaches, notification failures) |
| Customer notification | Not required | Required for data centres, RDSPs, and RMSPs after incidents |
| Incident definition | Actual adverse effect | Actual or potential adverse effect — broader scope of reportable incidents |
Two-tier penalties — stricter than NIS2
The UK Bill introduces a two-tier penalty structure: a standard maximum of £10M or 2% of global turnover for less serious failures, and a higher maximum of £17M or 4% of global turnover for serious failures — including security breaches and incident notification failures.
Regulators can additionally impose daily fines of up to £100,000 for ongoing non-compliance. This exceeds NIS2's single-tier structure.
Direct MSP regulation: closing a gap NIS2 left open
The Bill directly regulates managed service providers — a gap in NIS2 that the UK is explicitly addressing. An estimated 900 to 1,100 MSPs will come under direct ICO oversight as Relevant Managed Service Providers (RMSPs), subject to the full suite of obligations including mandatory registration, defined security standards, and incident reporting within prescribed timeframes.
Organizations using external IT providers should be asking those providers how they are preparing.
Broader incident definition
The current NIS Regulations define an incident as any event having an actual adverse effect on security. The Bill broadens this to capture any event having, or capable of having, an adverse effect — meaning organizations must assess and respond to potential incidents, not only confirmed ones. This will materially increase the volume of reportable events.
The UK threat landscape
The regulatory tightening reflects a genuine risk picture. Cyber attacks are estimated to cost UK businesses £14.7 billion annually — equivalent to approximately 0.5% of GDP — based on independent research commissioned by the UK government. The average cost of a significant cyber attack for an individual business is nearly £195,000.
Regulatory fragmentation across EU member states
The divergence is not only between the EU and UK. Despite the October 2024 transposition deadline, NIS2 implementation across the 27 member states remains highly fragmented. Austria's NISG 2026, Poland's KSC Act, and the Dutch Cyberbeveiligingswet each introduce national variations in penalties, enforcement procedures, and sector-specific requirements — creating disproportionate compliance costs for cross-border organizations.
Poland: KSC Act in force, entity list published

Poland's amended Act on the National Cybersecurity System (KSC) entered into force on April 3, 2026. The official list of key and important entities launched on April 13, 2026.
The scale of change is substantial. The previous KSC framework covered approximately 400 entities. The amended law brings an estimated 42,000 organizations into scope — including nearly 28,000 public sector bodies.
New sectors now covered
Five sectors enter Polish cybersecurity law for the first time:
| New sector | Annex |
|---|---|
| Food production, processing and distribution | Annex II |
| Waste management | Annex II |
| Chemical production and distribution | Annex II |
| Postal and courier services | Annex II |
| Manufacturing (medical devices, motor vehicles, electronics) | Annex II |
Poland also expanded several existing sectors beyond the NIS2 baseline — energy now includes coal mining; banking and financial market infrastructure picked up additional entity types. Classification is not always obvious: organizations in newly covered sectors should conduct a preliminary self-assessment before assuming they fall outside scope.
Key compliance deadlines
| Deadline | Obligation |
|---|---|
| April 13, 2026 | Official list of essential and important entities published |
| October 3, 2026 | Registration application deadline |
| April 3, 2027 | Full implementation of all Chapter 3 obligations |
| April 3, 2028 | First information system security audit (essential entities) |
Registration is not automatic — most organizations must self-assess and apply within 6 months of meeting the criteria. Failing to register does not exempt an organization from its obligations; it adds a violation on top.
Netherlands: The Cyberbeveiligingswet is almost in force

The Dutch Cyberbeveiligingswet (Cbw) — the Netherlands' transposition of NIS2 — passed the House of Representatives on April 15, 2026 and is expected to take effect on Q2 2026.
The law introduces four core obligations for all in-scope organizations:
- 10 mandatory duty-of-care measures — risk analysis, access management, MFA, incident response, supply chain security, encryption, and four others. ISO 27001 certification helps but does not constitute full compliance on its own.
- Three-step incident reporting — early warning within 24 hours, follow-up notification within 72 hours, final report within 30 days, all submitted via the NCSC portal.
- Personal board liability — governing bodies must formally approve cybersecurity measures, oversee implementation, and complete cybersecurity training. Delegating entirely to IT without active oversight creates direct personal exposure.
Fines reach up to €10M or 2% of global turnover for essential entities, and €7M or 1.4% for important entities.
Most organizations need four to six months to reach the required compliance level. Those that haven't started a gap analysis yet are running out of time.
Board liability: Article 20 makes it personal

NIS2 Article 20 makes management bodies directly and personally accountable for cybersecurity governance. Three layers of exposure apply:
- Approval liability. Management bodies must formally approve cybersecurity risk-management measures. If those measures prove inadequate and lead to an incident, the approval decision and the people who made it will be examined by regulators.
- Training liability. Article 20(2) requires executives to complete cybersecurity training sufficient to identify risks and assess risk-management practices. Ignorance of technical details is no longer a defensible position.
- Oversight liability. Delegating entirely to IT or a third-party MSSP without maintaining governance oversight creates direct personal exposure. In Germany, individual managers face fines of up to €500,000 for governance failures — separate from any organizational penalty. Directors can also be temporarily banned from management roles for serious negligence.
KPMG Law's April 2026 analysis of the German implementation confirms this is not theoretical. MSI Global Alliance frames the shift plainly: cybersecurity now sits at the same governance level as financial reporting. Directors are responsible for their organization's cybersecurity posture, with obligations including documented risk management policies and demonstrable oversight of third parties.
How Passwork supports NIS2 compliance
The fastest way to close the most common NIS2 gaps is to bring access under control. Article 21 of the directive explicitly requires organizations to implement access management policies, enforce strong authentication, and maintain documented audit trails. These are also the controls regulators examine first and the ones most organizations still handle manually or inconsistently.
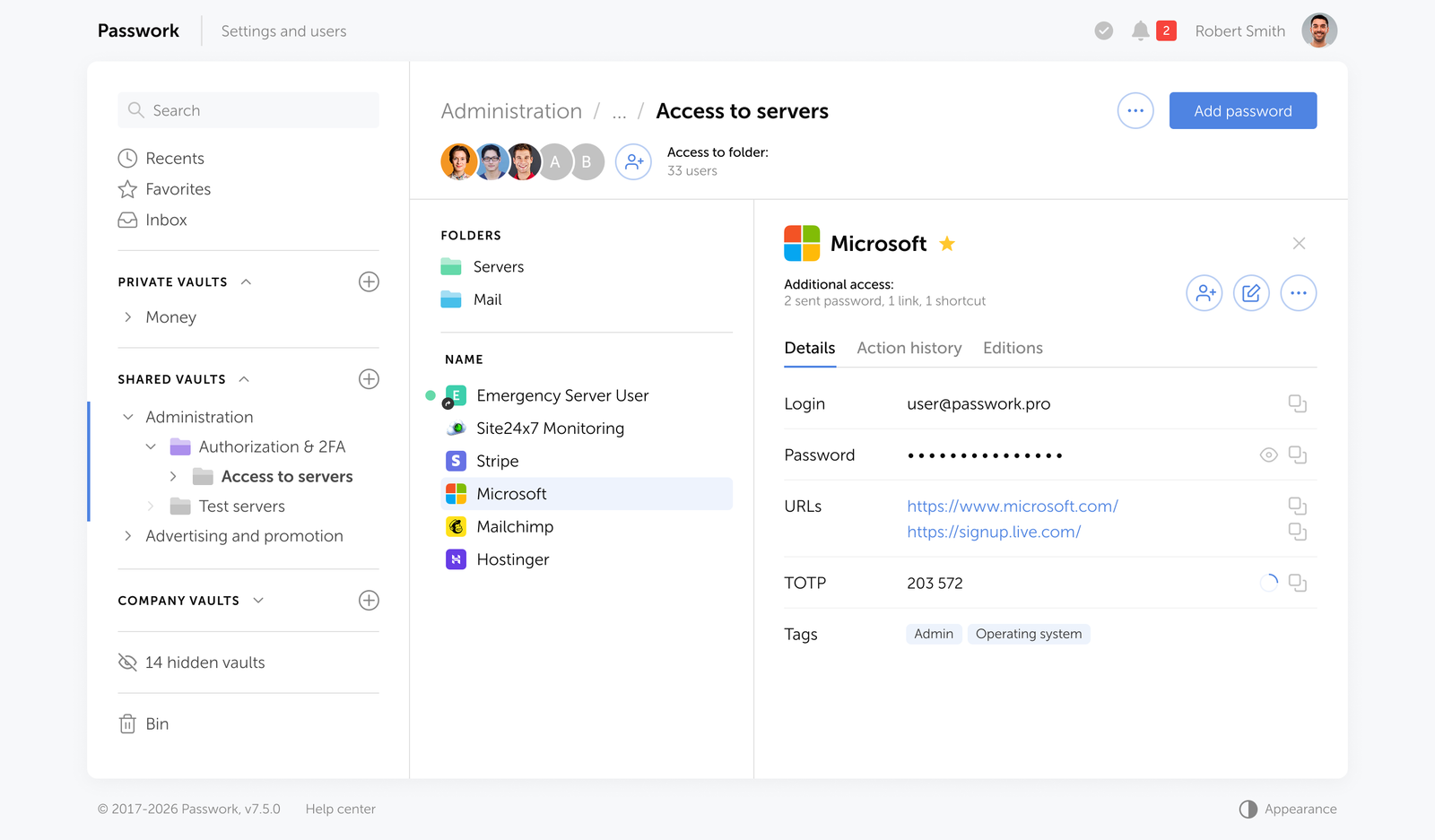
A password manager addresses this directly. It centralizes credential storage, enforces role-based access policies, and creates a verifiable record of who accessed what and when — the kind of evidence auditors expect to see.
Access management and audit trails
Passwork offers structured, role-based access control across all shared credentials. Admins assign permissions at the vault, folder, and individual password level. Every access event — view, copy, edit, share, deletion — is logged with a timestamp and user identity.
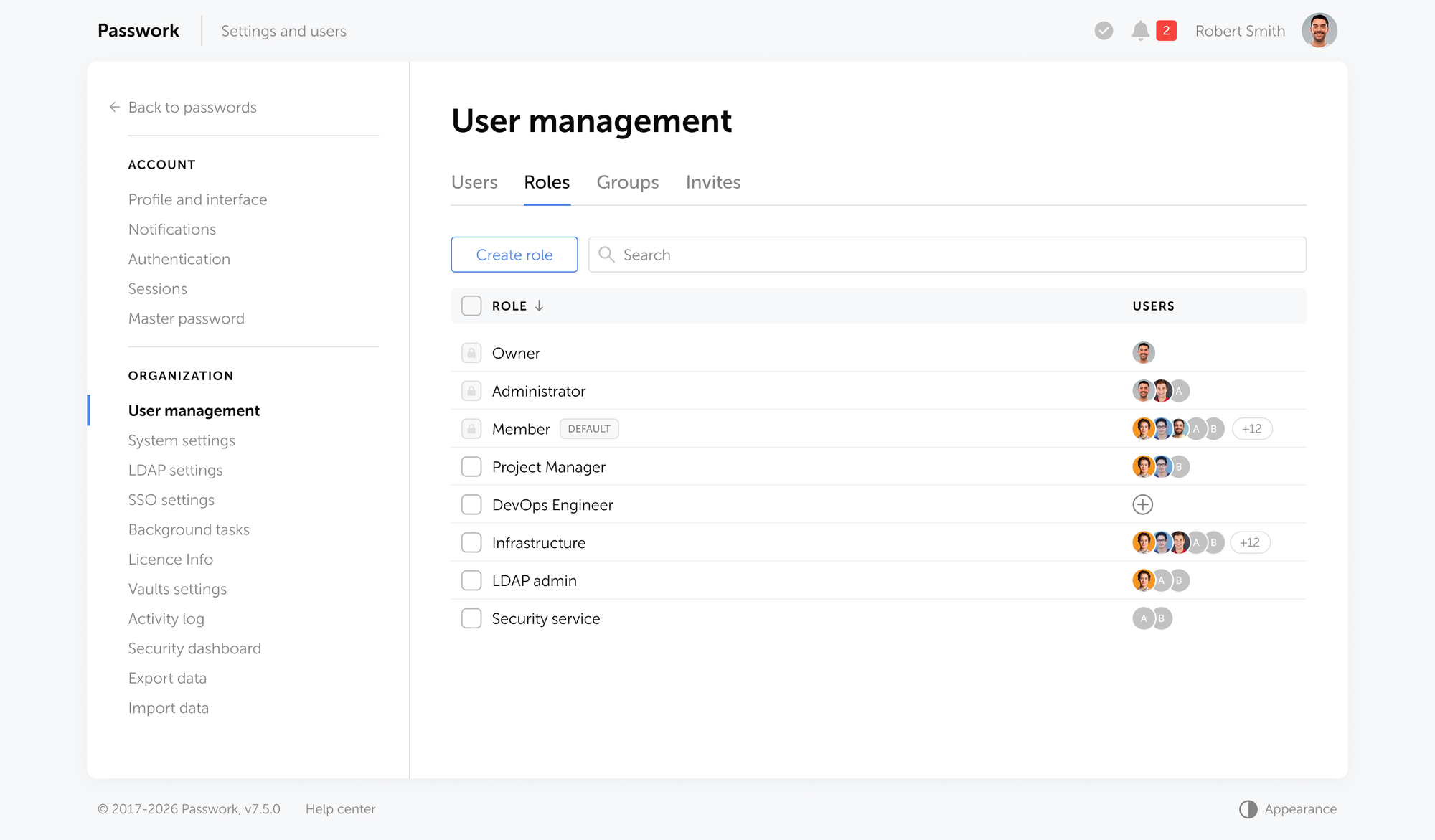
This audit trail is directly relevant to NIS2 Article 21(2)(i), which requires organizations to implement "policies and procedures regarding the use of cryptography and, where appropriate, encryption" and to maintain access controls over sensitive systems. When a regulator asks for evidence of access governance, a complete, searchable log is the answer.
Continuous monitoring
NIS2 requires ongoing security monitoring. Passwork supports this through a real-time activity feed and configurable notifications for any credential event: a password viewed by an unexpected user, a shared vault accessed outside working hours, a privileged account modified without a change ticket.
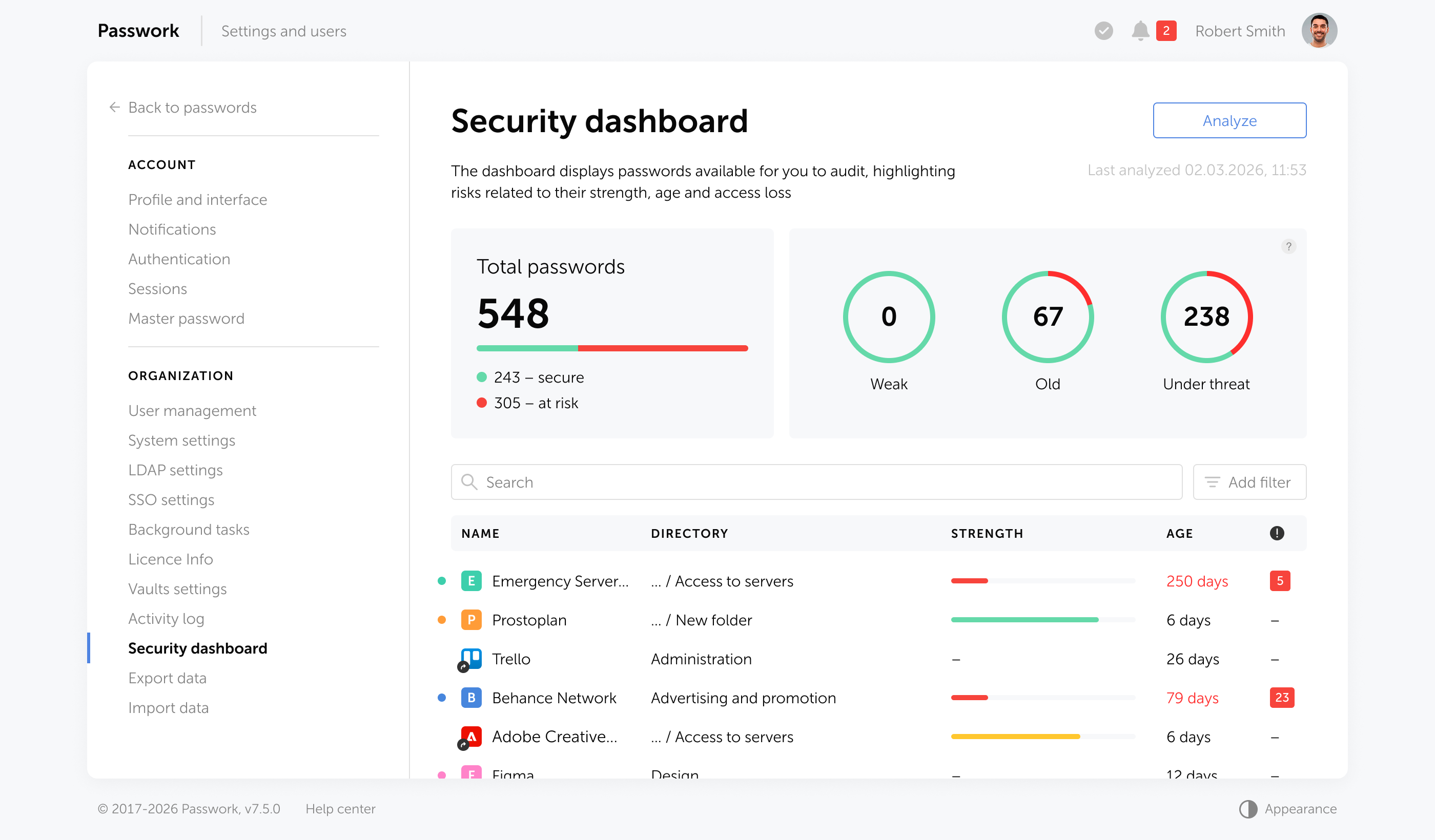
The password security dashboard flags weak, reused, outdated, and potentially compromised credentials across the entire organization — giving security teams continuous visibility without manual auditing.
ISO 27001 certified and continuously tested
Passwork holds ISO/IEC 27001 certification — the same standard Belgium accepts as a NIS2 compliance pathway under its CyFun framework. The certification confirms a systematic, auditable approach to information security management
For organizations that need to demonstrate security posture to regulators, partners, or customers, Passwork's ISO 27001 certification provides independently verifiable evidence.
Self-hosted deployment
Passwork deploys entirely within your own infrastructure. All data is encrypted with AES-256 and never leaves your servers. There is no dependency on third-party cloud services — which matters both for NIS2 compliance and for the supply chain risk provisions that require organizations to assess the security of their service providers.
The source code is auditable. Your security team can verify there are no hidden vulnerabilities before deployment.

Passwork gives your team structured access control, a full audit log, and continuous credential monitoring — all within your own infrastructure. See how Passwork supports NIS2 compliance
Compliance calendar
The following table outlines the key compliance events, sorted chronologically. Uncertain or estimated dates are flagged accordingly.
| Date | Event |
|---|---|
| April 18, 2026 | Belgium: NIS2 conformity assessment deadline for essential entities to demonstrate CyFun Basic/Important verification or ISO 27001 documentation. |
| May 6, 2026 | Poland: Deadline for the Minister of Digital Affairs to automatically add existing key service operators to the official list of key and important entities (Wykaz KSC). |
| June 11, 2026 | EU: Cyber Resilience Act (CRA) framework on notification of conformity assessment bodies starts to apply. | Mid 2026 (expected) | Germany: BSI registration opens for newly qualifying critical entities under the KRITIS-Dachgesetz. |
| July 1, 2026 (expected) | Netherlands: Cyberbeveiligingswet (NIS2 implementation) and Wet weerbaarheid kritieke entiteiten (CER implementation) expected to enter into force. |
| July 17, 2026 | Germany: First registration deadline for critical entities under the KRITIS-Dachgesetz with the Federal Office of Civil Protection and Disaster Assistance (BBK). |
| July 17, 2026 | Belgium: Important entities automatically considered as critical entities pursuant to the law on the resilience of critical entities. |
| July 2026 (expected) | France: Expected parliamentary vote on the "Loi résilience des infrastructures critiques et renforcement de la cybersécurité" (ReCyF) for NIS2 and CER implementation. |
| August 2, 2026 | EU: Main provisions of the Artificial Intelligence Act apply, including obligations for operators of high-risk AI systems and full enforcement powers for the AI Office. |
| August 18, 2026 | EU: E-Evidence Regulation (EU 2023/1543) becomes applicable, enabling authorities to directly order service providers to produce or preserve electronic evidence within 10 days. |
Conclusion

Belgium's April 18 deadline has passed. It will not be the last. Regulators across 27 member states are moving from guidance to audits, and the 16% readiness figure means the vast majority of in-scope organizations are exposed right now.
The pattern is consistent across every early enforcement action: the controls regulators examine first are access management, privileged credential governance, and audit trails. These are not the hardest requirements in NIS2 — they are the most concrete, the most documentable, and the most immediately actionable.
Getting access under control is the fastest way to close the most auditable compliance gaps. It satisfies Article 21 requirements directly, supports supply chain oversight, and generates the evidence trail that Article 20 board liability demands. A password manager with role-based access, a complete audit log, and continuous monitoring addresses all three.
Passwork is ISO/IEC 27001 certified and deploys entirely within your own infrastructure. It was designed for exactly the kind of access governance NIS2 auditors look for.

Passwork is a self-hosted password manager built for businesses. It enforces role-based access policies, maintains a complete audit log of all credential activity, and deploys entirely within your own infrastructure. Try Passwork in your infrastructure
Frequently Asked Questions

What is the NIS2 Directive and who does it apply to?
NIS2 (Directive EU 2022/2555) is the EU's legal framework for network and information security, replacing the original NIS Directive from 2016. It applies to medium and large organizations in 18 critical sectors — including energy, healthcare, finance, transport, digital infrastructure, and manufacturing — with at least 50 employees or €10 million in annual turnover or balance sheet total.
What are the main cybersecurity obligations under NIS2?
NIS2 Article 21 requires organizations to implement risk analysis, incident response, business continuity measures, supply chain security, access control policies, MFA, encryption, and vulnerability management. These measures must be formally approved by the management body under Article 20, with documented evidence of implementation available for regulatory inspection.
What fines can organizations face for NIS2 non-compliance?
Essential entities face fines of up to €10 million or 2% of global annual turnover, whichever is higher. Important entities face up to €7 million or 1.4% of global turnover. Several member states exceed these minimums — Germany allows fines up to €20 million for essential entities, plus individual manager fines of up to €500,000 for governance failures.
What does NIS2 require for access management and credential security?
Article 21(2)(i) requires policies covering access control, authentication, and the use of cryptography. In practice, this means role-based access to critical systems, enforced MFA, documented credential policies, and a complete audit trail of privileged access events. Shared passwords, unmanaged service accounts, and undocumented access paths are direct compliance failures under this article.
How does NIS2 address supply chain security?
Article 21(2)(d) requires organizations to assess and manage the cybersecurity posture of their direct suppliers and service providers. This includes mapping critical third-party dependencies, embedding security obligations in contracts, and monitoring supplier posture on an ongoing basis. Only around 1 in 10 businesses were adequately assessing their suppliers' security measures as recently as 2024, according to the UK NCSC.
What are the NIS2 incident reporting deadlines?
NIS2 mandates a three-stage process: a 24-hour early warning to the national authority after detecting a significant incident, a 72-hour detailed notification with an initial impact assessment, and a 30-day final report covering root cause analysis and remediation steps. These deadlines apply to both essential and important entities and require pre-tested, automated response workflows to meet reliably.
What personal liability do executives face under NIS2?
Article 20 makes management bodies directly accountable for approving cybersecurity risk-management measures, overseeing their implementation, and completing cybersecurity training. Executives can be held personally liable for governance failures. In Germany, individual managers face fines of up to €500,000 under national NIS2 implementation law, and directors can be temporarily banned from management roles for serious negligence.
Does ISO 27001 certification satisfy NIS2 requirements?
ISO 27001 certification is recognized as a compliance pathway in some member states — Belgium accepts it as evidence of NIS2 conformity, provided organizations submit the certification scope, Statement of Applicability, and the most recent internal audit report. However, certification alone does not constitute full NIS2 compliance in most jurisdictions. It significantly reduces the compliance gap and provides auditors with a recognized evidence baseline, but organizations must still demonstrate implementation of all Article 21 measures.



Table of contents
- Key takeaways
- What is NIS2 and who does it cover
- Top story: Belgium's April 18 deadline
- The NIS2 readiness gap: 84% of businesses are not ready
- The EU vs. UK regulatory divergence: What multinationals must know
- Poland: KSC Act in force, entity list published
- Netherlands: The Cyberbeveiligingswet is almost in force
- Board liability: Article 20 makes it personal
- How Passwork supports NIS2 compliance
- Compliance calendar
- Conclusion
- Frequently Asked Questions
Table of contents
- Key takeaways
- What is NIS2 and who does it cover
- Top story: Belgium's April 18 deadline
- The NIS2 readiness gap: 84% of businesses are not ready
- The EU vs. UK regulatory divergence: What multinationals must know
- Poland: KSC Act in force, entity list published
- Netherlands: The Cyberbeveiligingswet is almost in force
- Board liability: Article 20 makes it personal
- How Passwork supports NIS2 compliance
- Compliance calendar
- Conclusion
- Frequently Asked Questions
Self-hosted password manager for business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment. Double encryption and zero-knowledge architecture ensure your passwords never leave your infrastructure.
Learn more

