
Introduction
As organizations race toward the June 30, 2026 deadline for their first formal NIS2 compliance audits, credential security has emerged as a critical failure point in early assessments across the EU.
Pre-audit findings from Q4 2025 show that identity and access management (IAM) gaps account for a significant portion of compliance deficiencies flagged by national authorities.
Specifically, auditors are repeatedly identifying missing multi-factor authentication (MFA), over-privileged accounts, and unmanaged service credentials as primary vulnerabilities, aligning with ENISA data showing that 34% of organizations currently face severe skills shortages in IAM implementation.
NIS2 password requirements mandate that European companies implement multi-factor authentication, enforce strong credential policies aligned with NIST SP 800-63B guidelines, and continuously monitor for compromised passwords to comply with Article 21 risk management measures.
Organizations that treat these controls as documentation exercises rather than operational realities are the ones failing pre-audits.
Key takeaways
- Article 21(2)(i) and (j) require documented access control policies and MFA deployment — both are actively checked in 2026 audit cycles.
- NIST SP 800-63B (2025 revision) sets a 15-character minimum and deprecates mandatory 90-day rotation — password changes should be triggered by evidence of compromise, not by calendar.
- The most common Q4 2025 pre-audit failures: missing MFA on internal systems, over-privileged accounts, and dormant identities that were never disabled after offboarding.
- Fines reach €10M or 2% of global annual turnover; the average breach costs $4.4M — credential controls cost a fraction of either figure.
- The leading audit failure is not missing controls — it is missing evidence. Organizations that cannot produce access logs, access review records, and credential hygiene reports fail regardless of what they have deployed.
The 2026 NIS2 audit landscape: What regulators are checking
The ENISA NIS Investments 2025 report reveals a sharp tension: 70% of EU organizations cite regulatory compliance as their primary cybersecurity investment driver, yet 34% report skills gaps specifically in identity and access management. Compliance intent and operational readiness are not the same thing — and auditors know it.
National competent authorities are now conducting structured pre-audits of both essential entities (large organizations in high-criticality sectors under Annex I: energy, banking, healthcare, digital infrastructure) and important entities (Annex II sectors including postal services, food production, and waste management).
The supervision model differs — essential entities face proactive, regular audits; important entities are monitored reactively — but both categories must meet identical technical requirements under Article 21.
Pre-audit findings from Q4 2025 across Germany, the Netherlands, and Austria consistently flag the same identity management failures:
- Over-privileged accounts — standard user accounts with administrative rights, service accounts with domain-level permissions that have never been scoped down
- Missing or inconsistent MFA — MFA deployed for cloud access but absent from internal systems and VPN entry points
- Unmanaged tokens and API keys — credentials for third-party integrations stored in plaintext, spreadsheets, or shared inboxes
- Dormant accounts — former employees and contractors with active directory accounts that were never disabled after offboarding
- No documented access review process — organizations that apply controls but cannot produce evidence of periodic review
The last point matters most. Auditors are not just checking whether controls exist — they are checking whether organizations can prove those controls are operating continuously.
Article 21: Decoding the identity and access mandates
Article 21 of Directive (EU) 2022/2555 requires essential and important entities to take "appropriate and proportionate technical, operational and organisational measures" to manage risks to network and information systems. The directive does not prescribe specific password lengths or MFA methods — it sets outcome-based requirements that organizations must translate into concrete controls.
Two sub-clauses are directly relevant to credential security:
- Article 21(2)(i) requires "human resources security, access control policies and asset management."
- Article 21(2)(j) mandates "the use of multi-factor authentication or continuous authentication solutions… where appropriate."
The phrase "where appropriate" is not a loophole — ENISA technical guidance and national transpositions consistently interpret it as mandatory for privileged access and remote access scenarios.
The directive also marks a structural shift in how security is framed. The previous NIS Directive treated cybersecurity largely as incident response: detect, report, recover. NIS2 moves the obligation upstream.
Two additional sub-clauses define this proactive posture:
- Article 21(2)(a) requires documented risk analysis and information system security policies.
- Article 21(2)(g) mandates basic cyber hygiene practices and training.
The expectation is that organizations operate within a zero-trust architecture mindset — where access is continuously validated, not assumed after initial authentication.
This shift has direct implications for password management. A policy document sitting in a shared folder is not a control. A control is an enforced technical measure with an audit trail showing it is applied consistently across all accounts, systems, and user types.
Specific password policy requirements for 2026
NIS2-compliant password policy in 2026 means aligning with NIST digital identity guidelines (SP 800-63B, 2025 revision) while addressing the credential threat reality confirmed by the latest research.
Compromised credentials remain the most common initial access vector, present in 22% of all confirmed breaches — and 88% of basic web application attacks involved stolen credentials specifically.
Password reuse compounds the exposure: infostealer data shows that only 49% of a user's passwords across different services are unique, meaning a single compromised account routinely opens access to many others. Third-party involvement in breaches doubled year-over-year, from 15% to 30%, with credential abuse at the center of that supply chain risk. Policy that does not account for this attack surface is structurally incomplete.
The 2025 revision of NIST SP 800-63B makes two significant changes that directly affect NIS2 compliance planning:
- 15-character minimum when a memorized secret (password) is used as the sole authenticator. This replaces the previous 8-character baseline and reflects the computational reality of modern brute-force attacks.
- Deprecation of forced periodic rotation — mandatory 90-day password changes are explicitly discouraged. Forced rotation produces predictable incremental changes ("Summer2025!" → "Autumn2025!") and increases help desk load without improving security. Rotation should be triggered by evidence of compromise, not by calendar.
A compliant password policy for 2026 must include the following controls:
- Length over complexity — minimum 15 characters; allow passphrases; do not require mandatory character-class mixing that produces predictable substitutions
- Dictionary word and pattern blocking — reject passwords containing common words, keyboard walks (qwerty, 123456), and username strings
- No password reuse — enforce history checks across critical systems; credential stuffing attacks rely on reused credentials from previous breaches
- Compromise-triggered rotation — change passwords immediately when credentials appear in breach data, not on a fixed schedule
- Fine-grained password policy (FGPP) — apply stricter rules to privileged accounts, service accounts, and accounts with access to sensitive data, separate from standard user policy
For organizations running Active Directory environments, fine-grained password policy (FGPP) allows different password settings objects (PSOs) to be applied to specific users or security groups — enabling stricter controls for administrators without imposing the same friction on all users.
Multi-factor authentication: Moving beyond SMS
Phishing-resistant MFA is the operative standard under NIS2 — and it excludes SMS-based one-time passwords. MFA blocks 99.9% of automated attacks on user accounts, but phishing remains the most common intrusion vector, accounting for 60% of incidents analyzed in the ENISA Threat Landscape 2025. SMS OTPs and email-based codes are vulnerable to real-time phishing proxies that intercept tokens mid-session — they do not protect against this attack class.
The distinction between acceptable and unacceptable MFA methods under NIS2 is not explicitly codified in the directive text, but ENISA guidance and the NIST AAL2/AAL3 framework (SP 800-63B) provide the reference standard:
| MFA method | NIS2 status | Reason |
|---|---|---|
| FIDO2 / WebAuthn hardware keys | ✅ Compliant | Phishing-resistant; cryptographic binding to origin |
| Passkeys (device-bound) | ✅ Compliant | Phishing-resistant; no shared secret transmitted |
| TOTP authenticator apps | ⚠️ Conditional | Acceptable for standard users; not sufficient for privileged access |
| Push notifications (with number matching) | ⚠️ Conditional | Reduces MFA fatigue attacks; still susceptible to some social engineering |
| SMS OTP | ❌ Not recommended | Vulnerable to SIM swapping, SS7 attacks, real-time phishing |
| Email OTP | ❌ Not recommended | Depends on email account security; not a separate factor |
For privileged access — domain administrators, security operations, system accounts — NIST SP 800-63B AAL3 requirements apply: phishing-resistant authenticators with non-exportable keys. FIDO2 hardware tokens (YubiKey, Google Titan) or device-bound passkeys meet this bar.
For Active Directory environments, deploying phishing-resistant MFA requires integration with Azure AD Conditional Access or a compatible on-premises MFA solution that enforces hardware-backed authentication for privileged roles. Standard TOTP-based MFA configured at the application layer does not protect AD authentication itself.
Hardening Active Directory and managing account lifecycles
Active Directory remains the identity backbone for the majority of European enterprise environments — and it is the primary target in credential-based attacks. NIS2 compliance requires that AD hardening be treated as a documented, auditable process, not a one-time configuration task.
Step 1: Audit and scope privileged accounts
Run a full inventory of accounts with Domain Admin, Enterprise Admin, Schema Admin, and Backup Operators membership. Every account in these groups should have a named owner, a documented business justification, and MFA enforced at the authentication layer. Remove any accounts that cannot be justified.
Step 2: Implement fine-grained password policy (FGPP)
Create separate Password Settings Objects for privileged accounts (15+ character minimum, breach screening, no reuse for 24 cycles) and standard users (15+ character minimum, breach screening). Apply PSOs directly to security groups, not individual accounts, to maintain consistency as membership changes.
Step 3: Secure and inventory service accounts
Service accounts and non-human identities are the most consistently overlooked credential class in pre-audit findings. For each service account: document the system it serves, scope permissions to the minimum required, rotate credentials on a defined schedule, and store them in a centralized secrets vault — not in scripts, configuration files, or shared spreadsheets. Group Managed Service Accounts (gMSA) in AD automate password rotation for service accounts and should be used wherever the application supports them.
Step 4: Automate offboarding and dormant account management
Dormant accounts — active directory objects for former employees, contractors, and decommissioned systems — are a persistent audit failure point. Implement automated offboarding workflows that disable accounts within 24 hours of HR system updates. Run monthly reports on accounts with no login activity in 90+ days and disable or delete them after review. This is not optional under Article 21(2)(i): asset management includes the lifecycle of identity assets.
Step 5: Enable and review audit logs
AD audit policy must capture account logon events, account management changes, privilege use, and directory service access. These logs must be retained for a period consistent with your incident reporting obligations under Article 21(2)(b) — most national implementations require a minimum of 12 months. Forward logs to a SIEM for correlation and alerting.
Step 6: Enforce least-privilege access
Conduct quarterly access reviews for all privileged roles. Use role-based access control (RBAC) to assign permissions to roles, not individuals. Document each review — the date, reviewer, accounts examined, and changes made. This documentation is what auditors ask for first.
The cost of compliance vs. the cost of failure
The financial case for investing in credential security is straightforward when the numbers are placed side by side.
First-year NIS2 compliance implementation costs range from €150,000 to €750,000 depending on sector complexity, organization size, and the maturity of existing controls. This range covers policy development, technical tooling, staff training, and external advisory work. For organizations with mature security programs, the incremental cost is considerably lower — primarily the gap-filling work in identity management and documentation.
The alternative is considerably more expensive. Essential entities face fines of up to €10 million or 2% of global annual turnover — whichever figure is higher. Important entities face up to €7 million or 1.4% of turnover.
These are maximum figures; national authorities apply proportionality. But the direction of enforcement is clear: Germany's BSI, the Dutch NCSC, and Austria's CERT.at have all signaled that identity management failures will be prioritized in 2026 audit cycles.
The breach cost calculation adds a third dimension. The average cost of a data breach is $4.4 million (IBM Cost of a Data Breach Report 2025), and credential compromise is the leading initial attack vector. An organization that avoids one breach by implementing compliant credential controls has, in financial terms, more than recovered its compliance investment.
For essential entities operating in energy, healthcare, or financial services, the ROI calculation is not close. The cost of deploying phishing-resistant MFA, a centralized password manager, and automated AD hardening across a 500-person organization is a fraction of a single regulatory fine — let alone a breach.
How a corporate password manager ensures audit readiness
The evidence gap is where most NIS2 compliance programs break down. Organizations implement controls — they enforce password policies, they deploy MFA, they conduct access reviews — but they cannot produce the documentation that demonstrates these controls are operating continuously. Auditors do not accept verbal assurances. They ask for logs.
A corporate password manager addresses the compliance audit evidence problem directly. It provides three categories of documentation that regulators require:
- Centralized access control records. Every credential in the organization is stored in a structured vault with defined permissions. Auditors can see, for each password: who has access, at what permission level, when access was granted, and when it was last reviewed. This maps directly to Article 21(2)(i) access control policy requirements.
- Immutable activity logs. Every action — password creation, modification, access, sharing, deletion — is recorded with a timestamp and user identity. These logs cannot be altered by standard users and provide the audit trail required under Article 21(2)(b) incident handling and Article 21(2)(f) effectiveness assessment obligations. When a security incident occurs, the logs show exactly what credentials were accessed and by whom.
- Automated security analysis. Password security dashboards that continuously flag weak, reused, outdated, and compromised credentials provide ongoing evidence that the organization is actively managing credential hygiene — not just setting a policy and forgetting it. This is the operational continuity evidence that distinguishes a mature compliance program from a checkbox exercise.
For incident reporting purposes, the ability to immediately identify which credentials were potentially exposed — and which systems they access — is operationally critical. NIS2 Article 21(2)(b) requires incident handling procedures; a centralized credential inventory is the foundation of any meaningful incident response.
How Passwork closes the audit evidence gap
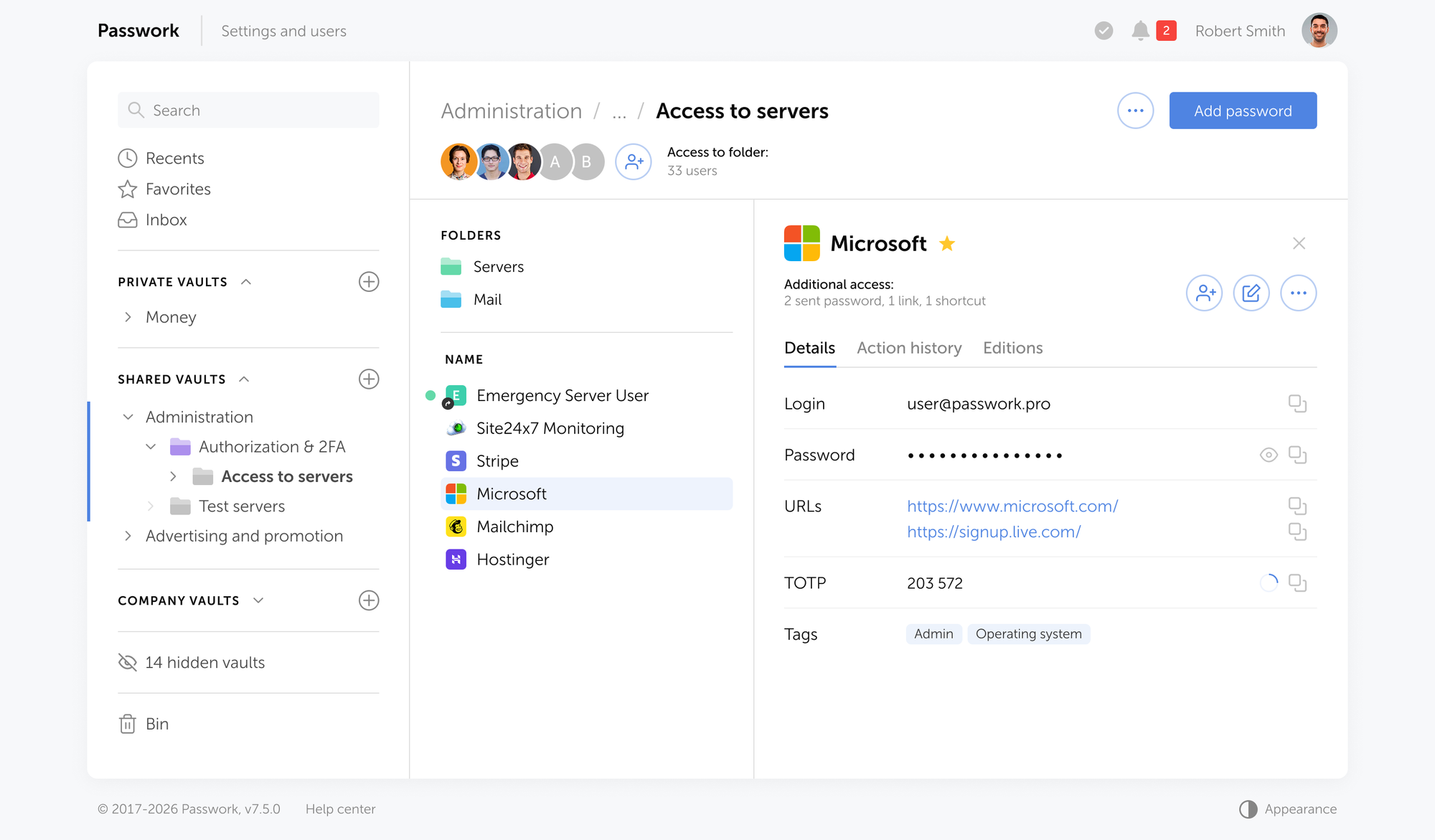
Passwork provides all of these capabilities as a self-hosted solution deployed within your own infrastructure. Credential data never leaves your environment. LDAP/AD group synchronization maps your existing directory structure to vault permissions automatically, reducing administrative overhead while maintaining the access control documentation NIS2 auditors require.
The full activity log, role-based access model, and password security dashboard give compliance officers the evidence package they need — without manual compilation before each audit.
Conclusion

NIS2 password requirements are not a new category of compliance burden — they are a formalization of security practices that should already be in place. The organizations failing Q4 2025 pre-audits are not failing because the requirements are unclear. They are failing because identity management has been treated as infrastructure maintenance rather than a documented, auditable security control.
The path to compliance is concrete: align password policies with NIST SP 800-63B, deploy phishing-resistant MFA for privileged and remote access, harden Active Directory with FGPP and automated lifecycle management, and implement centralized credential management that produces the audit evidence regulators demand.
Credential security is the foundation on which every other NIS2 control rests. If an attacker can authenticate as a legitimate user, your network segmentation, your encryption, and your incident detection capabilities all face a harder problem. Getting identity right is not a prerequisite for NIS2 compliance — it is NIS2 compliance, operationally.
Frequently asked questions

What are the NIS2 password requirements under Article 21?
Article 21(2)(i) of Directive (EU) 2022/2555 requires essential and important entities to implement access control policies and human resources security measures. In practice, this means enforcing minimum password lengths aligned with NIST SP 800-63B (15 characters for sole authenticators), screening credentials against breach databases, banning password reuse, and applying stricter fine-grained policies to privileged accounts.
Does NIS2 mandate multi-factor authentication?
Article 21(2)(j) requires the use of MFA "where appropriate." ENISA technical guidance and national transpositions consistently interpret this as mandatory for privileged access, remote access, and any system handling sensitive data. SMS-based OTPs are not considered sufficient — phishing-resistant methods such as FIDO2 hardware keys or device-bound passkeys are the expected standard for high-risk access scenarios.
What is the deadline for NIS2 compliance in 2026?
EU member states were required to transpose NIS2 into national law by October 2024. Enforcement is active, and national competent authorities are conducting structured audits throughout 2026. There is no single "deadline" — organizations are expected to be compliant now, and the June 2026 audit cycle is when many essential entities will face their first formal assessment.
What are the fines for NIS2 non-compliance?
Essential entities face fines of up to €10 million or 2% of global annual turnover, whichever is higher. Important entities face up to €7 million or 1.4% of global annual turnover. National authorities apply proportionality, but identity management failures — missing MFA, unmanaged accounts, absent audit logs — are explicitly flagged as priority enforcement areas for 2026.
How does a password manager help with NIS2 compliance?
A corporate password manager addresses the evidence gap that causes most compliance failures. It provides centralized access control records, immutable activity logs, and automated credential security analysis — the three categories of documentation that NIS2 auditors require. A self-hosted solution like Passwork keeps all credential data within your own infrastructure, satisfying both NIS2 access control requirements and data residency obligations.
What is the difference between essential and important entities under NIS2?
Essential entities are large organizations in high-criticality sectors listed in Annex I of the directive — energy, banking, healthcare, digital infrastructure, transport, and water. They face proactive supervision with regular audits. Important entities cover Annex II sectors including postal services, food production, and waste management, and are monitored reactively. Both categories must meet identical technical requirements under Article 21.
What password length does NIS2 require?
NIS2 does not specify a password length directly — it requires measures aligned with "the state of the art" and relevant standards. The applicable standard is NIST SP 800-63B (2025 revision), which sets a 15-character minimum when a memorized secret is used as the sole authenticator. For accounts protected by MFA, a shorter minimum may be acceptable, but 15 characters remains the recommended baseline for all accounts.


Table of contents
- Introduction
- Key takeaways
- The 2026 NIS2 audit landscape: What regulators are checking
- Article 21: Decoding the identity and access mandates
- Specific password policy requirements for 2026
- Multi-factor authentication: Moving beyond SMS
- Hardening Active Directory and managing account lifecycles
- The cost of compliance vs. the cost of failure
- How a corporate password manager ensures audit readiness
- How Passwork closes the audit evidence gap
- Conclusion
- Frequently asked questions
Table of contents
- Introduction
- Key takeaways
- The 2026 NIS2 audit landscape: What regulators are checking
- Article 21: Decoding the identity and access mandates
- Specific password policy requirements for 2026
- Multi-factor authentication: Moving beyond SMS
- Hardening Active Directory and managing account lifecycles
- The cost of compliance vs. the cost of failure
- How a corporate password manager ensures audit readiness
- How Passwork closes the audit evidence gap
- Conclusion
- Frequently asked questions
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more



