
Which words pop into your head when creating a password for your new account on a website or on a social network? Safety? Privacy? Well, there’s some bad news — hackers are clued-up on hacking any kind of password that you can think into existence, and as a matter of fact, it’s a global problem.
According to recent Kaspersky analysis of 193 million real-world passwords, 59% can be cracked in under one hour using a modern GPU and smart guessing algorithms. Even more alarming, 45% of those passwords fall in under one minute. This data underscores a harsh reality for enterprise security teams: traditional password complexity rules are failing.
Attackers no longer rely solely on manual guessing. They deploy industrialized, AI-assisted tools and Malware-as-a-Service platforms to harvest credentials at an unprecedented scale. The leak of 16 billion credentials from 30 data sources and the exposure of 184 million credentials on underground markets demonstrate the sheer volume of data available to threat actors.
This article explains how each major password cracking technique works, the real-world scale of these threats, and what organizations must do to defend against them. Understanding the attacker’s toolkit is the first step in securing your enterprise infrastructure.
What is password cracking?
Password cracking is the process by which attackers attempt to recover or bypass authentication credentials — either by decrypting stolen password hashes offline or by guessing credentials directly against live systems. Techniques range from automated brute-force and dictionary attacks to AI-powered guessing, phishing, and infostealer malware.
Security professionals divide these techniques into two primary categories: online and offline attacks:
- Online attacks involve interacting directly with a live authentication system, such as a website login portal or an SSH gateway. These attacks are inherently constrained by network latency, rate-limiting, and account lockout policies.
- Offline attacks pose a far greater enterprise threat. When attackers steal a database of hashed passwords, they can attempt to crack them on their own hardware without triggering any network alarms. Unconstrained by rate limits, attackers leverage immense computational power. A single modern GPU, such as an NVIDIA RTX 4090, can process 164 billion MD5 hashes per second. Against this level of hardware, weak passwords are mathematically trivial to break.
Top 12 Password cracking techniques hackers use in 2025
1. Brute force attack
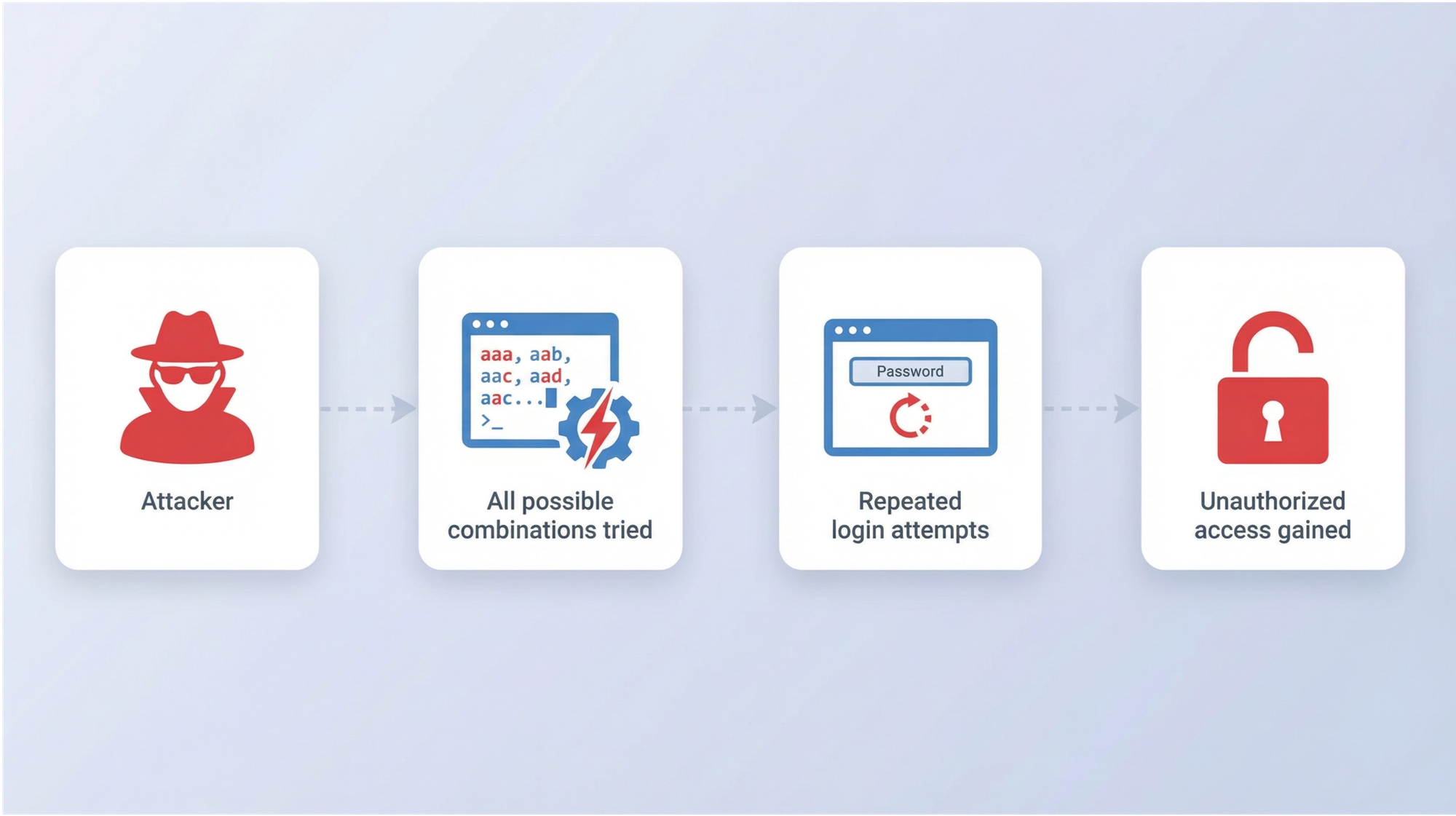
A brute force attack relies on exhaustive enumeration. The attacker’s software systematically tries every possible combination of characters — letters, numbers, and symbols — until it finds the correct match. It is the most fundamental password cracking technique, guaranteeing success eventually, provided the attacker has enough time and computing power.
To defend against brute force attacks, organizations must enforce minimum length requirements of at least 12 characters. Length provides exponentially more protection than complexity. Implement strict account lockout policies for online portals to stop live guessing.
For stored data, ensure all passwords are hashed using computationally expensive algorithms like bcrypt or Argon2, which intentionally slow down the verification process and neutralize hardware advantages.
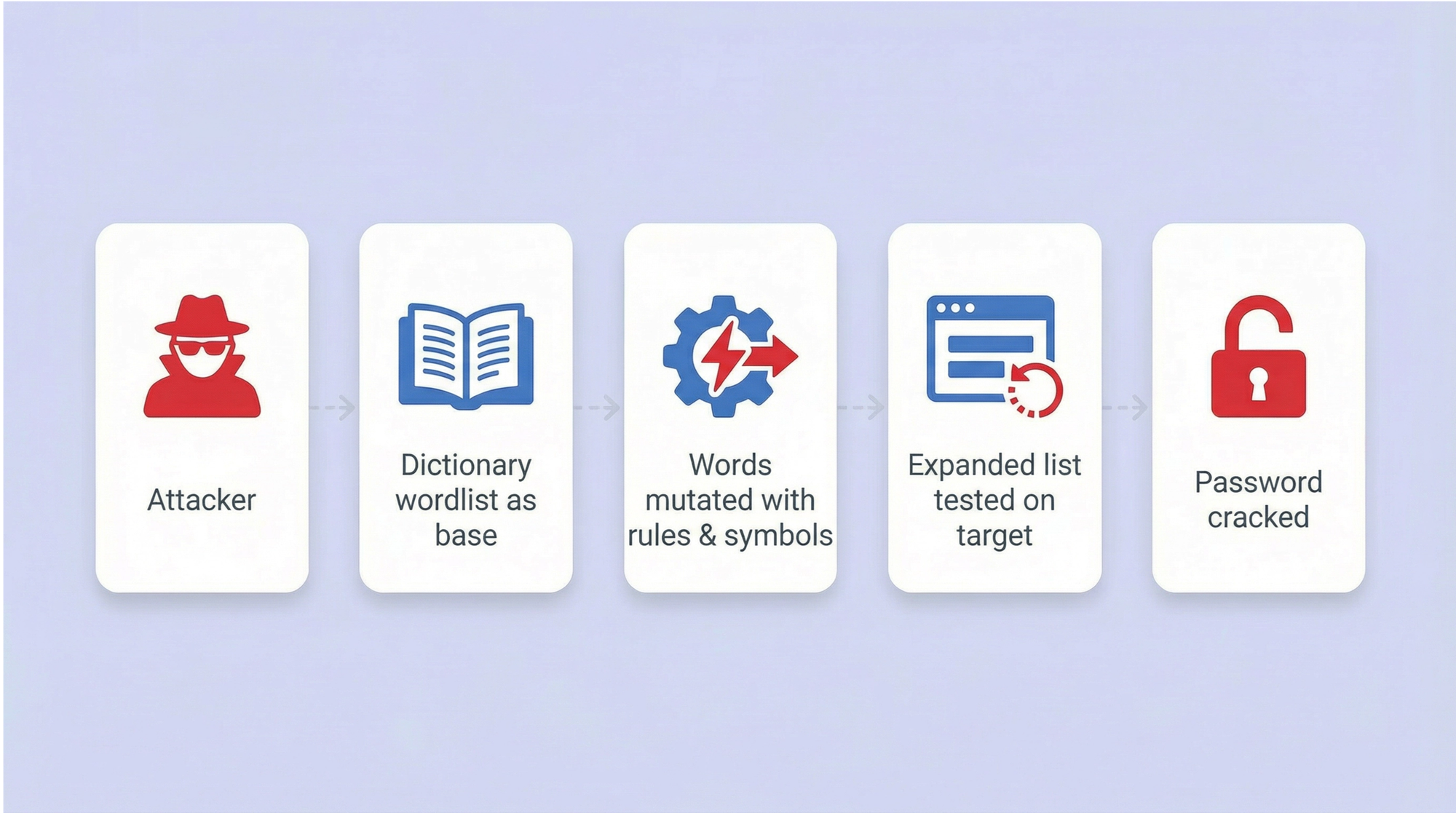
2. Dictionary attack
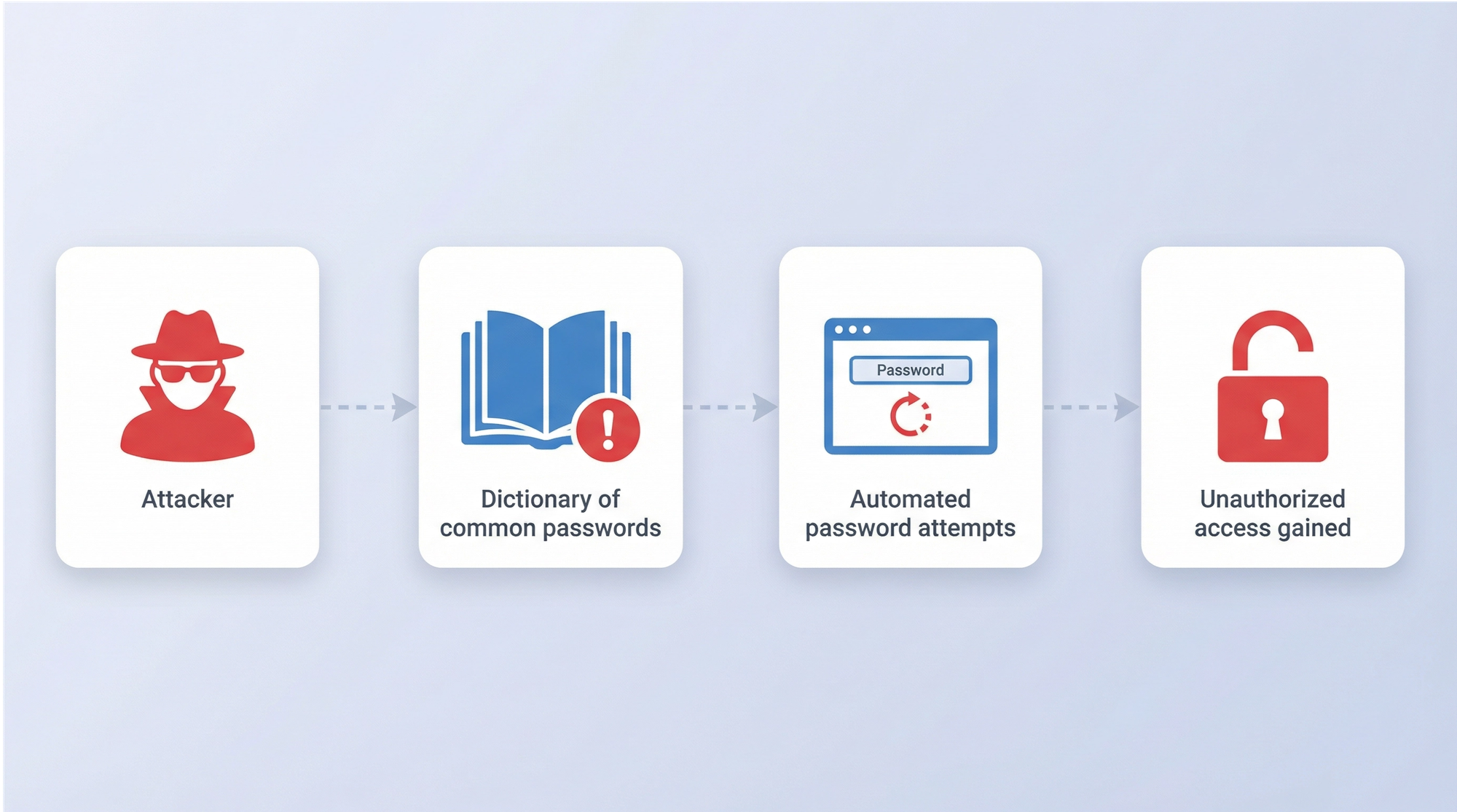
A dictionary attack uses a precompiled list of likely passwords to guess credentials. Attackers leverage massive wordlists, such as the infamous RockYou dataset, Have I Been Pwned dumps, and custom lists derived from Open-Source Intelligence (OSINT). They combine these base words with rule-based mutations, adding common numbers, capitalization, and “leet speak” substitutions (e.g., replacing “a” with “@”).
This method is highly efficient because we are predictable. We favor memorable words and patterns. Kaspersky’s analysis revealed that 57% of all analyzed passwords contain a dictionary word or a common symbol combination. Instead of trying every possible character, a dictionary attack tests the passwords people actually use, drastically reducing the time required to breach an account.
Defense requires blocking common passwords at the point of creation. Integrate a breached password monitoring service into your Active Directory or identity provider to prevent users from selecting known compromised terms. Enforce true randomness in password generation, moving away from simple substitutions that dictionary rules easily anticipate.
3. Credential stuffing

Credential stuffing exploits the human habit of password reuse. Attackers take massive lists of usernames and passwords exposed in one breach and systematically test them across hundreds of other services using automated botnets. If a user utilizes the same password for their personal email and their corporate VPN, a breach of the former immediately compromises the latter.
The 2025 Verizon Data Breach Investigations Report (DBIR) highlights the dominance of this technique. Compromised credentials served as the initial access vector in 22% of all confirmed breaches. Credential stuffing accounted for a median 19% of all daily authentication attempts across monitored networks, spiking to an overwhelming 44% on the worst days. The 2023 breach of 23andMe stands as a canonical example of how devastating this attack vector can be when users recycle credentials.
Since employees cannot memorize dozens of unique credentials, companies must implement an enterprise password manager like Passwork. It automatically generates and securely stores unique credentials, eliminating the practice of password reuse. Deploy Multi-Factor Authentication (MFA) across all external-facing portals. Security teams must monitor authentication logs for anomalous login patterns.
4. Password spraying
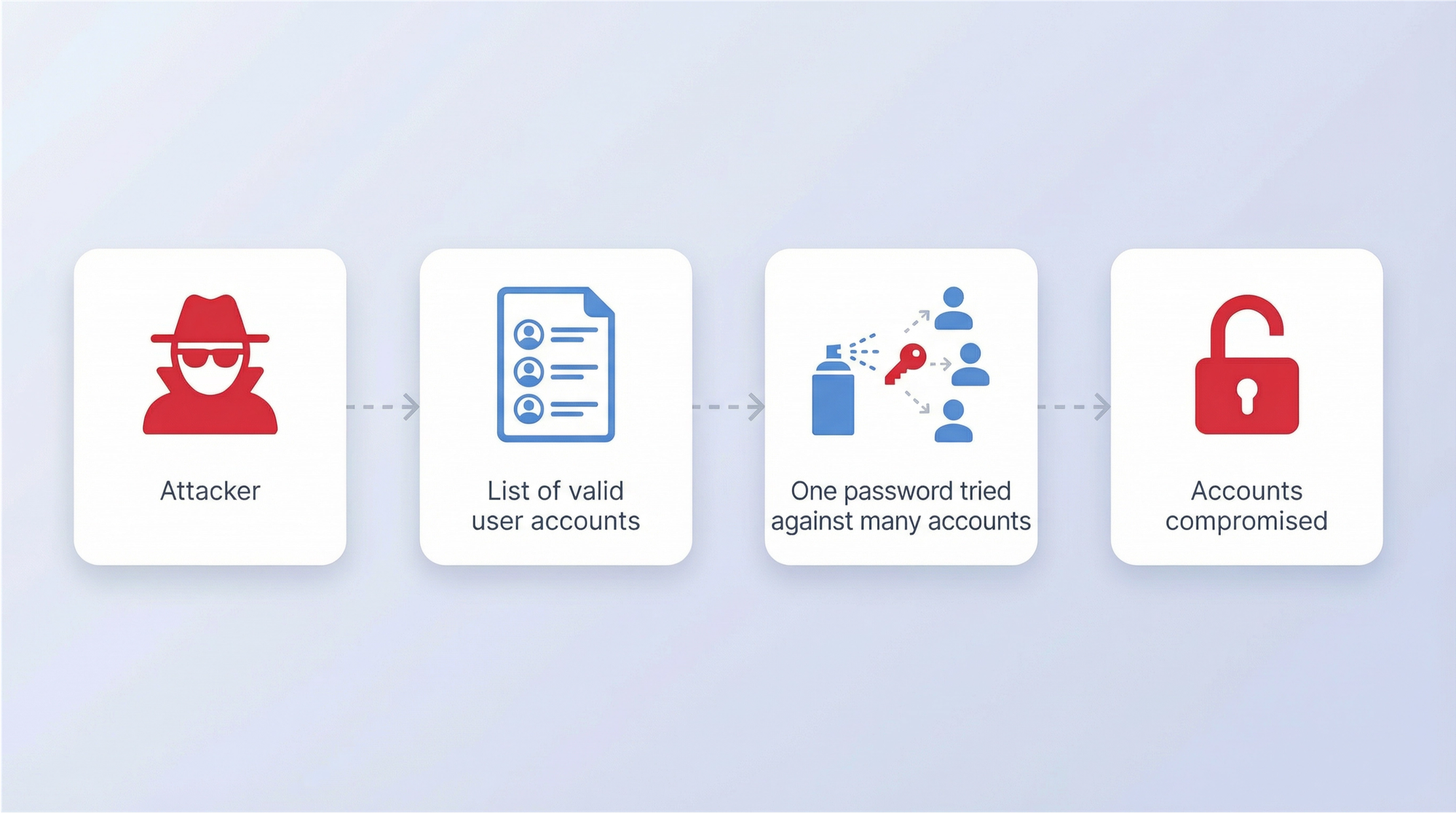
Password spraying is the inverse of a traditional brute force attack. Instead of trying thousands of passwords against a single account, an attacker tries one highly probable password — such as "“Password1!” or “Welcome2025” — against thousands of different accounts. This “low and slow” approach is specifically designed to evade account lockout policies and intrusion detection systems.
This technique remains highly effective against large organizations. SSH.com notes that Single Sign-On (SSO) environments are particularly vulnerable, as one successful guess grants access to a wide array of corporate resources. Attackers often time their spraying campaigns to coincide with corporate events, seasonal changes, or new employee onboarding, using passwords relevant to the context.
To stop password spraying, organizations must block commonly sprayed passwords globally. Implement MFA to ensure that a guessed password alone is insufficient for access. Security Information and Event Management (SIEM) systems should be configured to monitor for distributed, low-frequency login failures across the network, which often indicate an ongoing spray attack.
5. Rainbow table attack
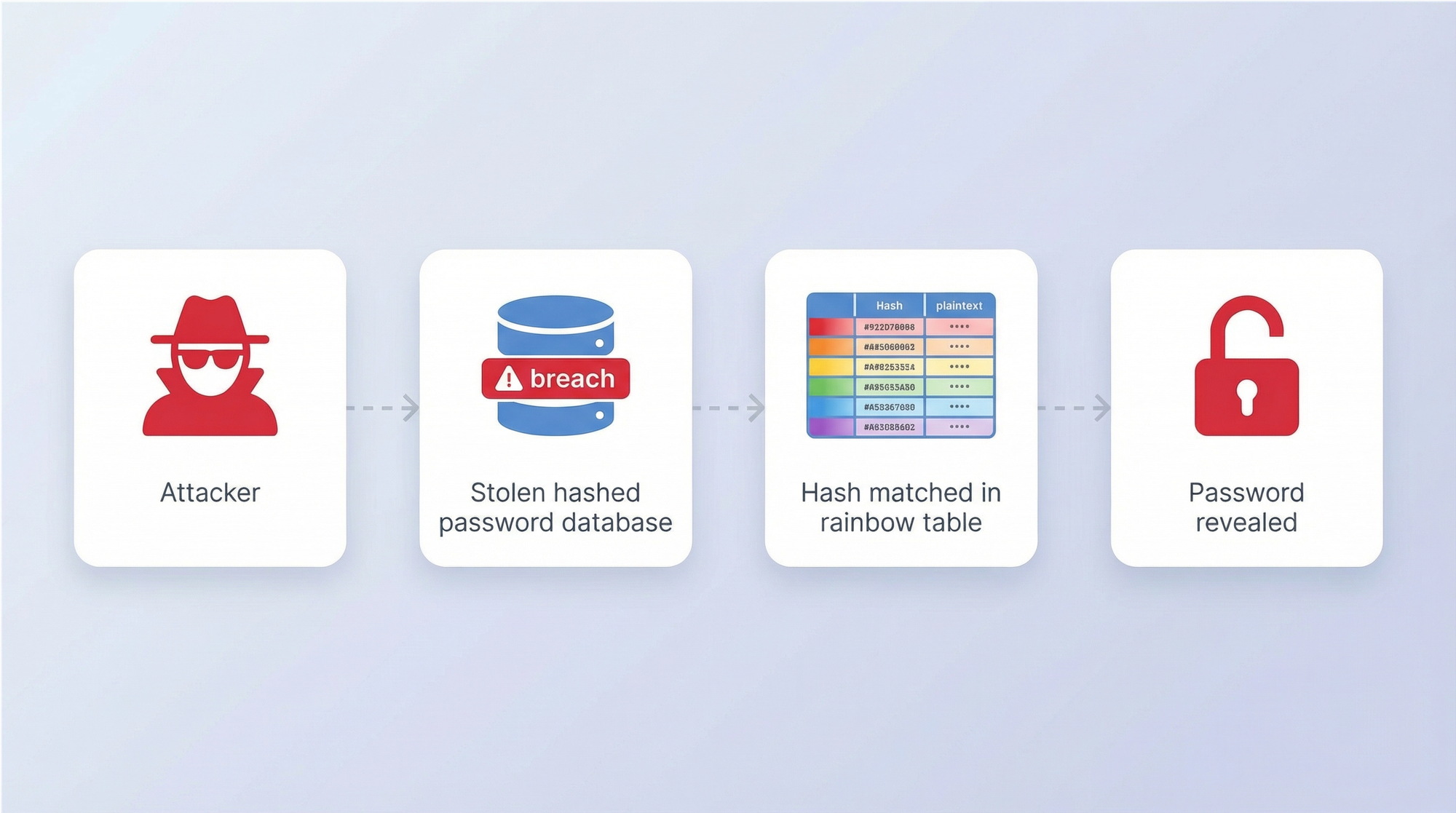
A rainbow table attack uses massive, precomputed tables of hash-to-plaintext pairings to reverse cryptographic hashes instantly. Instead of calculating hashes on the fly, the attacker simply looks up the stolen hash in their database to find the corresponding password. This technique is devastatingly effective against older, unsalted hashing algorithms like LM, NTLM, and MD5.
The effectiveness of rainbow tables relies entirely on the absence of a cryptographic “salt” — a random string of data added to the password before hashing. If two users have the same password, an unsalted hash will look identical for both. A rainbow table exploits this predictability. Defending against rainbow tables is straightforward: ensure all password storage uses salted hashing. When a unique salt is added to every password, the precomputed tables become useless.
6. Phishing and spear phishing
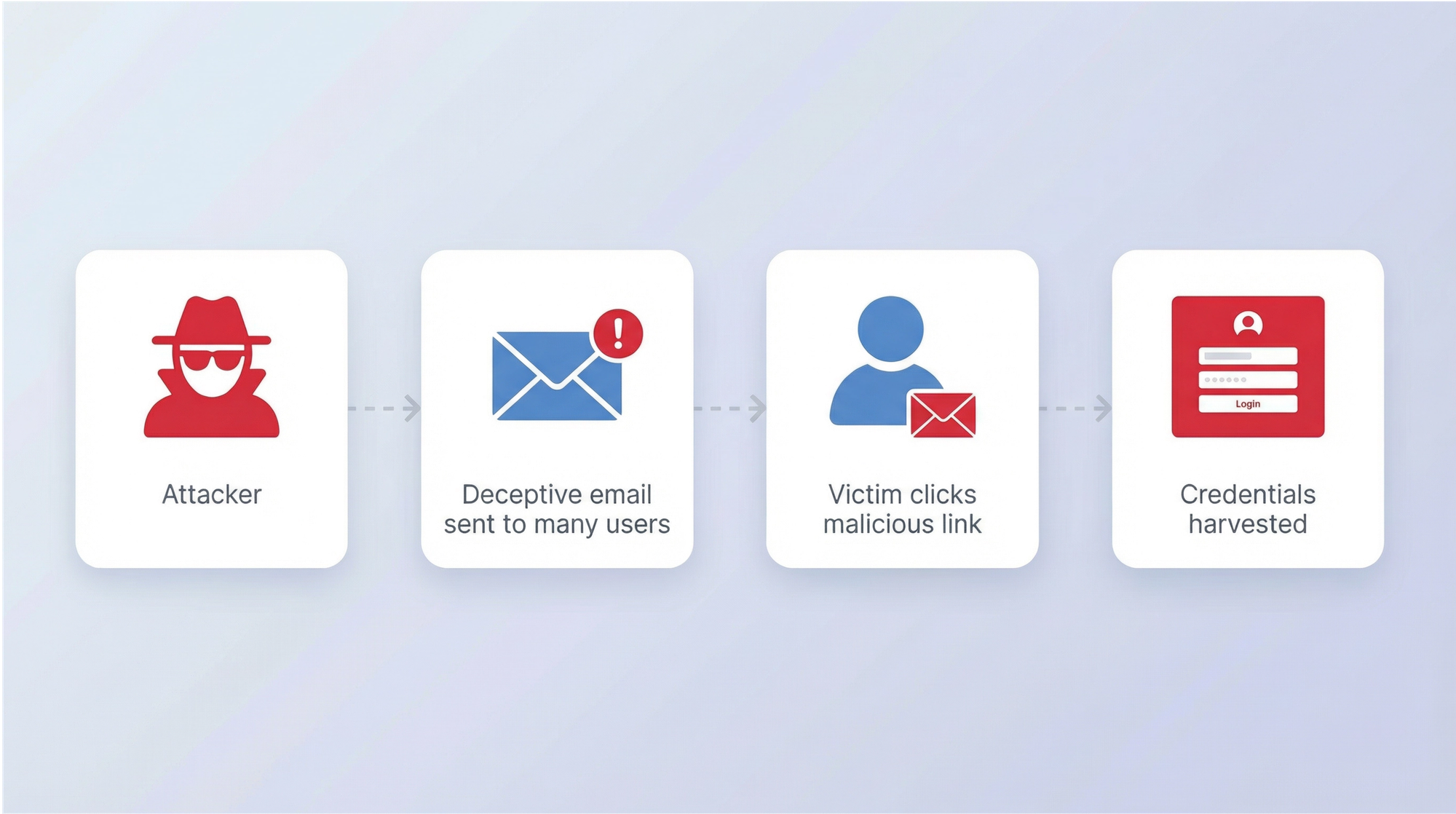
The easiest and most common way of hacking someone’s password is phishing. There are plenty of techniques here: phishing can take the form of an email, an SMS, a direct message on a social media platform, or a public post on a website.
Phishing bypasses the technical challenge of cracking a password by simply tricking the user into handing it over. Attackers deploy fake login pages, deceptive email lures, and sophisticated Adversary-in-the-Middle (AiTM) proxy attacks. AiTM attacks are particularly dangerous because they sit between the user and the legitimate service, capturing session cookies and MFA tokens in real time.
Phishing takes many forms. Spear phishing targets specific individuals with highly personalized lures. Smishing uses SMS messages, vishing relies on voice calls, and whaling targets C-suite executives. The IBM Cost of a Data Breach Report 2025 identified phishing as the most common initial attack vector, responsible for 16% of breaches at an average cost of $4.88 million per incident.
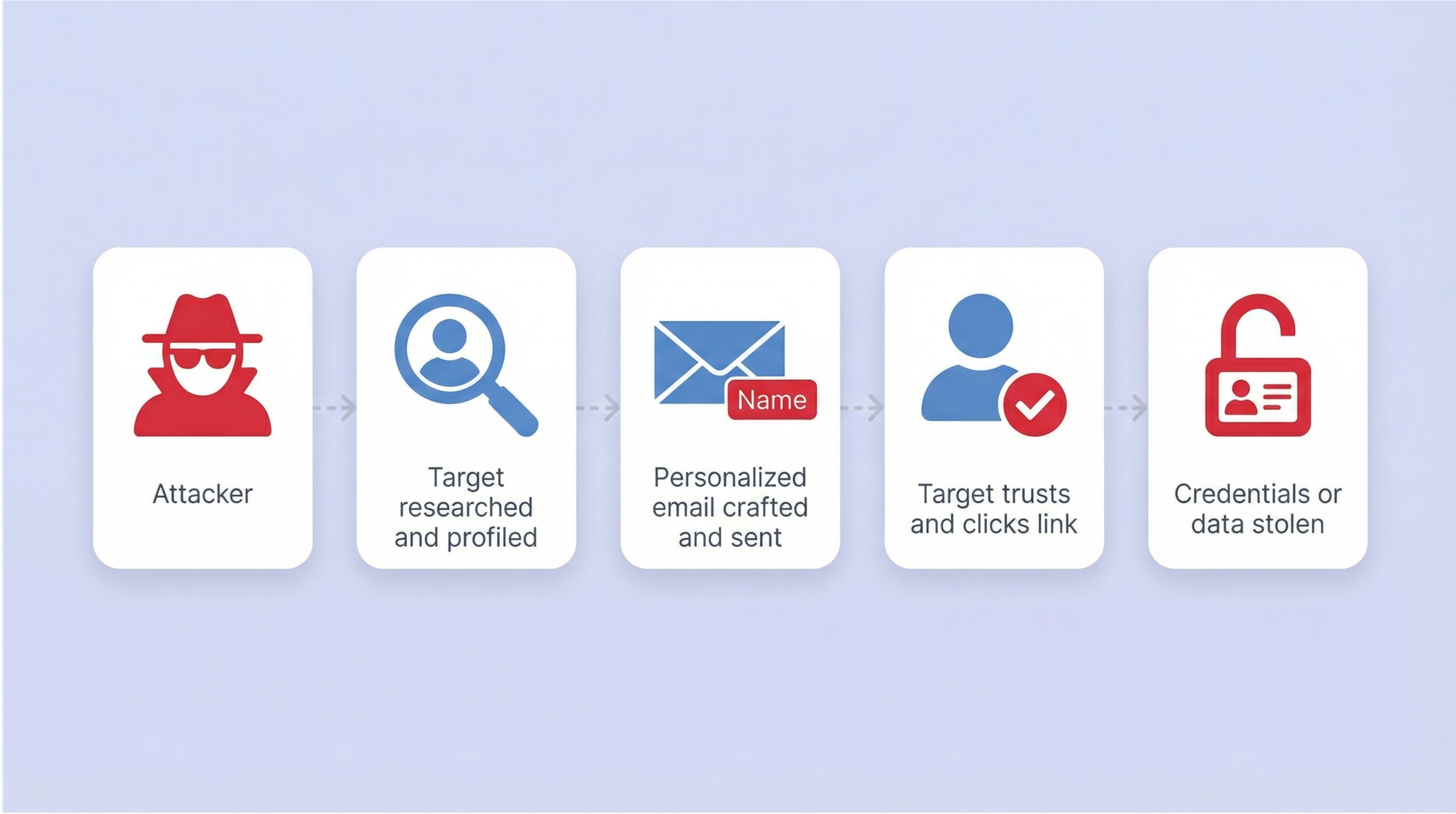
Defense requires a multi-layered approach. Regular security awareness training helps employees recognize deceptive tactics. Deploy strict email filtering and DMARC authentication to block malicious messages before they reach the inbox. Most importantly, organizations must transition to phishing-resistant MFA, such as FIDO2 security keys or passkeys, which mathematically bind the authentication token to the specific legitimate domain, rendering stolen credentials useless.
7. Keylogger and infostealer malware
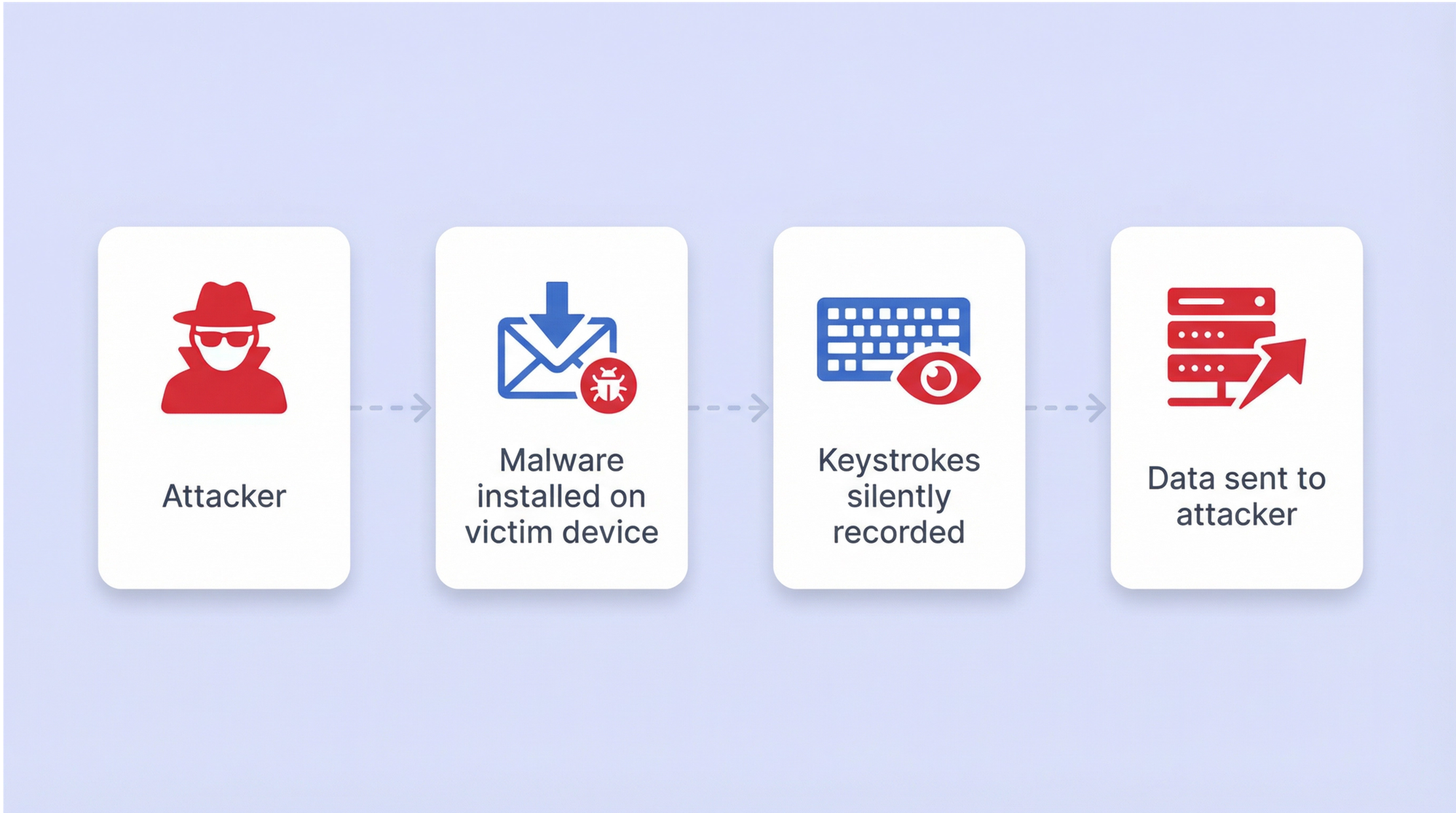
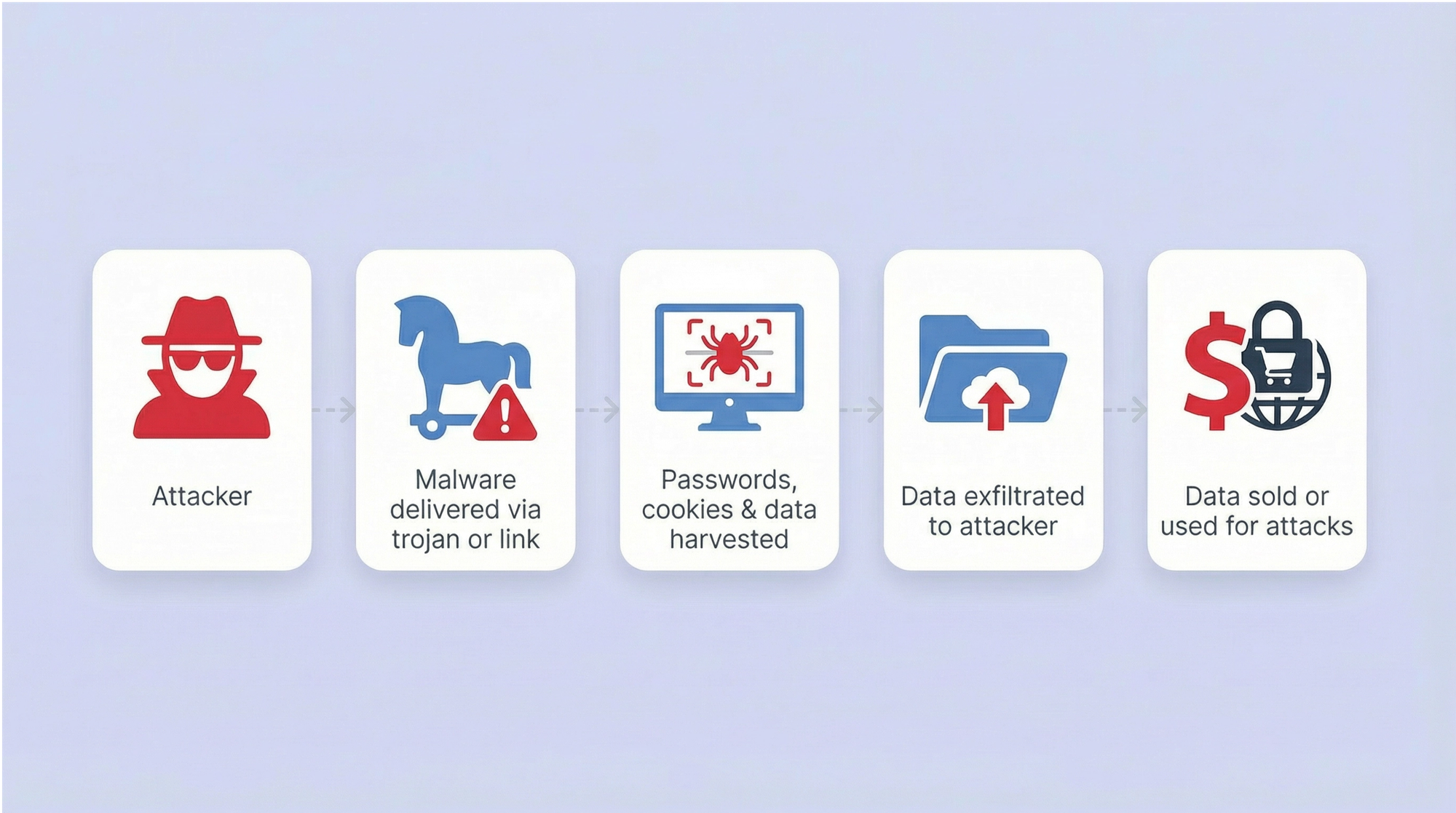
While traditional keyloggers simply recorded keystrokes, modern attackers utilize highly sophisticated infostealer malware. Families like Lumma, Acreed, and StealC V2 operate silently, extracting saved browser passwords, active session cookies, cryptocurrency wallets, and MFA tokens in a single sweep.
The scale of this threat is staggering. According to Vectra AI and DeepStrike, infostealers stole 1.8 billion credentials from 5.8 million devices in 2025 — representing an 800% year-over-year increase. This explosion is driven by the Malware-as-a-Service (MaaS) model. Sophisticated infostealer platforms are available on dark web forums for as little as $200 per month, lowering the barrier to entry for cybercriminals.
To defend against infostealers, organizations must deploy robust Endpoint Detection and Response (EDR) solutions. Implement privileged access management to restrict the execution of unauthorized software. Employees must be strictly prohibited from saving corporate credentials in built-in browser password managers. Using a dedicated, encrypted vault like Passwork isolates credentials from malicious endpoint processes and prevents mass theft by infostealers.
8. Man-in-the-Middle (MitM) attack
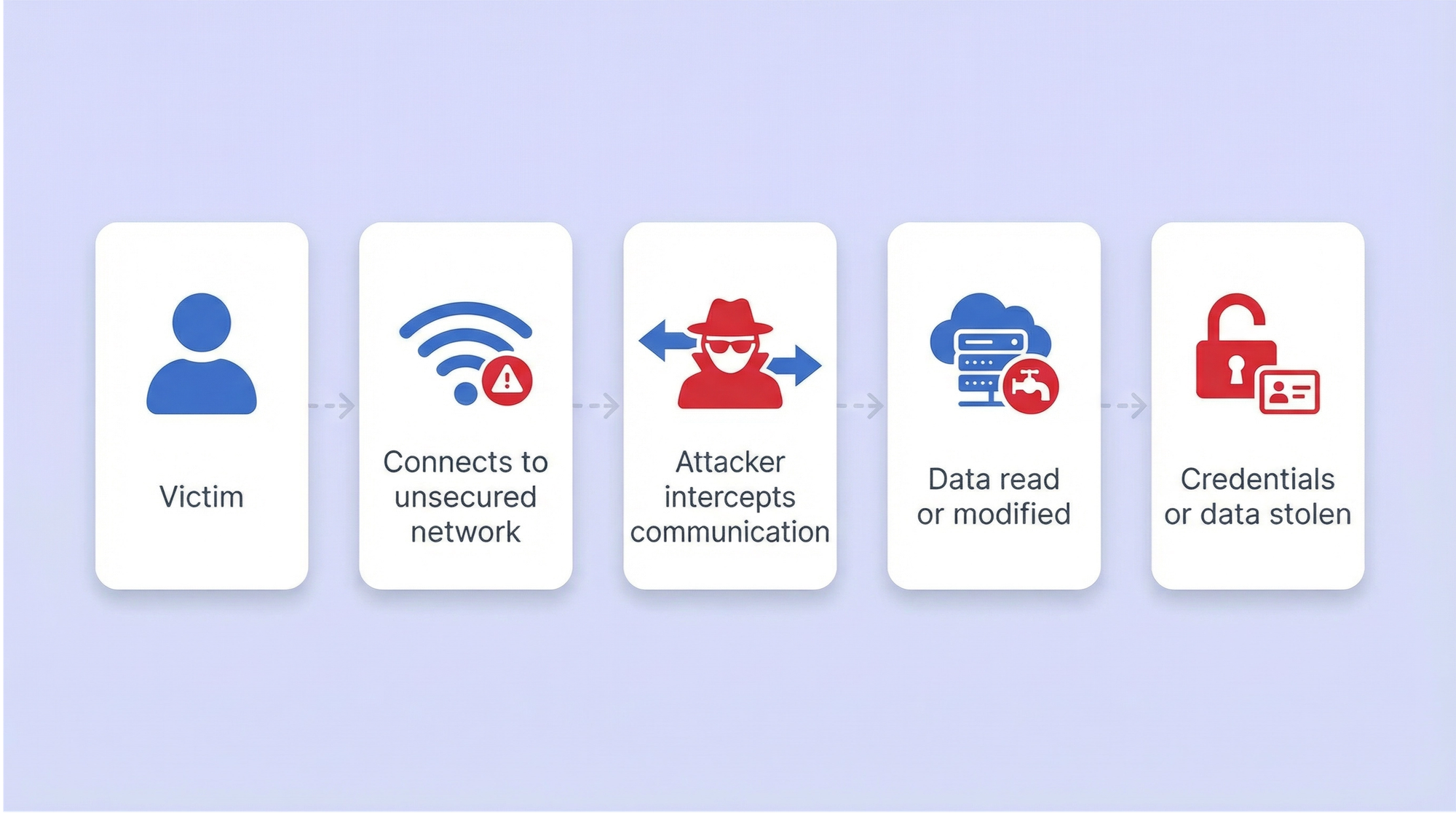
A Man-in-the-Middle (MitM) attack occurs when an attacker intercepts communication between a user and a legitimate service. This can happen on unsecured public Wi-Fi networks, through rogue access points, or via DNS cache poisoning. The attacker captures the traffic, extracting plaintext passwords or session tokens as they travel across the network.
The modern evolution of this technique is the Adversary-in-the-Middle (AiTM) proxy attack. Attackers use reverse proxies to seamlessly relay traffic between the victim and the real authentication server. When the user enters their password and MFA code, the proxy captures the resulting authenticated session cookie, allowing the attacker to bypass MFA entirely.
Defense relies on robust encryption and network security. Enforce HTTPS and TLS 1.3 across all internal and external communications. Require the use of corporate VPNs when employees connect from public or untrusted networks. To defeat AiTM attacks, deploy phishing-resistant FIDO2 authentication, which validates the origin of the request and prevents session token theft.
9. Social engineering
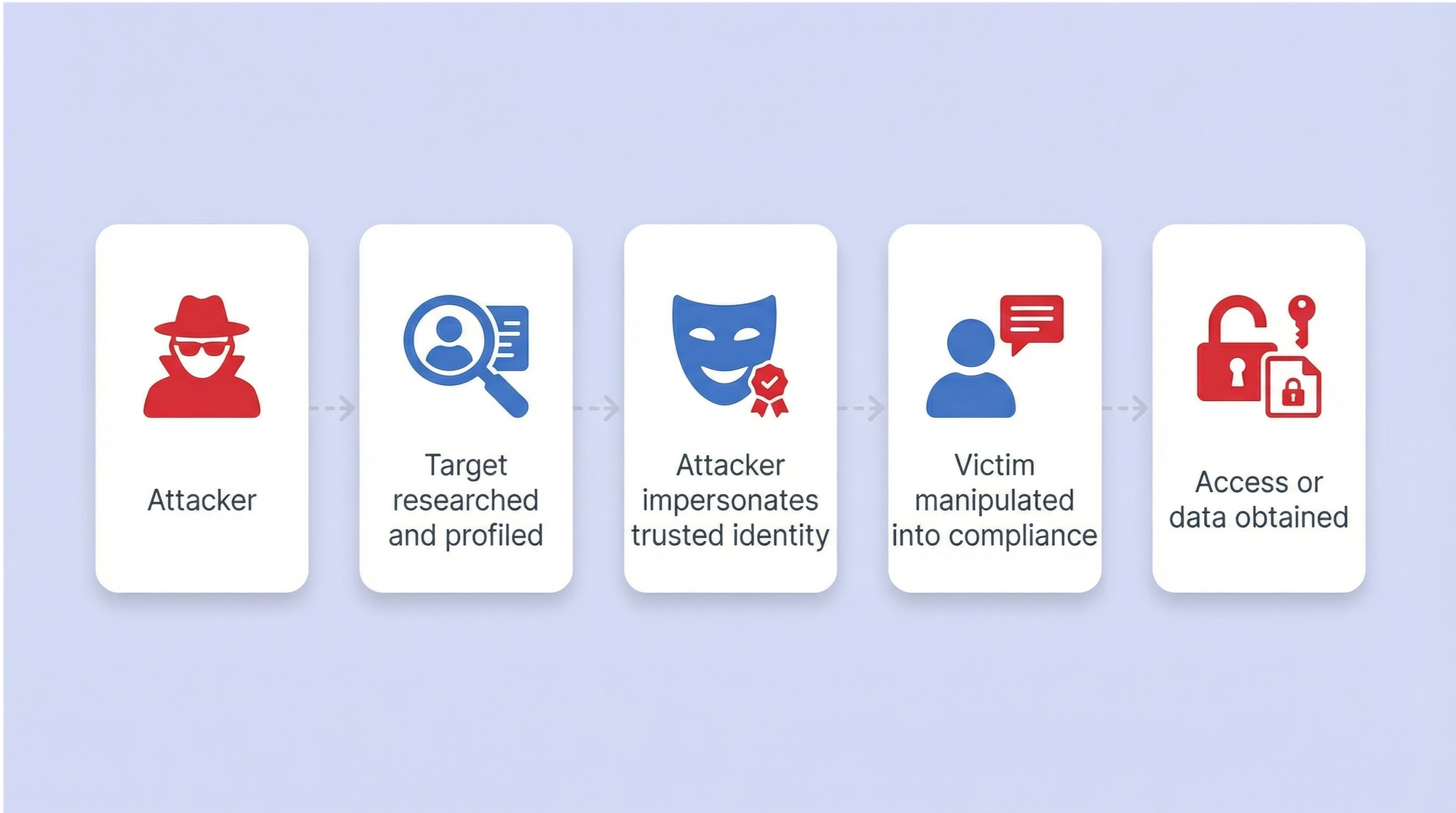
Social engineering attacks target the human layer of security. Attackers use pretexting, impersonation, and psychological manipulation to bypass technical controls. A common tactic involves calling the IT service desk, impersonating a legitimate employee, and requesting an urgent password reset.
Research from Specops Secure Service Desk highlights that helpdesk agents are frequent targets for these attacks. Attackers gather personal information from LinkedIn or other public sources to answer basic security questions, convincing the agent to hand over temporary credentials or reset an MFA device.
Defending against social engineering requires strict, verifiable protocols. Service desks must implement rigorous identity verification procedures that do not rely on easily discoverable public information. Security awareness training should extend to IT staff, focusing on the tactics used to manipulate support personnel. Implement Zero Trust access policies to limit the blast radius if an account is compromised through human error.
10. Hybrid attack
A hybrid attack combines the speed of a dictionary attack with the thoroughness of a brute force approach. Attackers take a known base word — often a company name, a season, or a previously leaked password — and append or prepend numbers, symbols, and years.
This technique is exceptionally effective against post-breach password resets. When forced to change a compromised password like “Atlanta2024!”, a user will predictably change it to “Atlanta2025!”. Attackers know this behavior and configure their cracking tools to test these incremental variations automatically.
Defense requires strict password history policies. Active Directory and identity providers must be configured to block incremental variations of previous passwords. Organizations should move away from arbitrary password expiration policies, which encourage users to create predictable, iterative passwords, and instead focus on continuous breached password monitoring.
11. Pass-the-Hash (PtH) and Kerberoasting
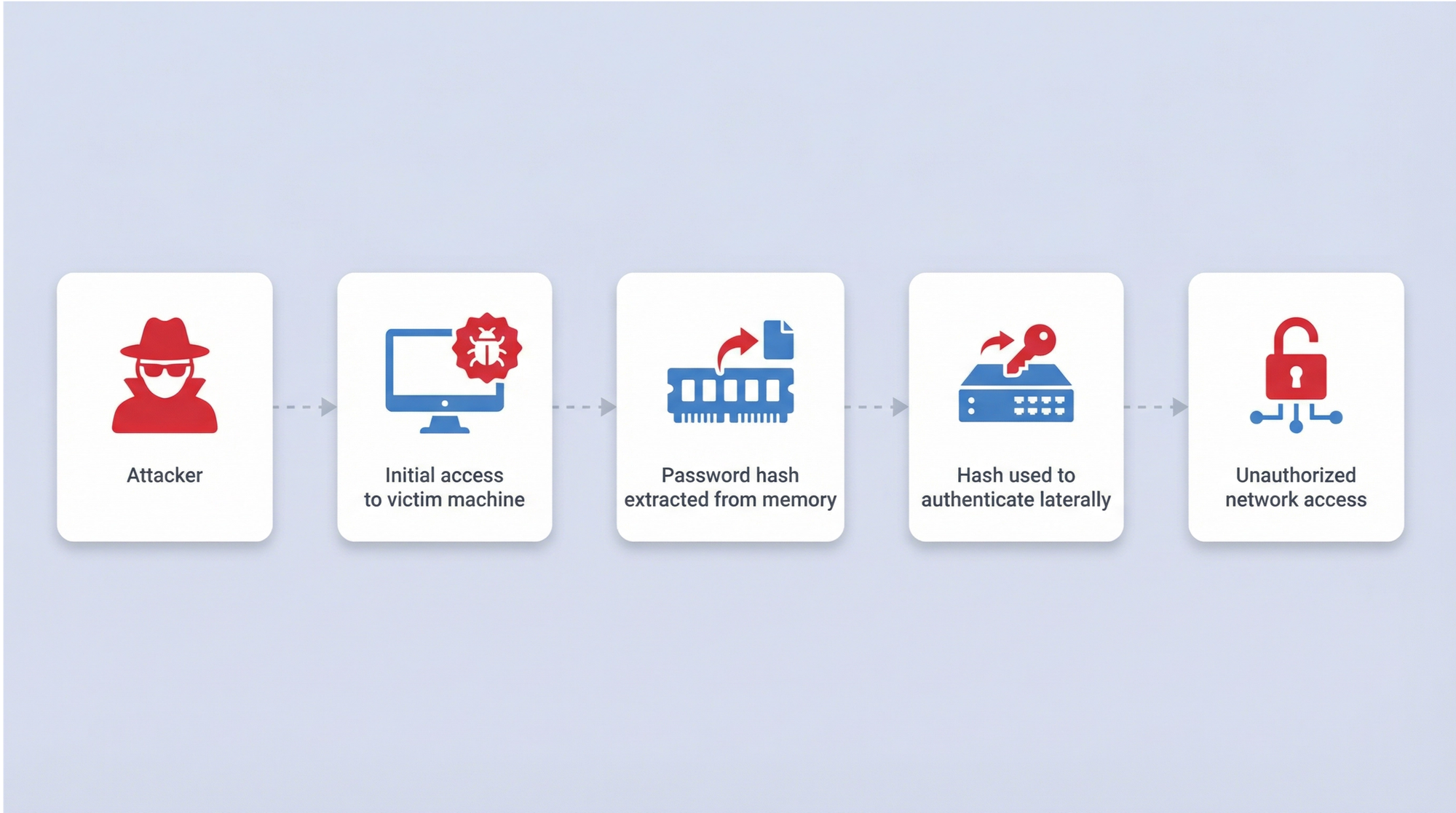
Pass-the-Hash (PtH) and Kerberoasting are advanced techniques specifically targeting enterprise Active Directory environments. In a PtH attack, an adversary extracts the NTLM hash of a user’s password from a compromised machine’s memory using tools like Mimikatz. They then use this hash to authenticate to other network resources without ever needing to crack the plaintext password.
Kerberoasting targets service accounts. Any authenticated domain user can request a Kerberos service ticket for a Service Principal Name (SPN). The attacker extracts this ticket and takes it offline, attempting to crack the service account’s password hash at their leisure. Because service accounts often have high privileges and rarely change their passwords, they are prime targets.
Defending against these lateral movement techniques requires strict control over privileged accounts. Adhere to the principle of least privilege. Passwork allows teams to securely manage shared administrative passwords using a Role-Based Access Control (RBAC) model, ensuring that critical hashes are not compromised due to careless storage. Monitor network traffic for unusual Kerberos ticket requests. Transition to Group Managed Service Accounts (gMSAs), which automatically rotate complex passwords, eliminating the risk of offline Kerberoasting.
12. AI-powered password guessing
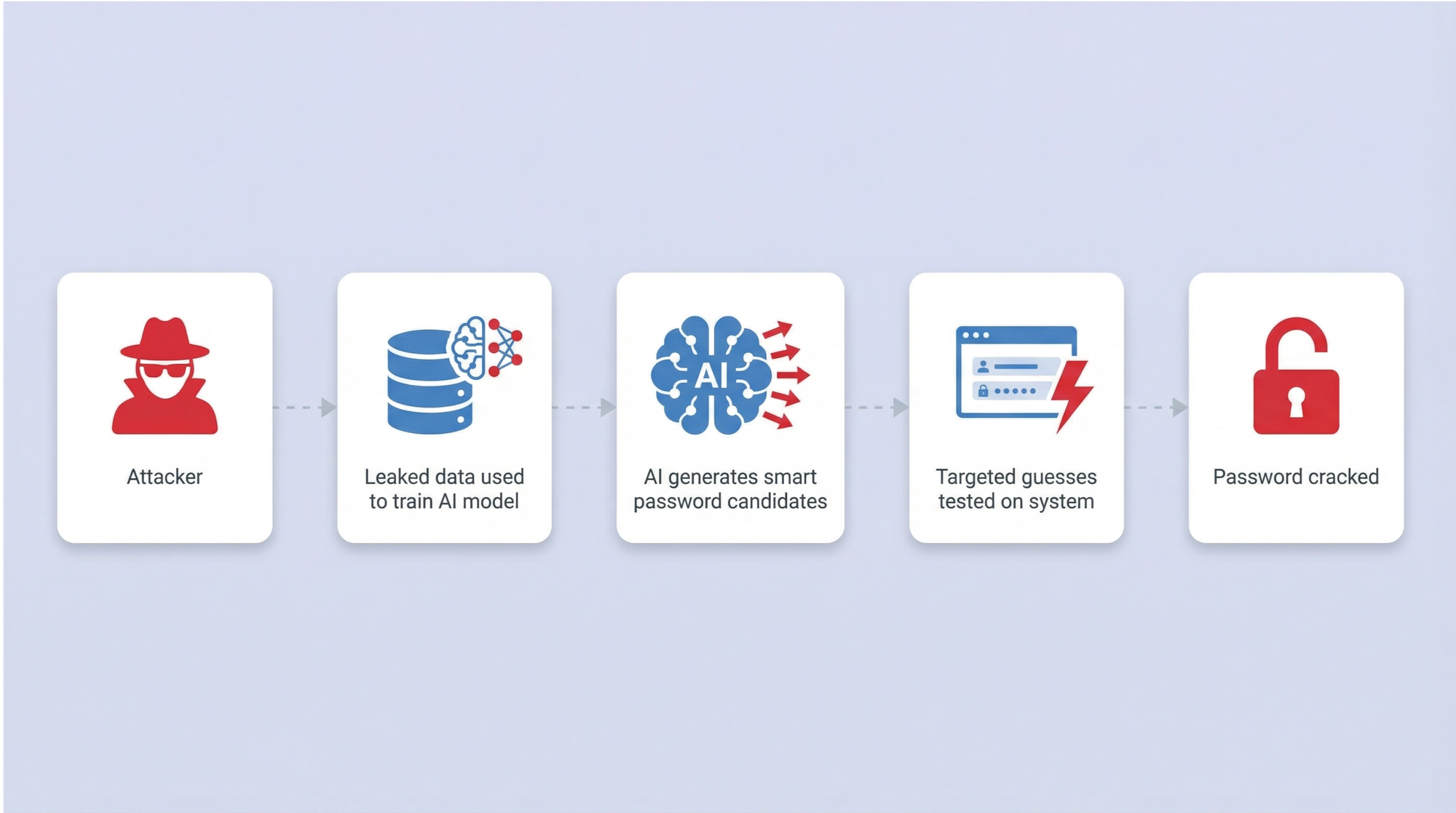
Artificial Intelligence has fundamentally altered the password cracking landscape. Tools like PassGAN use Generative Adversarial Networks (GANs) trained on massive datasets of leaked credentials. Instead of relying on static wordlists or rigid mutation rules, these neural networks learn the underlying psychology of how humans construct passwords. They generate statistically likely candidates with terrifying accuracy.
When AI generation is combined with high-speed hashing tools like Hashcat, the overall success rate of cracking campaigns increases dramatically. AI tools complement traditional methods, filling the gaps where dictionary rules fail.
Defense against AI-powered guessing requires passwords that lack human patterns entirely. Organizations must mandate the use of password managers to generate and store passwords of 15 or more characters with true cryptographic randomness. Combine this with robust MFA and continuous breached password monitoring to mitigate the threat of AI-generated guesses.
How hackers prioritize their targets
Attackers operate with a clear economic model, prioritizing techniques based on efficiency, scale, and the value of the target. Credential stuffing and phishing are the preferred methods for mass exploitation. Because stolen credentials sell for as little as $10 on criminal markets, the return on investment for automated stuffing campaigns is exceptionally high.
When attackers acquire a database of hashed passwords, they turn to dictionary attacks and AI-powered guessing, reserving resource-intensive brute force attacks for high-value administrative accounts. Infostealer malware is deployed selectively against targets likely to yield access to corporate networks, cryptocurrency assets, or proprietary source code.
Time is always on the attacker’s side. Check Point found that organizations take an average of 94 days to remediate compromised credentials exposed in GitHub repositories. Attackers exploit this window aggressively, using automated scripts to validate and weaponize leaked secrets within minutes of exposure. Understanding this prioritization helps defenders allocate their resources effectively, focusing on the attack vectors that present the highest statistical risk.
How to protect your organization against password cracking
Securing an enterprise against modern password cracking requires a comprehensive, layered defense strategy. Technical controls must align with human behavior to create a resilient authentication environment.
- Enforce strong, unique passwords
Length matters more than complexity. Following NIST SP 800-63B guidance, organizations should require passwords of at least 12 characters. Because humans cannot memorize dozens of long, random strings, provide an enterprise password manager to generate and store truly random credentials for every service. - Deploy Multi-Factor Authentication (MFA)
MFA is mandatory, but not all MFA is equal. Prioritize phishing-resistant authentication methods like FIDO2 security keys or passkeys. Move away from SMS-based One-Time Passwords (OTPs), which are highly vulnerable to SIM swapping and AiTM proxy attacks. - Monitor for breached credentials
The Verizon 2025 DBIR notes that only 3% of passwords meet NIST complexity requirements. Organizations must continuously check employee passwords against known breach databases. If a credential appears in a public dump, the system should force an immediate reset. - Implement privileged access management
Protect service accounts and shared credentials, which are the primary targets for lateral movement attacks like Pass-the-Hash and Kerberoasting. Restrict administrative access and log all privileged sessions. - Conduct security awareness training
Social engineering and phishing remain the most common initial access vectors. Regular, contextual training and simulated phishing tests measurably reduce employee susceptibility to credential harvesting lures. - Deploy a centralized enterprise password manager
Security policies work effectively when employees have convenient tools to follow them. Implementing an enterprise password manager like Passwork solves the human factor problem.
Passwork provides teams with an encrypted vault featuring granular Role-Based Access Control (RBAC), detailed audit logs, and seamless Active Directory/SSO integration. For companies with strict compliance requirements, Passwork offers an on-premise version, allowing organizations to host all encrypted data exclusively on their own servers and eliminate the risks associated with cloud breaches.
Conclusion
The threat landscape has shifted fundamentally. Password cracking has evolved from a niche technical skill into an industrialized, AI-assisted, and MaaS-enabled attack category. The 2025 data is unambiguous: stolen credentials drive the vast majority of corporate breaches, and the tools available to attackers have never been more powerful or accessible. Relying on outdated complexity rules and manual password management is a guaranteed path to compromise.
The most effective organizational response requires a holistic approach. It combines strong password hygiene, phishing-resistant MFA, continuous breach monitoring, and a centralized password management platform.
Are you ready to protect your corporate infrastructure against modern cracking techniques? Discover how Passwork helps enterprise teams securely store, generate, and manage corporate passwords with complete control over their data.
Frequently asked questions

What is the most common password cracking technique in 2025?
Credential stuffing is the most prevalent technique at scale, accounting for a median 19% of all daily authentication attempts according to the Verizon 2025 DBIR. Phishing was the most common initial breach vector, responsible for 16% of confirmed breaches, as reported in the IBM 2025 Cost of a Data Breach Report.
How long does it take to crack a password?
It depends entirely on length, complexity, and the hashing algorithm used. Kaspersky’s analysis of 193 million real-world passwords found that 59% could be cracked in under one hour using a modern GPU and smart guessing algorithms. An 8-character alphanumeric password can be cracked by an RTX 4090 in approximately 17 seconds. Passwords of 15 or more truly random characters would take centuries to crack with current hardware.
To guarantee the use of such cryptographically strong passwords without sacrificing productivity, organizations should rely on built-in password generators provided by solutions like Passwork.
What is the difference between a brute force and a dictionary attack?
A brute force attack tries every possible character combination systematically, which is thorough but slow. A dictionary attack uses a precompiled list of likely passwords, including common words, leaked credentials, and OSINT-derived terms. Dictionary attacks are far faster in practice because most real-world passwords follow predictable human patterns.
Can AI crack passwords?
Yes. AI-powered tools like PassGAN use neural networks trained on real password datasets to generate statistically likely guesses. Research shows PassGAN can crack 51% of common passwords in under one minute and 65% within one hour — significantly outperforming traditional dictionary attacks on their own.
Does multi-factor authentication prevent password cracking?
MFA significantly raises the bar, but it is not a complete defense. Adversary-in-the-Middle (AiTM) attacks can intercept MFA tokens in real time. Phishing-resistant FIDO2 or passkey authentication is the current gold standard for preventing credential-based attacks.

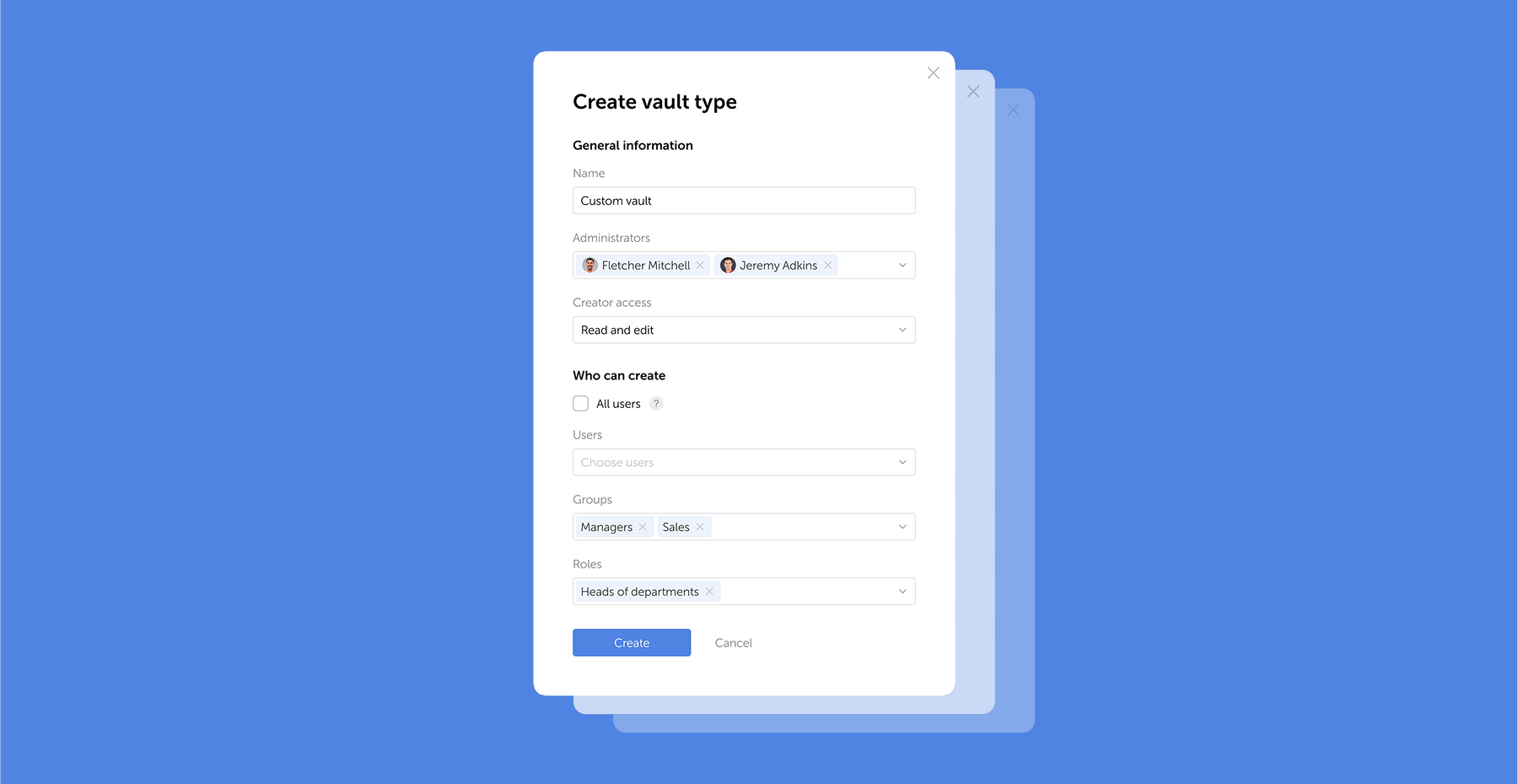
Table of contents
Table of contents
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more



