
Privileged access management (PAM) is a cybersecurity solution designed to protect an organization's most valuable assets: privileged accounts. As organizations increasingly face threats such as data breaches and unauthorized access, PAM provides the tools needed to secure these high-value credentials.
Privileged accounts are user accounts with elevated permissions that grant access to critical systems, sensitive data, and administrative functions — far beyond what standard users can reach. This category includes administrator accounts, service accounts, root access, and other high-privilege credentials. Because of the level of control they carry, these accounts represent the highest-value targets for attackers: a single compromised privileged account can give an adversary full control over infrastructure, applications, and data.
PAM addresses this risk through a set of security strategies and technologies for controlling, monitoring, and auditing privileged accounts. This guide explores PAM, its core components, and how it helps organizations reduce security risks by keeping their most sensitive credentials under strict, verifiable control.
Understanding privileged access
Privileged access denotes a heightened level of permissions granted to users, enabling them to perform administrative tasks and access critical systems across the organization. These accounts are commonly described as the master keys to the IT infrastructure of the organization.
If they are compromised, attackers gain the ability to modify configurations, exfiltrate sensitive data, and cause widespread damage to operations.
To mitigate this risk, the Principle of least privilege is applied. It ensures that users are granted only the minimum level of access necessary for their role. By limiting the permissions for accounts, organizations can reduce the attack surface and heighten security.
Types of privileged access you need to secure
Privileged accounts fall into three primary categories, each carrying distinct risks.
- Administrative accounts hold the broadest access — they control system configurations, user permissions, and critical infrastructure. A compromised admin account effectively hands an attacker the keys to the entire environment.
- Service accounts operate in the background, running automated tasks, scheduled jobs, and system processes without direct human interaction. Because they rarely get the same scrutiny as user accounts, they often become overlooked attack vectors.
- Application accounts are provisioned for specific software to function with the permissions it requires — connecting to databases, calling APIs, or accessing file systems.
The accounts often have privileged credentials, such as passwords, SSH keys, or API tokens, that provide access. PAM solutions focus on securing these credentials and managing access to these accounts to prevent unauthorized activities.
What are privileged credentials?
Privileged credentials are the authentication data that grant access to privileged accounts. They include passwords, API keys, SSH keys, and other sensitive tokens. A password manager stores and protects these credentials, enabling secure, centralized management.
Credential vaults handle both traditional passwords and DevOps secrets (API keys, SSH keys, certificates) within a single platform. This unified approach helps avert the fragmentation IT teams often experience when juggling separate password management and secrets management tools. We designed Passwork to deliver enterprise deployment options that cover password plus secrets management in one solution. Learn more about our on-premise and cloud deployment options.
Non-human privileged access
In IT environments, non-human privileged access is becoming increasingly important. Service accounts, application accounts, and other machine identities often outnumber human accounts. The accounts often require specific management approaches, especially when dealing with automation and API access.
PAM solutions for non-human access centralize the management of privileged credentials, including API keys and service-account tokens. The following approach strengthens security across all privilege levels while keeping CI/CD pipelines and other automation workflows running smoothly.
The true cost of compromised privileges
The financial and reputational impact of a breach that involves privileged accounts can be devastating. Privileged threat vectors, such as credential theft, privilege escalation, and insider threats can lead to data breaches and severe legal consequences. Investing in privileged access management (PAM) solutions significantly reduces security risks.
Harden privileged credentials and implement tight access controls to stop unauthorized privilege escalation. PAM solutions centralize the management of privileged accounts, and limits the number of users with administrative access. This helps mitigate the risk of data breaches, insider threats, and system misconfigurations by reducing the attack surface and monitoring the activities of those with elevated permissions.
According to Microsoft, PAM solutions help organizations safeguard critical systems by monitoring, detecting, and preventing unauthorized access to resources. The potential impact of compromised credentials is reduced as a result.
PAM vs. Related Identity Management concepts
Privileged access management (PAM) is a critical component of an organization's cybersecurity strategy, designed to protect privileged accounts. While PAM focuses on securing and monitoring privileged access to sensitive systems, it should not be confused with related identity management concepts such as Privileged identity management (PIM), Privileged user management (PUM), and Privileged session management (PSM).
- Identity governance forms the foundation of PIM, which manages privileged accounts throughout their lifecycle and ensures only authorized users receive elevated permissions.
- Monitoring user behavior and enforcing security policies define PUM's approach to implementing the Principle of least privilege across privileged operations.
- Through session recording and real-time monitoring, PSM provides forensic evidence and detects privileged threat vectors during active administrative sessions.
PAM integrates with broader Identity and access management (IAM) frameworks, but it is tailored to the unique risks associated with privileged accounts. PAM focuses on the critical aspect of privileged access security. Together, PAM and IAM ensure protection for all types of access across the organization.
| Concept | Definition | Primary focus | Key capabilities |
|---|---|---|---|
| PAM | Security for user accounts | Securing all privileged credentials and sessions | Credential vaulting, session monitoring, access workflows, privilege elevation |
| PIM | Identity-centric privileged access | Managing privileged identity lifecycle | Identity provisioning, governance, certification |
| PUM | User behavior and policy enforcement | Monitoring privileged user activities | Activity tracking, policy enforcement, behavioral analytics |
| PSM | Monitoring and recording privileged sessions | Session control and forensics | Session recording, keystroke logging, real-time monitoring |
Privileged identity management (PIM)
Privileged identity management (PIM) is a subset of PAM focused on the governance of privileged identities within the Identity and access management (IAM) framework. PIM ensures that privileged accounts are properly managed throughout their lifecycle, limiting access according to the Principle of least privilege. If integrated with IAM, PIM provides identity governance, which means that users’ elevated permissions are granted only when necessary and are strictly monitored.
Privileged user management (PUM)
Privileged user management (PUM) focuses on the human aspect of managing privileged accounts. It involves monitoring user behavior. By tracking privileged accounts and their usage patterns, PUM helps organizations prevent unauthorized privilege escalation, so only authorized personnel can access critical systems and data.
Privileged session management (PSM)
Privileged session management (PSM) plays a role in detecting privileged threat vectors by tracking session activity, logging keystrokes, and identifying anomalous behaviors. Through session monitoring and forensic capabilities, PSM helps prevent and mitigate potential security breaches related to privileged accounts.
Why organizations need privileged access management
The need for Privileged Access Management (PAM) arises from the growing risks associated with privileged accounts. These accounts represent significant vulnerabilities in an organization's security posture, as they provide elevated access to sensitive systems. With PAM, organizations can protect against external privileged threat vectors and mitigate insider threats.
PAM helps reduce security risks by enforcing the Principle of least privilege. This strategy both minimizes the risk of privilege escalation and helps organizations meet regulatory compliance requirements such as GDPR, PCI DSS, and HIPAA.
The implementation of PAM improves operational efficiency by offering centralized management of privileged credentials. It also reduces complexity of managing access controls across different systems. Additionally, PAM allows organizations to monitor and audit privileged accounts, so mitigate potential security threats become easier to identify.
Organizations that deploy PAM can also benefit from the flexibility of on-premise or cloud-based solutions.
Common privilege threat vectors
Privileged threat vectors refer to the various methods that attackers use to exploit weaknesses in privileged accounts and privileged credentials.
- Credential theft: Passwords or keys are stolen by the attackers as they gain unauthorised access.
- Privilege escalation: Attackers elevate their access rights to gain more control over critical systems.
- Lateral movement: Once inside the network, attackers move across systems using compromised privileged accounts to extend their reach.
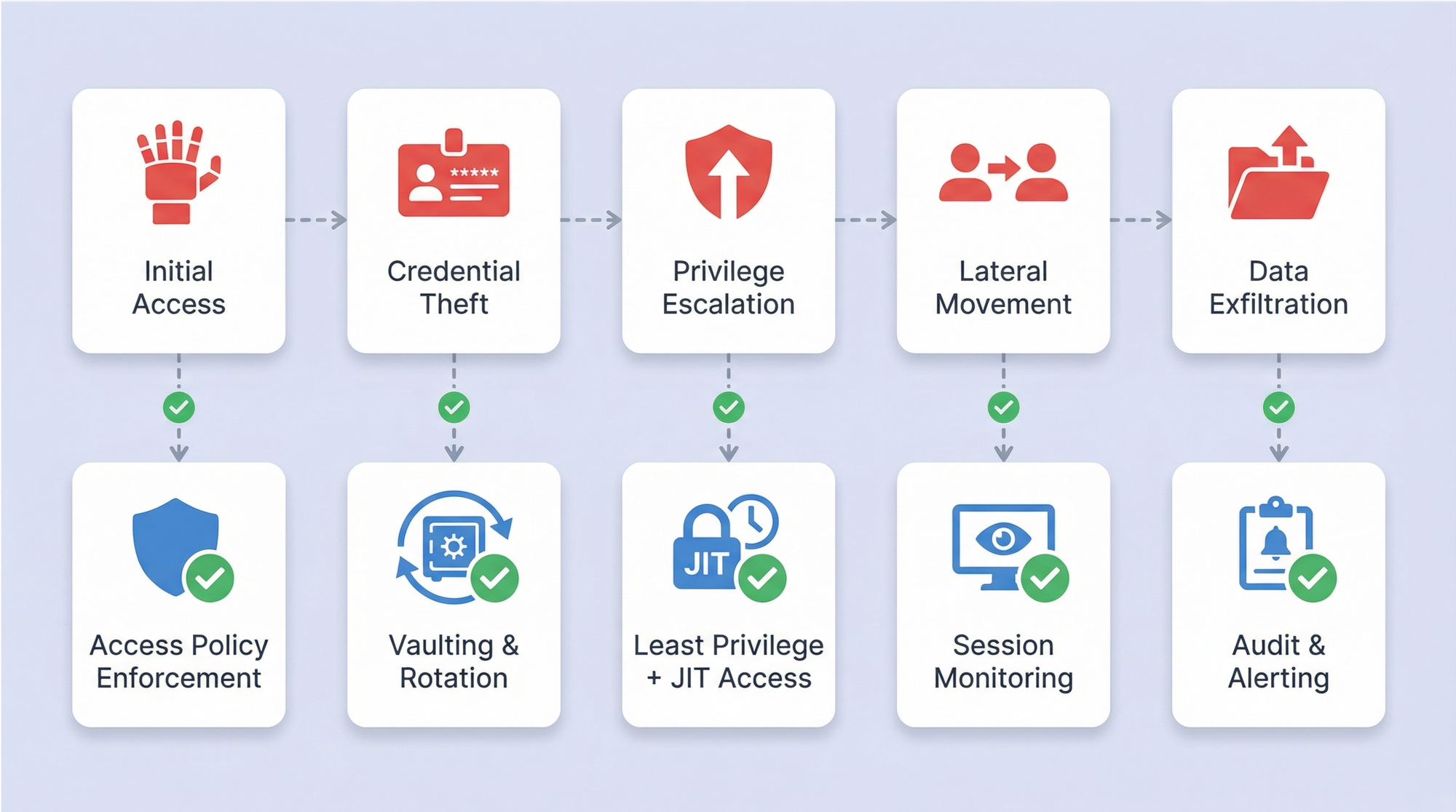
PAM helps mitigate these threats by protecting privileged credentials.
Key benefits of PAM implementation
- Risk reduction: By securing privileged accounts, PAM reduces the likelihood of unauthorized access and privileged escalation.
- Regulatory compliance: PAM helps organizations meet industry standards such as GDPR, HIPAA, and PCI DSS.
- Operational efficiency: PAM simplifies the management of privileged credentials and ensures that access is only granted when necessary.
- Improved audit capabilities: With session monitoring and logging, PAM provides detailed audit trails for compliance purposes.
Building the business case for PAM
To build a business case for PAM, consider the security, operational, and financial benefits. They include the reduction in privileged threat vectors, the prevention of data breaches, and the improvement in overall security posture. Usually, ROI presentation is based on risk reduction, compliance achievements, and the visibility of privileged accounts can help secure executive sponsorship for PAM implementation.
PAM and compliance: meeting regulatory requirements
PAM helps organizations align with various regulatory standards. It directly addresses the strict access rules found in PCI DSS and HIPAA, while also supporting the risk-based security measures required by GDPR and the internal control audits necessary for SOX. To demonstrate this compliance, PAM ensures that all privileged activity is monitored and logged.
Core components of Modern PAM Software
A PAM solution consists of several critical components:
- Password vaults: Secure storage for privileged credentials help ensure safe access and management.
- Session monitoring real-time is helpful in detecting potential hacker attacks.
- Least privilege enforcement to minimize access risks.
- Audit and reporting helps to ensure transparency and support regulatory requirements.
By integrating these components, PAM solutions provide protection for privileged accounts and privileged credentials.
Privileged account discovery and management
Finding all privileged accounts across servers, cloud platforms, and endpoints forms the foundation of secure governance. PAM builds a complete, continuous inventory of these credentials. To keep the environment safe, the system handles regular password rotation and formal access certification. Since configurations and assets change often, continuous discovery prevents security blind spots.
Privileged session monitoring and management
For forensic analysis, PAM records exactly how privileged accounts are used. Real-time monitoring spots anomalies as they happen, which allows you to detect threats immediately. While access controls restrict who can view these recordings, the logs themselves provide data for investigations. This visibility helps stop misuse of elevated access in networks before it becomes a major incident.
Privileged elevation and delegation
Permanent admin rights maintain high risk. By using just-in-time access, you enforce the principle of least privilege. The system delivers temporary accounts through workflow approvals only when needed. These elevations last for a limited time and revoke automatically once the work is done. This approach balances security with operational needs, reducing exposure without slowing down workflows.
PAM and Zero Trust architecture
Zero trust rests on the idea of never trusting and always verifying. PAM supports this by enforcing the least privileges and continuous verification of privileged accounts. Context-aware policies check device posture and behavior before granting access. Integration points include policy engines and identity brokers to enable secure access across hybrid environments.
Common PAM implementation challenges and solutions
Deploying PAM reveals a consistent set of hurdles for enterprises. Older applications often fail to support contemporary authentication standards. The complexity increases with distributed infrastructure, where on-premise hardware, multi-cloud environments, and SaaS platforms all utilize distinct mechanisms for privileged access.
| Challenge category | Specific issues | Proven solutions |
|---|---|---|
| Legacy system integration> | Applications requiring hardcoded credentials; systems lacking API support | Credential injection via scripts; privileged session management as proxy; gradual migration strategies |
| IAM/directory integration | Inconsistent identity sources; multiple AD forests; cloud identity providers | Federated identity management; LDAP synchronization; SSO integration |
| DevOps and cloud | Fast-paced deployments; ephemeral infrastructure; secrets in code | Secrets management integration; API-driven credential retrieval; container-native approaches |
| User adoption | Workflow disruption concerns; perceived loss of productivity | Executive sponsorship; phased rollout; training programs |
Technical integration issues and solutions
Integrating a PAM tool requires seamless connectivity with existing Identity and Access Management (IAM) frameworks to ensure consistent policy enforcement. Technical hurdles often arise when managing accounts across hybrid cloud environments or outdated legacy architectures. To mitigate these risks, architects should prioritize solutions that offer broad application compatibility and robust API support.
DevOps and cloud environments: unique PAM challenges and solutions
Dynamic DevOps workflows and cloud-native architectures introduce distinct hurdles for PAM. Service accounts proliferate rapidly across CI/CD pipelines, containerized workloads, and automation scripts — each carrying privileged credentials that demand protection. Hardcoded API keys and static secrets embedded in repositories remain a persistent vulnerability. Integrating PAM with secrets management and dynamic credential injection addresses these risks.
PAM nest practices from industry experience
Successful PAM deployments follow a structured, phased approach grounded in documented security frameworks. The principle of least privilege serves as the cornerstone — every privileged account receives only the minimum permissions required for its designated function.
Governance over privileged credentials demands continuous oversight: automated rotation schedules, real-time session monitoring, and periodic access reviews all contribute to a resilient security posture. Balancing technical rigor with organizational readiness remains essential for sustained adoption.
| Deployment Model | Key Advantages | Ideal Use Cases | Implementation Considerations |
|---|---|---|---|
| On-Premise | Full data sovereignty, deep legacy integration | Regulated industries, air-gapped networks | Higher infrastructure costs, dedicated maintenance teams |
| Cloud | Rapid scalability, reduced overhead | Distributed workforces, multi-cloud environments | Vendor dependency, network latency concerns |
| Hybrid | Flexibility across environments | Organizations mid-migration | Complex synchronization, unified policy enforcement |
Implementing Least Privilege Access
Applying the principle of least privilege through PAM starts with mapping every privileged account to its specific operational role. Role-based access control provides the structural framework, assigning right-sized permissions that match each user's actual responsibilities. Periodic access reviews are critical — without them, privilege creep gradually expands permissions beyond what any account genuinely needs, widening the attack surface over time.
Maturing your PAM implementation
Based on available resources and risk appetite, security teams move through defined levels of maturity. You should start with basic credential vaulting and storing shared admin passwords in encrypted containers. From there, the process moves to automation, which includes policy-based rotation, approved workflows, and connecting to Active Directory.
For enterprise-scale deployments, deep account discovery and DevOps secrets management become necessary. Managing passwords between applications also plays a key role at this stage. Finally, full operational maturity requires just-in-time access and linking with SIEM platforms to detect behavioral anomalies.
Measuring PAM success: KPIs and metrics that matter
To evaluate the effectiveness of PAM implementations, organizations should track specific KPIs:
- Risk reduction: Measured by the decrease in privileged threat vectors and security breaches.
- Operational efficiency: Monitoring improvements in accounts management, including reduced manual efforts.
- Compliance achievement: Meet regulatory standards like GDPR and PCI DSS.
These metrics help demonstrate PAM's value in enhancing security and reducing risk.
Conclusion: Securing organizations' most powerful access

PAM is a critical solution for securing accounts and privileged credentials from privileged threat vectors. By enforcing the Principle of least privilege, PAM helps prevent unauthorized access, mitigate security risks, and meet compliance standards. Organizations should consider deploying PAM to safeguard their most sensitive systems and data.
Frequently asked questions

What is privileged access management (PAM)?
Security teams use PAM to manage access to user accounts through three core mechanisms: credential vaulting, session monitoring, and least privilege enforcement.
What does privileged access management do?
Organizations use PAM to limit access, monitor privileged account usage, and manage credentials like passwords and SSH keys. These controls prevent unauthorized access to sensitive systems, and ensure compliance with industry standards like GDPR, PCI DSS, and HIPAA.
What are the benefits of privileged access management?
PAM improves security by reducing privileged threat vectors, helps organizations meet regulatory compliance, improves accounts governance, and improves operational efficiency by centralizing the management of privileged credentials.
What are privileged accounts?
Privileged accounts are accounts that grant elevated access to critical systems or sensitive data. For example, administrator or service accounts are targeted by attackers because of their elevated permissions and access to core infrastructure.
How does PAM work?
Encrypted credential vaults store privileged passwords and SSH keys, controlling access through granular permissions and session monitoring. When users need elevated access, time-based policies grant temporary privileges that automatically expire and implement least privilege principles.
What is an example of PAM?
An example of PAM is the use of a password manager to securely store and manage privileged credentials like administrative passwords, SSH keys, and API tokens. Access to these credentials is granted on a just-in-time basis, with detailed session monitoring.
What are privileged credentials?
Privileged credentials are the authentication data (passwords, API keys, SSH keys) that provide access to privileged accounts. These credentials need to be secured and properly managed to prevent unauthorized access and privilege escalation.
Why is PAM needed?
PAM is necessary to prevent unauthorized access to privileged accounts, mitigate privileged threat vectors, and meet compliance requirements. It ensures that sensitive data is protected by enforcing strict access controls and monitoring user behavior.
What are common privilege threat vectors?
Common privileged threat vectors include credential theft, privilege escalation, and insider threats. The vulnerabilities allow attackers to gain unauthorized access to privileged accounts and perform malicious actions.
How does privileged access management support a zero trust security model?
Through continuous verification of privileged accounts, PAM supports a zero-trust posture. Access is granted only under the principle of least privilege, with ongoing monitoring of all activities to ensure verification. In practice, PAM enforces the “never trust, always verify” mindset by correlating real-time access events with policy checks and alerting on deviations.
Table of contents
- Understanding privileged access
- PAM vs. Related Identity Management concepts
- Building the business case for PAM
- Core components of Modern PAM Software
- Common PAM implementation challenges and solutions
- PAM nest practices from industry experience
- Measuring PAM success: KPIs and metrics that matter
- Conclusion: Securing organizations' most powerful access
- Frequently asked questions
Table of contents
- Understanding privileged access
- PAM vs. Related Identity Management concepts
- Building the business case for PAM
- Core components of Modern PAM Software
- Common PAM implementation challenges and solutions
- PAM nest practices from industry experience
- Measuring PAM success: KPIs and metrics that matter
- Conclusion: Securing organizations' most powerful access
- Frequently asked questions
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more
