
Three things happened in April 2026 that don't look connected — until you see the pattern.
APT28 hijacked 18,000 routers across 120 countries and redirected authentication traffic through an adversary-in-the-middle proxy. No malware. Just a TLS certificate warning that most users dismissed. Microsoft 365 credentials and OAuth tokens collected at the midpoint, MFA bypassed entirely.
A developer at an AI productivity startup got infected by a commodity infostealer. The malware cost roughly $200 on a darknet forum. It extracted a browser-stored OAuth token, handed it to attackers, and within hours they were inside Vercel's production environment — enumerating API keys, database credentials, and signing keys.
ShinyHunters pulled authentication tokens from a third-party analytics provider called Anodot and spent the day monetizing access to dozens of downstream platforms. Vimeo. Zara. Snowflake customers. None of the primary platforms were compromised directly. The attack ran entirely through the integration layer.
The common thread: the breach never started where the damage ended. Every attacker entered through a peripheral — a vendor, an integration, a forgotten device — and pivoted to the real target from there.
This digest covers the credential and authentication incidents that defined April 2026, the statistics that give them context, and what they collectively mean for how organizations manage access.
Key takeaways
- APT28 hijacked 18,000 routers across 120 countries to steal Microsoft 365 OAuth tokens. The FrostArmada campaign required no malware and left almost no visible trace — DNS settings were silently overwritten to redirect authentication traffic through an adversary-in-the-middle proxy. MFA was bypassed entirely. The FBI dismantled the infrastructure in April 2026.
- Storm-2372 bypassed MFA at scale without stealing a single password. The campaign abused the OAuth Device Code flow, using AI-generated role-specific lures to trick victims into authorizing attacker-controlled sessions. The toolkit (EvilTokens) automated the entire operation end-to-end.
- The Anodot breach exposed stored tokens for dozens of downstream platforms. ShinyHunters extracted authentication tokens from a third-party analytics provider and used them to access customer data at Vimeo (119,000 users) and Zara/Inditex (197,000 records). Snowflake was not compromised — the attack ran entirely through the integration layer.
- A commodity infostealer on one developer's device was sufficient to breach Vercel's production environment. Lumma Stealer compromised Context.ai, a peripheral AI vendor. Inherited OAuth access gave attackers direct entry into Vercel systems — no zero-day, no phishing of Vercel staff required.
- A malicious Bitwarden CLI package circulated via npm for 94 minutes. Attackers hijacked a GitHub Action in the CI/CD pipeline and injected a payload targeting developer secrets, cloud credentials, and AI coding tool configurations — with built-in self-propagation across reachable repositories.
- AI-assisted development drove secret leaks to a record 28.6 million in 2025 — up 34% year-over-year. AI-service credential leaks grew 81%. Commits co-authored by AI tools leak secrets at roughly twice the baseline rate. 64% of secrets exposed in 2022 remained active and exploitable in 2026.
- Every major incident this month followed the same pattern. The primary target was never the ultimate victim — attackers moved through a peripheral vendor, a stored token, or a compromised dependency to reach the real objective. MFA did not stop any of the credential theft campaigns. The attack surface is the integration layer, the CI/CD pipeline, and the OAuth grant.
APT28: DNS hijacking campaign FrostArmada disrupted by international authorities

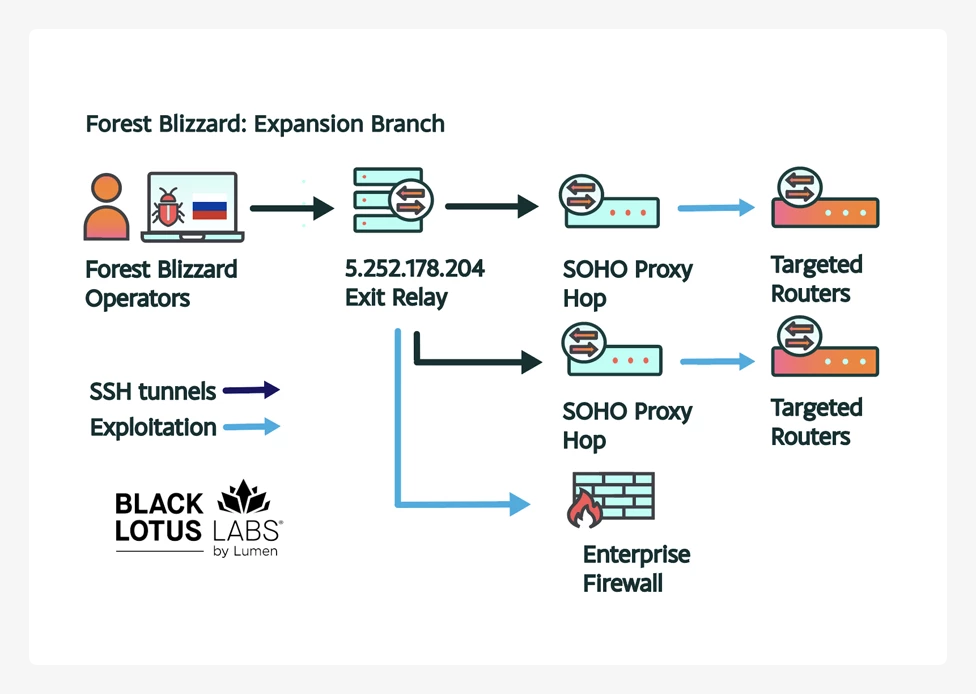
An international law enforcement operation involving the FBI, the U.S. Department of Justice, and the Polish government, with technical support from Microsoft and Black Lotus Labs, dismantled FrostArmada: an APT28 campaign that hijacked router DNS settings to steal Microsoft 365 credentials and OAuth tokens. Active since May 2025, the campaign infected 18,000 devices across 120 countries at its peak in December 2025.
What happened
APT28 (also tracked as Fancy Bear, Forest Blizzard, Strontium, and Storm-2754) — attributed by the NCSC and the U.S. DoJ to Russia's GRU military unit 26165 — compromised internet-exposed SOHO routers by exploiting known public vulnerabilities. The primary target was the TP-Link WR841N via CVE-2023-50224, which allowed unauthenticated attackers to extract router credentials via a crafted HTTP GET request, then overwrite DHCP/DNS settings with a second request.
The attack chain worked as follows:
- Router is compromised via a known vulnerability; DNS settings are overwritten to point to attacker-controlled VPS nodes
- New DNS configuration is automatically pushed to all internal devices via DHCP — laptops, phones, everything on the network
- When a user queries an authentication-related domain, the malicious DNS server returns the attacker's IP instead of the real one
- User is redirected to an adversary-in-the-middle (AitM) proxy
- The proxy passes requests through to the legitimate service — while silently collecting passwords and OAuth tokens at the midpoint
- The only visible warning to the victim: a TLS certificate error, easily dismissed
The approach required minimal end-user interaction and left almost no visible trace. Black Lotus Labs described it as "all thriller, no malware filler."
How the campaign evolved
The earliest activity was limited and began in May 2025. The inflection point came on August 5, 2025, when the NCSC published its Authentic Antics report describing a Forest Blizzard toolset for stealing Microsoft Office credentials. Lumen detected widespread router exploitation and DNS redirection starting the very next day (August 6) confirming rapid tradecraft adaptation after public exposure.
This pattern is consistent with Forest Blizzard's broader history. The group has continuously evolved its credential theft methods since at least 2021: from brute-force password spraying against Microsoft services, to NTLM hash harvesting via compromised routers, to full AitM infrastructure. The group is also known to deploy the LLM-based tool "LAMEHUG" alongside more traditional techniques.
How the infrastructure was organized
Black Lotus Labs identified two distinct operational clusters:
- Expansion team — focused on compromising new SOHO routers and growing the botnet at scale, targeting a large pool of networking equipment via exposed web interfaces
- AitM cluster — handled credential and token collection; also conducted interactive operations against specific MikroTik routers
The DNS hijacking was opportunistic by design: cast a wide net, then filter intercepted traffic to triage victims of likely intelligence value at each stage of the chain.
Targets and scope
The campaign primarily targeted government agencies, ministries of foreign affairs, law enforcement bodies, IT and hosting providers, and organizations running on-premise email servers. Microsoft confirmed AitM attacks against Microsoft 365 subdomains, including Outlook on the web. Black Lotus Labs and the NCSC also observed targeting of government organizations in North Africa, Central America, and Southeast Asia including "a national identity platform in one European country."
The takedown
The FBI carried out a court-authorized technical operation, remotely resetting DNS configurations on compromised routers to point back to legitimate resolvers. The operation was tested extensively on affected TP-Link firmware to ensure it did not impact normal router functionality or collect user data.
Lumen blocked traffic to the affected infrastructure and added indicators of compromise into Lumen Defender. Routers can be fully cleaned by restoring factory default settings. TP-Link confirmed the scope in an official statement:
"TP-Link has conducted an internal review and identified that multiple legacy TP-Link products may be affected by this vulnerability. Except for TL-WR940N v6 (EOS since 2024), all affected products have reached End-of-Life (EOL) status and no longer within TP-Link's standard maintenance lifecycle."
In practice, this means no patches are coming — replacement is the only remediation path for affected hardware.
What to do
Priority actions for network and security teams:
- Replace any routers that no longer receive firmware updates — end-of-life hardware was the primary entry point
- Verify DNS resolver settings in your router configuration and check against known-good values from your ISP
- Implement certificate pinning on corporate devices managed via MDM — this generates an error when an AitM proxy attempts traffic inspection
- Review firewall rules to prevent unwanted exposure of remote management interfaces
- Monitor Microsoft Entra sign-in logs for anomalous OAuth token usage patterns
Storm-2372 AI phishing: Massive MFA bypass via Device Code
Microsoft documented a large-scale phishing campaign by Storm-2372 that bypassed MFA without stealing a single password. The attack abused the OAuth Device Code authentication flow — a legitimate mechanism designed for devices that cannot support interactive logins — to trick users into authorizing attacker-controlled sessions. The campaign was powered by EvilTokens, a phishing-as-a-service toolkit that automated the entire operation end-to-end.
How it worked
The attack unfolded in three phases:
- Reconnaissance: 10–15 days before phishing, the group verified target account validity via Microsoft's GetCredentialType endpoint.
- Delivery: generative AI produced hyper-personalized lure emails tailored to each target's role — RFPs for procurement staff, invoices for finance teams, manufacturing workflow notifications for operations. Redirect chains ran through Vercel, Cloudflare Workers, and AWS Lambda to blend with legitimate enterprise traffic.
- Token capture: when a victim clicked the link, a background script generated a live Device Code in real time — bypassing the standard 15-minute expiration window. The victim completed MFA on Microsoft's real login page, unknowingly authorizing the attacker's session.
Post-compromise activity focused on high-value targets: email exfiltration, malicious inbox rules for persistence, and Microsoft Graph reconnaissance to map organizational structure and permissions.
Targets and scope
The campaign targeted organizations across government, finance, manufacturing, and IT sectors. Post-compromise activity was not indiscriminate: threat actors used automated enrichment — cross-referencing public profiles and corporate directories — to triage compromised accounts and prioritize individuals in financial or executive roles for deeper exploitation.
Post-compromise activity
Once tokens were obtained, attackers focused on maintaining access and extracting data. This included email exfiltration, creation of malicious inbox rules to redirect or conceal communications, and Microsoft Graph reconnaissance to map organizational structure and permissions — enabling lateral movement for as long as the stolen tokens remained valid.
What to do
- Disable Device Code flow for users and applications that don't require it via Conditional Access policies
- Monitor for anomalous GetCredentialType endpoint queries and unusual token issuance patterns
- Implement token lifetime policies and continuous access evaluation to limit stolen token validity windows
- Treat role-specific AI-personalized lures as a documented threat vector — generic awareness training is insufficient
Anodot token leak: Vimeo, Zara and dozens more hit in ShinyHunters campaign

Over a dozen companies suffered data theft after authentication tokens were stolen from Anodot, an AI-based analytics provider acquired by Glassbox in November 2025. The majority of attacks targeted Snowflake customer environments. Among the confirmed victims: Vimeo (119,000 users affected) and Zara's parent company Inditex (197,000 records exposed). The Snowflake platform itself was not breached — the attack ran entirely through the third-party integration layer.
What happened
Anodot provides real-time anomaly detection for business and operational data, integrating directly with Snowflake, S3, Amazon Kinesis, and other platforms. To function, it stores authentication tokens on behalf of its customers. When Anodot's environment was breached, those stored tokens gave attackers direct access to downstream customer data — no vulnerability in Snowflake itself was required.
The ShinyHunters extortion group claimed responsibility, telling BleepingComputer they stole data from dozens of companies on a single Friday using tokens harvested from Anodot. The group also hinted they may have had access to Anodot for some time before acting. ShinyHunters subsequently attempted to use the same stolen tokens against Salesforce customer accounts — but was detected and blocked by AI-based detection before succeeding.
Snowflake responded by locking down potentially impacted customer accounts and notifying affected organizations. Anodot's status page showed all connectors down across all geographic regions from the weekend of the incident. Neither Anodot nor its parent company Glassbox responded to press inquiries at time of publication.
Confirmed victims
Vimeo confirmed that the Anodot breach exposed user and customer data — primarily technical data, video titles, metadata, and in some cases email addresses. In its official disclosure, Vimeo stated:
"The data accessed does not include Vimeo video content, valid user login credentials, or payment card information. Vimeo user and customer login credentials are secure. Upon learning of the incident, we promptly disabled all Anodot credentials, removed the Anodot integration with Vimeo systems, and engaged third-party security experts to assist with the investigation."
According to Have I Been Pwned, 119,200 unique email addresses were exposed, sometimes accompanied by names. ShinyHunters published hundreds of gigabytes of Vimeo data after listing the company on their "pay or leak" extortion portal.
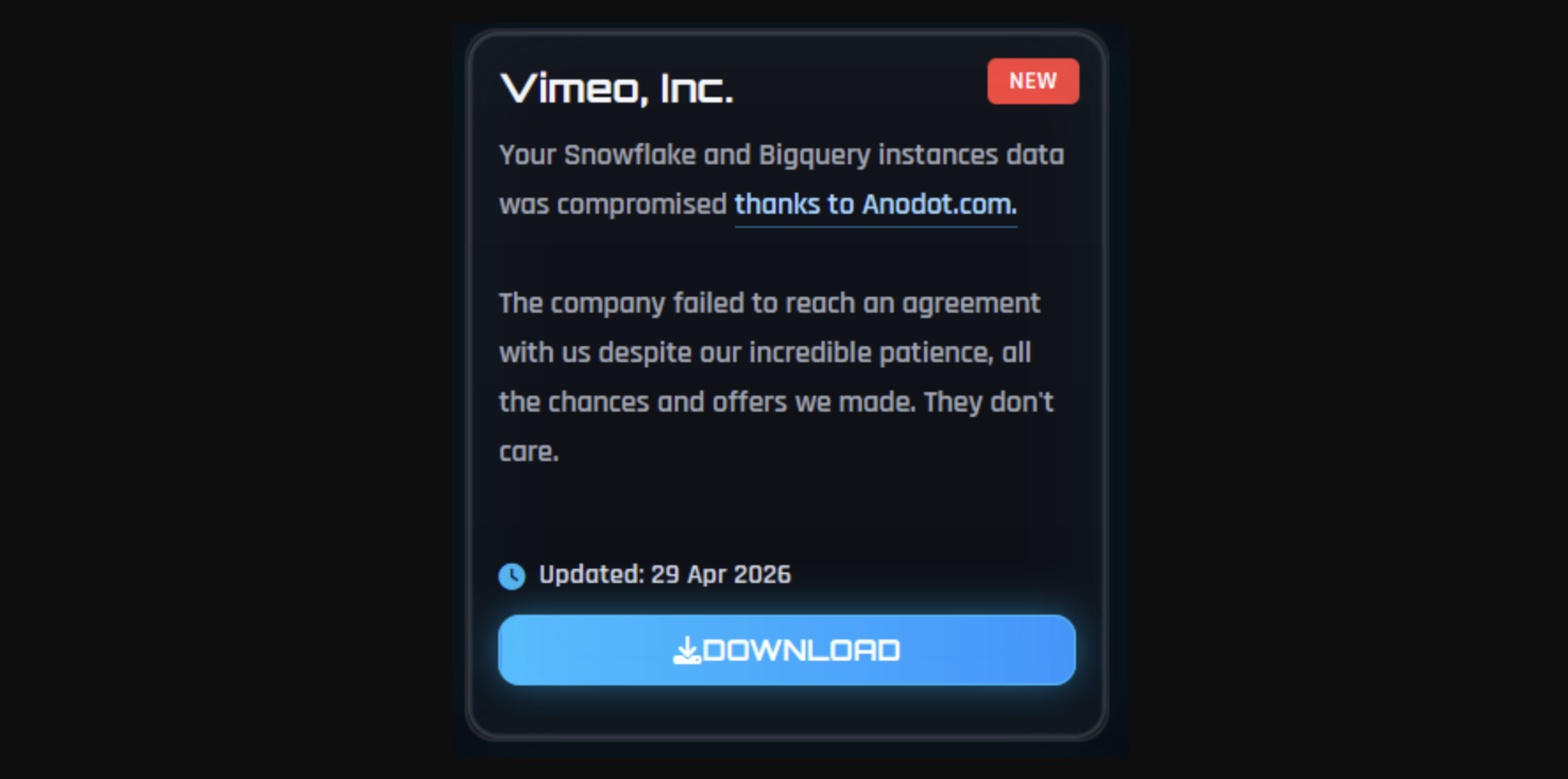
Zara (Inditex) was also listed by ShinyHunters as part of the same campaign. The group published what they claimed was a terabyte of data, allegedly including 95 million support ticket records. Have I Been Pwned recorded 197,400 unique email addresses in the breach, alongside product SKUs, order IDs, and geographic market data. Inditex confirmed the incident but stated it did not affect passwords or payment information.
Why it matters
This incident is a structural risk, not a one-off event. SaaS-to-SaaS integrations routinely involve credential delegation: one service authenticates on behalf of another, storing long-lived tokens with broad permissions. That authorization is granted once and rarely reviewed. When the delegated service is compromised, every downstream connection it holds becomes an attack vector — and the primary platform has no visibility into or control over the breach.
The ShinyHunters playbook is consistent: identify a peripheral integration service, compromise it, extract stored tokens, and monetize access through extortion before victims can respond.
What to do
- Maintain a current inventory of all third-party SaaS integrations and the credentials they hold on your behalf
- Apply least-privilege scoping to all OAuth grants and API tokens issued to external services
- Set token expiration policies — avoid indefinite long-lived tokens for third-party integrations
- Conduct periodic access reviews and revoke authorizations for services no longer in active use
- Treat integration provider security posture as part of your vendor risk assessment process

Unreviewed third-party integrations and long-lived tokens are a structural risk, not an edge case. Passwork gives security teams a centralized inventory of credentials with role-based access and a full audit trail — so nothing persists unnoticed. See how it works
Vercel: Supply chain attack via OAuth and Lumma Stealer

A Vercel employee used Context.ai — a third-party AI productivity tool — connected to their corporate Google Workspace account via OAuth. When Context.ai was compromised, attackers inherited that OAuth access, took over the employee's Vercel account, and pivoted into production systems.
Non-sensitive environment variables — API keys, tokens, database credentials, signing keys — were enumerated and decrypted. Vercel engaged Google Mandiant for forensic investigation and described the attackers as "highly sophisticated based on their operational velocity and in-depth understanding of Vercel's product API surface."
What happened
Trend Micro identified Lumma Stealer as the infostealer used in the initial compromise of Context.ai. Lumma is a commodity malware-as-a-service tool that extracts browser-stored credentials, session cookies, and authentication tokens from infected machines. One infected developer device at a small AI vendor became the entry point for a $2 million data breach at a major cloud platform.
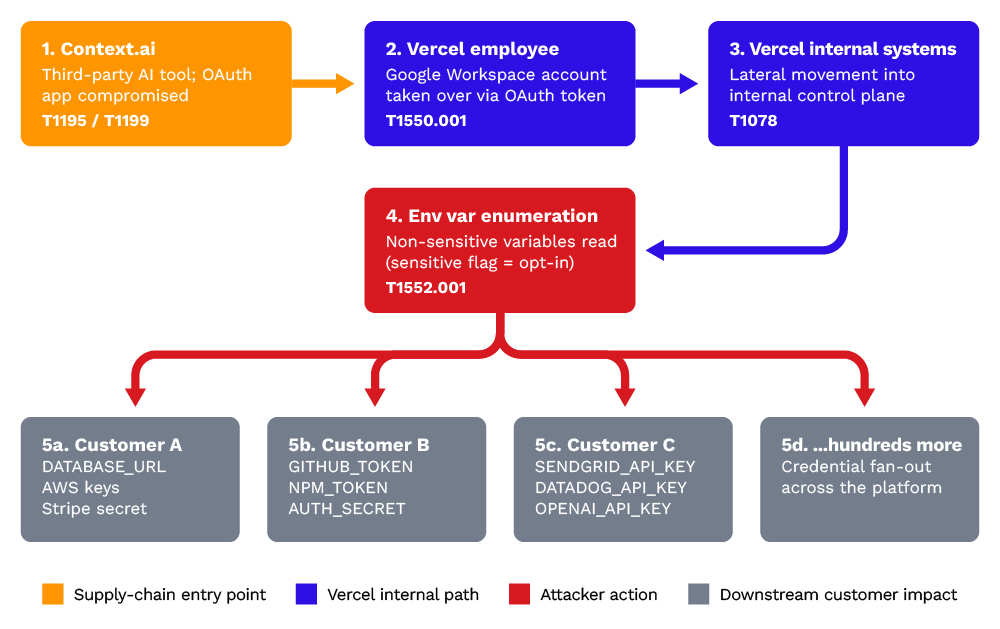
Vercel confirmed that secret environment variables — those explicitly marked as sensitive — were stored encrypted and were not compromised. Non-secret variables were exposed. The company described the attackers as "highly organized" and engaged Mandiant for forensic investigation.
"We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems. We are actively investigating, and we have engaged incident response experts to help investigate and remediate." — Vercel official statement
Why it matters
OAuth grants are easy to create and rarely reviewed. When an employee connects a third-party tool to a corporate account, they typically grant broad permissions in a single click — and that authorization persists indefinitely unless explicitly revoked. Each connected application is a potential pivot point if that application is ever compromised.
The attack chain here required no zero-day, no phishing of a Vercel employee directly, and no vulnerability in Vercel's own code. A commodity infostealer on a developer's machine at a peripheral vendor was sufficient.
What to do
- Audit all OAuth applications connected to corporate Google Workspace and Microsoft 365 accounts
- Enforce policies restricting which third-party applications employees can authorize
- Mark all sensitive environment variables explicitly — and treat non-marked variables as potentially exposed
- Deploy endpoint detection capable of identifying infostealer activity before credential exfiltration occurs
- Rotate all non-sensitive environment variables as a precaution if the Context.ai OAuth app was present in your environment
Bitwarden CLI compromised in Checkmarx supply chain attack
April 22, 2026. The Bitwarden CLI package @bitwarden/[email protected] was distributed with malicious code for 94 minutes — between 5:57 PM and 7:30 PM ET — via a hijacked GitHub Action in Bitwarden's CI/CD pipeline. The compromise is part of the broader Checkmarx supply chain campaign, attributed to the threat actor TeamPCP. Bitwarden confirmed the incident and stated that no end-user vault data was accessed.
What the malicious code did
The injected code executed via a preinstall hook and targeted credentials across multiple surfaces: local environment files and shell history, GitHub Actions secrets, CI/CD pipeline credentials, configuration files for AI coding tools (Claude, Cursor, Codex CLI, Aider, Kiro), and npm tokens. Stolen data was encrypted with AES-256-GCM and exfiltrated to audit.checkmarx[.]cx — a domain impersonating Checkmarx — with a GitHub repository as fallback.
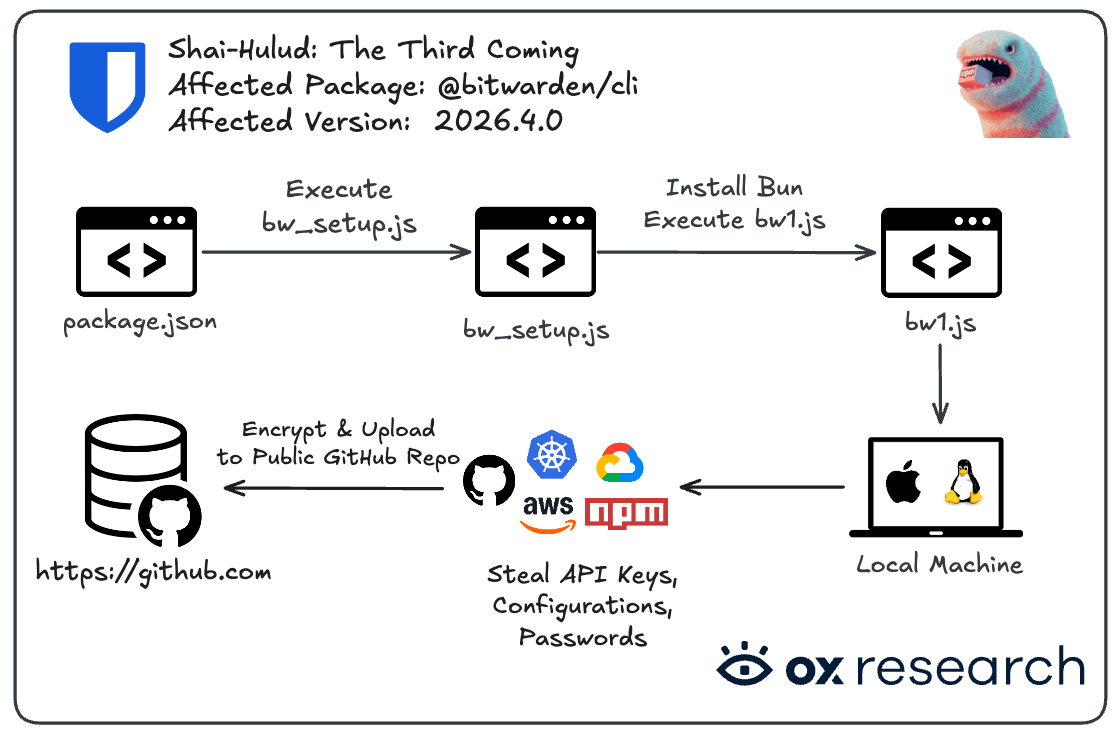
If GitHub tokens were found, the malware injected malicious Actions workflows into every reachable repository and used harvested npm credentials to push further malicious package versions downstream. Endor Labs described it as one of the "more capable npm supply chain payloads" published to date.
What to do
- Pin all CI/CD dependencies — GitHub Actions, npm packages, Docker images — to specific verified commit hashes
- Implement dependency integrity verification (checksums, Sigstore signatures) before installation
- Restrict CI/CD pipeline permissions to the minimum required scope
- If the package was installed during the affected window, rotate all secrets accessible from that environment immediately
GitGuardian: AI agents led to the leak of 29 million secrets
GitGuardian's State of Secrets Sprawl 2026 report found 28,649,024 new secrets exposed in public GitHub repositories in 2025 — a 34% year-over-year increase and the largest annual jump in the report's history. The primary driver: AI-assisted development.
Why AI makes this worse
AI assistants accelerate development to the point where code looks production-ready — and gets committed — before anyone has decided where credentials should live. Commits co-authored by Claude Code leak secrets at roughly twice the baseline rate across public GitHub. A separate risk surface emerged with MCP configuration files: GitGuardian found 24,008 unique secrets exposed in Model Context Protocol configs in 2025.
Key figures
| Metric | 2025 figure |
|---|---|
| New secrets exposed in public GitHub | 28,649,024 |
| Year-over-year growth | +34% (report record) |
| AI-service secrets exposed | 1,275,105 |
| YoY growth of AI-service credential leaks | +81% |
| OpenRouter credential leaks growth | ×48 year-over-year |
| AI services among top 15 fastest-growing leak types | 12 of 15 |
| Secrets in MCP configuration files | 24,008 unique |
| Secrets from 2022 still active and exploitable in 2026 | 64% |
| Internal repos vs. public repos | 6× more likely to contain hardcoded secrets |
| Leaks outside repositories (Slack, Notion, etc.) | 28% of all incidents |
Once a secret is committed to a public repository, it is effectively public — regardless of whether it is later deleted. Automated scanners harvest newly committed secrets within minutes of publication.
What to do
- Implement pre-commit hooks and CI/CD secret scanning to catch credentials before they reach repositories
- Enforce dedicated secrets management tooling (HashiCorp Vault, AWS Secrets Manager) as the only permitted credential storage mechanism
- Rotate any credential that has ever appeared in a public repository, regardless of how briefly
- Establish credential governance policies specifically for AI agent integrations — treat agent identities as first-class access management objects
What April's incidents have in common
Three patterns repeat across every incident this month:
- The primary target was rarely the ultimate victim — attackers moved through a peripheral vendor, a third-party OAuth app, or a compromised CI/CD dependency to reach the real objective.
- MFA provided less protection than assumed — both the Device Code campaign and the OAuth token theft chains bypassed it entirely without touching a password.
- AI accelerated attacker velocity on both sides — generative AI personalized phishing at scale while AI-assisted development created a record volume of exposed credentials.
April 2026 by the numbers: the month in cybersecurity
April 2026 continued the trajectory established earlier in the year — more incidents, broader impact, and attack chains that increasingly bypass traditional controls. Ransomware, credential theft, and supply chain compromise dominated the threat landscape across every sector.
Breach and attack volume
| Metric | Figure | Source |
|---|---|---|
| Countries affected by APT28 FrostArmada DNS hijacking | 120 | Lumen / Black Lotus Labs, April 2026 |
| Devices compromised at peak (December 2025) | 18,000 | FBI / DOJ, April 2026 |
| Records exposed in Anodot token breach (Vimeo + Zara) | 316,000+ | Vimeo / Inditex disclosures, April 2026 |
| Bitwarden CLI malicious version exposure window | 94 minutes | Bitwarden, April 2026 |
| Ransomware incidents tracked in April 2026 | 9+ documented | CM-Alliance, May 2026 |
| Sectors targeted by ransomware in April | Healthcare, government, finance, education, tech | CM-Alliance, May 2026 |
| US data breaches in past 12 months (underground forums) | 758 (13.3% of global total) | BitSight, 2025–2026 |
| Top targeted sector globally | Public administration — 543 breaches (21% of total) | BitSight, 2025–2026 |
Credential and secrets exposure
| Metric | Figure | Source |
|---|---|---|
| New secrets exposed in public GitHub in 2025 | 28,649,024 | GitGuardian, April 2026 |
| Year-over-year growth in secret leaks | +34% | GitGuardian, April 2026 |
| AI-service credentials exposed | 1,275,105 | GitGuardian, April 2026 |
| Secrets from 2022 still active and exploitable | 64% | GitGuardian, April 2026 |
| Secrets exposed outside code repositories | 28% of all incidents | GitGuardian, April 2026 |
Attack techniques in focus
| Technique | Incident | Impact |
|---|---|---|
| DNS hijacking (AitM) | APT28 FrostArmada | Microsoft 365 credential and OAuth token theft at scale |
| OAuth token theft via third-party breach | Anodot → Vimeo, Zara | 316,000+ records; no primary platform compromised directly |
| OAuth supply chain + infostealer (Lumma) | Vercel via Context.ai | Production environment access; non-secret variable exposure |
| CI/CD supply chain (GitHub Actions + npm) | Bitwarden CLI | Credential harvesting across developer environments |
| Device Code phishing (MFA bypass) | Storm-2372 / EvilTokens | Large-scale Microsoft 365 account compromise without password theft |
| AI-accelerated credential sprawl | GitGuardian report | 29M+ secrets in public repos; AI-assisted commits leak at 2× baseline |
Conclusion

April 2026 confirmed a shift that has been building for years: the authentication layer is the primary attack surface, and session tokens are the primary target.
APT28 hijacked 18,000 routers to intercept OAuth tokens without ever touching a password. Storm-2372 bypassed MFA at scale using a legitimate authentication flow. ShinyHunters extracted stored tokens from a third-party analytics provider and monetized access across dozens of downstream platforms — none of which were directly compromised. A commodity infostealer on a single developer's machine at a peripheral vendor was sufficient to reach Vercel's production environment.
The 28.6 million secrets exposed on GitHub, the token theft campaigns run by APT28 and Storm-2372, and the Anodot breach affecting dozens of downstream platforms all point to the same structural gap: access management built for a simpler environment is not keeping pace with how organizations actually operate today.
Protecting credentials now means governing the full lifecycle — issuance, rotation, delegation, and revocation — across human users, service accounts, API keys, and AI agent identities. Shadow IT, unreviewed OAuth grants, and hardcoded secrets in CI/CD pipelines are the attack surface. The perimeter is not.

The incidents in this digest share one structural gap: credentials and tokens that existed outside of governance — unreviewed, unrotated, unrevoked. Passwork provides a self-hosted vault with role-based access control, structured permissions, and a complete audit log. Try Passwork in your infrastructure
Frequently asked questions

What was the most significant cybersecurity threat in April 2026?
The APT28 FrostArmada campaign was the most operationally significant incident of the month. By hijacking DNS settings on over 18,000 unpatched SOHO routers across 120 countries, the Russian GRU-linked group silently intercepted Microsoft 365 credentials and OAuth tokens from government agencies, law enforcement bodies, and IT providers — bypassing MFA without deploying malware or phishing individual users directly.
How does OAuth token theft bypass MFA?
OAuth tokens are issued after a user has already completed authentication — including any MFA step. Stealing the token means inheriting a fully authenticated session. MFA protects the login process; it does not protect the token that results from it. Attackers who intercept or steal tokens skip the login process entirely, rendering MFA irrelevant at that stage.
What is the Device Code phishing technique used by Storm-2372?
Device Code phishing abuses a legitimate OAuth flow designed for input-limited devices. Attackers initiate the flow, then deliver the resulting code to victims via AI-personalized phishing emails. When the victim enters the code at Microsoft's real authentication page, they unknowingly authorize the attacker's session — issuing a valid access token without exposing their password or triggering any MFA challenge. The token is legitimate because the user completed authentication themselves.
Why was the Bitwarden CLI supply chain attack significant?
It demonstrated that security tooling carries the same supply chain risk as any other software dependency. A malicious version of the Bitwarden CLI was distributed via npm for 94 minutes after attackers hijacked a GitHub Action in the CI/CD pipeline. The injected code targeted developer secrets, cloud credentials, and pipeline tokens — and was built to self-propagate to every repository the victim's GitHub token could reach.
What is credential sprawl and why is it accelerating?
Credential sprawl refers to the uncontrolled proliferation of secrets — API keys, tokens, passwords, certificates — across repositories, configuration files, collaboration tools, and CI/CD pipelines. GitGuardian's State of Secrets Sprawl 2026 report found 28.6 million new secrets exposed in public GitHub repositories in 2025, a 34% year-over-year increase driven largely by AI-assisted development. Code reaches production faster than credential governance policies can keep pace — and 64% of secrets exposed in 2022 remained active and exploitable in 2026.



Table of contents
- Key takeaways
- APT28: DNS hijacking campaign FrostArmada disrupted by international authorities
- Storm-2372 AI phishing: Massive MFA bypass via Device Code
- Anodot token leak: Vimeo, Zara and dozens more hit in ShinyHunters campaign
- Vercel: Supply chain attack via OAuth and Lumma Stealer
- Bitwarden CLI compromised in Checkmarx supply chain attack
- GitGuardian: AI agents led to the leak of 29 million secrets
- What April's incidents have in common
- April 2026 by the numbers: the month in cybersecurity
- Conclusion
- Frequently asked questions
Table of contents
- Key takeaways
- APT28: DNS hijacking campaign FrostArmada disrupted by international authorities
- Storm-2372 AI phishing: Massive MFA bypass via Device Code
- Anodot token leak: Vimeo, Zara and dozens more hit in ShinyHunters campaign
- Vercel: Supply chain attack via OAuth and Lumma Stealer
- Bitwarden CLI compromised in Checkmarx supply chain attack
- GitGuardian: AI agents led to the leak of 29 million secrets
- What April's incidents have in common
- April 2026 by the numbers: the month in cybersecurity
- Conclusion
- Frequently asked questions
Self-hosted password manager for business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment. Double encryption and zero-knowledge architecture ensure your passwords never leave your infrastructure.
Learn more



