Introduction
Your security team just renewed the antivirus license. Patches are current. The firewall rules haven't changed in two years — because nothing went wrong. So why do organizations with all of this in place still end up on the breach disclosure list?
Because the tools that worked in 2010 were built for a threat that no longer exists.
Modern attackers don't deliver malware to your endpoints. They acquire a valid set of credentials — through phishing, a leaked database, or a compromised vendor — and authenticate like any other user. From there, they move quietly, escalate privileges, and exfiltrate data over weeks. By the time anyone notices, the damage is done.
Antivirus has no signature for a legitimate login.
This article breaks down what a layered, identity-centric defense actually looks like — and which controls to prioritize if you're building or auditing a security stack in 2026.
Key takeaways
- Traditional, signature-based antivirus misses 82% of modern attacks, which are now malware-free [3]
- Stolen credentials are the leading initial access vector — identity is the new perimeter
- Privileged Access Management (PAM) and enterprise password managers are foundational controls, not optional add-ons
- Zero Trust architecture is the structural answer to lateral movement after a breach
What is a data breach? (The modern definition)
A data breach is any confirmed incident in which sensitive, protected, or confidential information is accessed, disclosed, or exfiltrated without authorization. This includes personally identifiable information (PII), financial records, intellectual property, and protected health information (PHI).
The distinction between a security incident and a confirmed data breach matters operationally.
- Security incident — any event that threatens confidentiality, integrity, or availability. Broad by design, most never escalate further.
- Confirmed data breach — unauthorized access to data is established as fact. This triggers mandatory notification obligations under GDPR Article 33, NIS2 Article 23, and similar frameworks.
That boundary determines your legal exposure, your notification timeline, and whether regulators treat you as a victim or a negligent party.
Why antivirus is no longer enough for data breach prevention
Antivirus software scans files and processes against a database of known malware signatures, then blocks anything that matches. It was the right tool for a threat landscape built around executable files and known virus strains.
Legacy antivirus relies on signature-based detection: if the threat isn't in the database, it isn't detected. That model fails against threats that don't look like malware at all.
According to CrowdStrike's 2026 Global Threat Report, 82% of detections in 2025 were malware-free — meaning attackers used credential abuse, living-off-the-land techniques, and fileless execution that leave no binary footprint for antivirus to scan. Google's Threat Intelligence Team tracked 90 zero-day vulnerabilities exploited in the wild in 2025, each representing an attack window where no signature yet exists.
The 7-layer data breach prevention strategy for 2026

A layered defense model addresses the full attack chain — from initial access through lateral movement to exfiltration. Each layer below is ordered by impact and implementation priority.
1. Enforce phishing-resistant MFA and enterprise password management
Microsoft research confirms that MFA blocks more than 99.2% of account compromise attacks. That single control eliminates the vast majority of credential-based intrusions but only if it's implemented correctly.
SMS-based MFA is vulnerable to SIM-swapping and prompt bombing. Phishing-resistant alternatives — FIDO2 hardware keys, passkeys, and certificate-based authentication — remove the human-intercept vector entirely. These should be the standard for any account with access to sensitive systems.
MFA alone, however, doesn't solve the underlying credential hygiene problem. Employees reuse passwords across personal and corporate accounts, share credentials over chat, and store them in spreadsheets. Verizon's 2025 DBIR found that stolen credentials were the initial access vector in roughly 30% of breaches. An enterprise password manager closes that gap by centralizing credential storage, enforcing strong password policies, and eliminating ad-hoc sharing.
Passwork is purpose-built for this use case. It deploys entirely on your own infrastructure — no credential data ever leaves your environment. All secrets are encrypted with AES-256 on both the server and client sides under a zero-knowledge architecture.
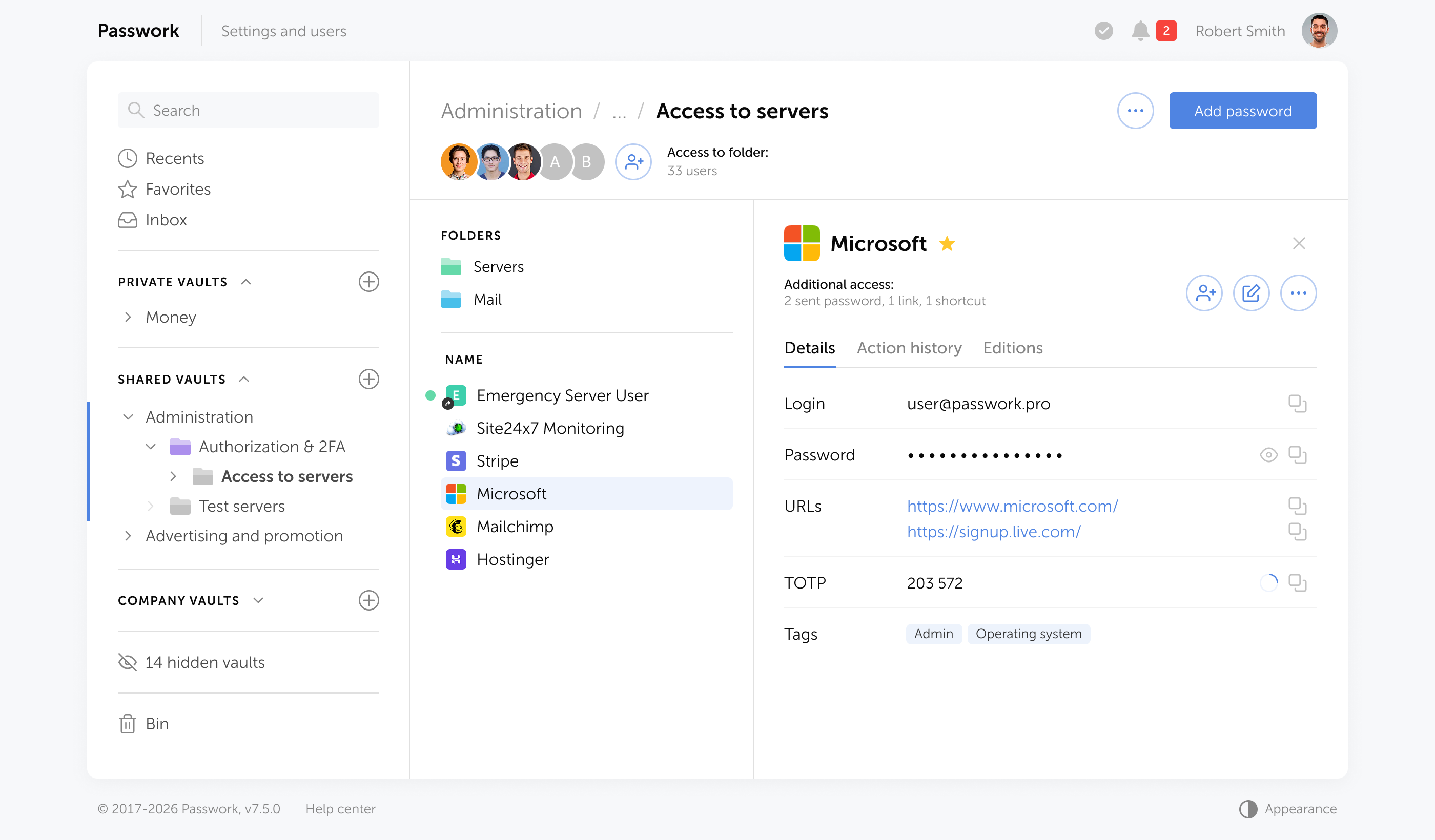
Integration with Active Directory and LDAP automates user provisioning and deprovisioning, so access is revoked the moment an employee leaves. Every credential access, modification, and sharing event is logged in a tamper-evident audit trail — directly addressing insider threat and compliance audit requirements. Passwork holds ISO/IEC 27001 certification, confirming its information security management meets international standards.

Managing shared credentials across teams without a structured vault is one of the fastest paths to a breach. See how Passwork handles enterprise password management → passwork.pro
2. Implement Privileged Access Management (PAM)
Privileged Access Management (PAM) is a security framework that controls, monitors, and audits access to accounts with elevated system permissions — the credentials that, if compromised, give an attacker administrative control over your infrastructure.
PAM governs access to high-value targets: domain controllers, cloud consoles, database servers, and network infrastructure. Beyond access control, it enforces additional session-level security: recording activity, auditing commands, and provisioning access through Just-In-Time (JIT) mechanisms. JIT means admin rights are granted for a defined window and automatically revoked — eliminating standing privileges that attackers can exploit after initial compromise.
The principle of least privilege is the operational foundation: every user, service account, and application receives the minimum access required for its function, and nothing more.
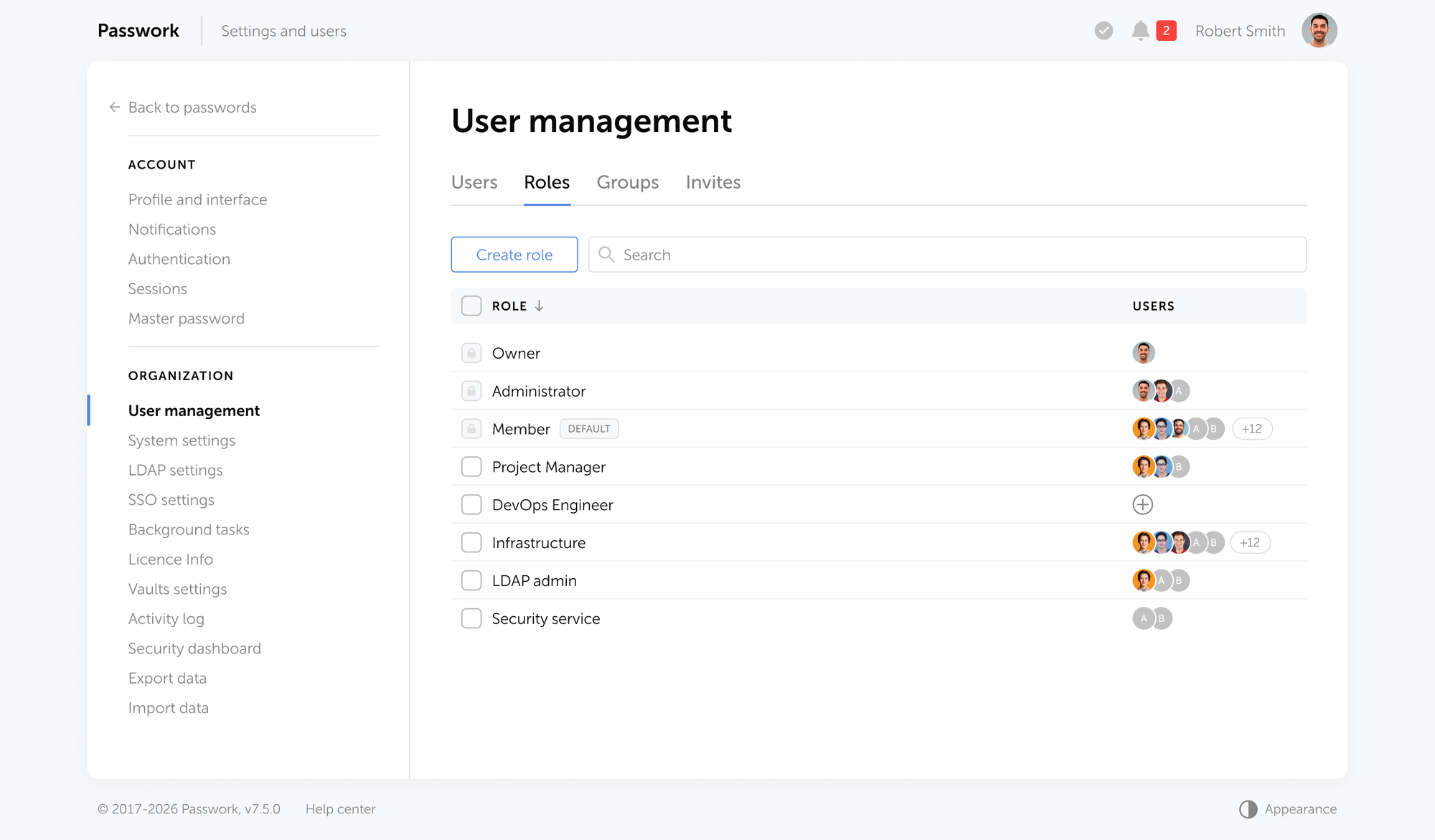
Enforcing least privilege starts at the credential level. Passwork's role-based access model lets administrators assign granular permissions per user or group — controlling exactly who can view, copy, or modify specific credentials.
Each role is fully configurable: rather than choosing between full administrator access and none, you can scope permissions to specific functions — user management, LDAP configuration, audit logs, or vault settings — independently of each other.
3. Adopt a Zero Trust architecture
Zero Trust is a security model built on the assumption that no user, device, or network segment should be trusted by default — regardless of whether the request originates inside or outside the corporate perimeter. Access is granted only after continuous verification of identity, device health, and behavioral context.
The model rests on three core principles:
- Verify explicitly — every access request is authenticated and authorized based on all available data points: identity, device health, location, and behavioral context.
- Use least privilege access — users and systems receive only the permissions required for their current task, limiting the blast radius of any compromise.
- Assume breach — the architecture is designed as if an attacker is already inside. Micro-segmentation, encrypted traffic inspection, and continuous monitoring contain lateral movement before it escalates.
This architecture directly addresses lateral movement. When an attacker compromises one endpoint or account, Zero Trust micro-segmentation and continuous authentication checks prevent them from pivoting to adjacent systems.
Zero Trust is a design philosophy implemented through identity providers, network segmentation, and policy enforcement points — not a single product or vendor solution. NIST SP 800-207 provides the authoritative framework for implementation.
4. Upgrade to Endpoint Detection and Response (EDR)
Endpoint Detection and Response (EDR) is a security technology that continuously monitors endpoint activity — processes, network connections, file system changes, and user behavior — and triggers automated responses when anomalous patterns are detected.
EDR replaces the static signature model with behavioral monitoring. Instead of asking "does this file match a known threat?", EDR asks "does this process behave like an attack?"
That distinction catches fileless malware, credential dumping tools, and ransomware staging activity before execution completes. EDR solutions maintain a continuous telemetry record of endpoint activity, enabling forensic reconstruction after an incident — critical for both containment and compliance reporting.
Ransomware was present in 44% of breaches in 2025, up from 32% the prior year. EDR with automated response capabilities — isolating an endpoint the moment anomalous behavior is detected — is now a baseline control for any organization handling sensitive data.
EDR solutions in practice
- CrowdStrike Falcon — cloud-native agent with real-time behavioral detection, automated containment, and threat intelligence integration
- SentinelOne Singularity Endpoint — autonomous response without cloud dependency; includes rollback capability for ransomware-affected files
- Microsoft Defender for Endpoint — deeply integrated with the Microsoft ecosystem; covers Windows, macOS, Linux, iOS, and Android
- Palo Alto Networks Cortex XDR — extends endpoint telemetry to network and cloud data; unified detection across the full attack surface
- Trend Micro Vision One — combines EDR with XDR across email, endpoints, servers, and cloud workloads
- Sophos Intercept X — includes anti-exploit and anti-ransomware modules alongside behavioral detection; available as a managed service
- Cisco Secure Endpoint — integrates with Cisco's broader security stack; strong on threat hunting and retrospective analysis
5. Deploy Data Loss Prevention (DLP) and encryption
Data Loss Prevention (DLP) is a set of technologies and policies that detect, monitor, and restrict the movement of sensitive data across endpoints, networks, and cloud environments — preventing unauthorized access, transfer, or exfiltration before a breach is confirmed.

DLP tools monitor and control the movement of sensitive data: PII, financial records, source code, and regulated information. They enforce policies that block unauthorized uploads to cloud storage, prevent exfiltration via email, and flag anomalous bulk data transfers.
DLP tools in practice
The market offers solutions across three deployment models — endpoint, network, and cloud — often combined within a single platform:
Endpoint DLP
- Microsoft Purview DLP — native integration with Microsoft 365 and Windows endpoints; covers email, Teams, SharePoint, and local file activity
- Forcepoint DLP — behavior-based detection with deep content inspection across endpoints and web channels
- Digital Guardian (Fortra) — granular endpoint agent with forensic-level logging; strong coverage for intellectual property
Network and cloud DLP
- Netskope DLP — cloud-native; designed for SaaS, IaaS, and web traffic inspection
- Symantec DLP (Broadcom) — covers network, endpoint, and cloud storage with data discovery and classification
- Palo Alto Networks Enterprise DLP — integrated into the NGFW and Prisma SASE stack; no separate agent required
- Varonis — maps sensitive data across file shares, cloud storage, and email; includes anomaly detection on user behavior
Encryption is the complementary control. Data encrypted at rest and in transit remains unreadable even if exfiltrated. Full-disk encryption on endpoints, TLS 1.3 for data in transit, and encrypted backups stored offline form the baseline. For regulated industries, encryption is not optional — NIS2 Article 21 and GDPR Article 32 both reference it as an appropriate technical safeguard.
6. Manage third-party and supply chain risk
Third-party risk is the exposure that enters your environment through vendors, contractors, and software dependencies — entities outside your direct control that nonetheless have access to your systems, data, or codebase. Third-party involvement in breaches doubled year-over-year, according to Verizon's 2025 DBIR.
Vendor risk management requires more than annual questionnaires. Effective controls include:
- Limiting third-party access to only the systems they need
- Requiring MFA for all external accounts
- Monitoring third-party session activity
- Including security requirements in contractual agreements
Supply chain attacks are a distinct and harder-to-detect vector: malicious code is injected into software before it reaches you — through a compromised build pipeline, a tampered package repository, or a hijacked vendor update. By the time the payload arrives, it already looks legitimate. Two incidents from early 2026 illustrate the range of exposure:
- Trivy (March 2026). Aqua Security's vulnerability scanner was compromised through its Docker images, delivering an information-stealing payload to teams that had every reason to trust the tool.
- Axios (March 2026). Attackers linked to North Korean threat actor UNC1069 embedded a remote access trojan inside the widely used Axios npm package and distributed it silently through the dependency chain.
In both cases, malicious code arrived through a trusted channel — before any internal control had a chance to intercept it. Effective defense requires software composition analysis and integrity verification for all third-party components.
7. Conduct continuous security awareness training
The human element was involved in 60% of breaches in 2025. Annual compliance training doesn't change behavior — it produces checkbox completion, not security awareness.
Effective programs run continuous, simulated phishing campaigns calibrated to current attack techniques. When an employee clicks a simulated phishing link, they receive immediate, contextual feedback — not a quarterly reminder.
Gamified platforms that track individual improvement over time produce measurable reductions in click rates. Security culture is built through repetition and relevance, not annual lectures.
How compliance frameworks impact data breach prevention
Compliance frameworks (GDPR, NIS2, DORA, SOC 2) mandate specific technical controls: access logging, encryption, incident response procedures, and vendor management. Meeting these requirements establishes a security baseline.
Compliance defines the minimum acceptable standard — not the appropriate one. A SOC 2 Type II audit confirms that controls existed and operated effectively during the audit period; it makes no statement about what happens the day after the auditor leaves, or whether those controls are sufficient against your actual threat landscape. Organizations that substitute compliance for security strategy tend to find out the difference at the worst possible moment.
Use frameworks as a structured starting point. Build beyond them based on your actual threat model.
What each framework actually requires
| Framework | Scope | Key technical controls | What it doesn't cover |
|---|---|---|---|
| GDPR | Personal data of EU residents | Access controls, encryption, breach notification within 72h, data minimization | Specific security standards; implementation is left to the organization |
| NIS2 | Critical infrastructure and essential services across the EU | Risk management, incident reporting, supply chain security, MFA | Prescriptive technical implementation; focuses on outcomes |
| DORA | Financial entities operating in the EU | ICT risk management, resilience testing, third-party ICT oversight, incident classification | Non-financial sectors; narrow scope by design |
| SOC 2 | Service organizations handling customer data | Availability, confidentiality, processing integrity, access logging | Point-in-time audit; no continuous compliance guarantee |
| ISO 27001 | Any organization seeking ISMS certification | Risk assessment, asset management, access control, incident management | Operational effectiveness; certification confirms process, not outcomes |
The table reveals a pattern: every framework covers access control and incident response in some form, but none prescribes exactly how. That implementation gap is where most breaches occur — not because the framework was wrong, but because the organization stopped at the checkbox.

Passwork's audit logs, role-based access controls, and ISO 27001 certification directly support compliance with GDPR, NIS2, and SOC 2 requirements. Explore Passwork's compliance-relevant features → passwork.pro
Developing an incident response plan (assume breach)
Prevention is never absolute. The IBM Cost of a Data Breach Report 2025 found that the mean time to identify and contain a breach is 241 days. Organizations with a tested incident response plan contain breaches significantly faster — and faster containment directly reduces cost.
An effective IR plan defines: who declares an incident, what the escalation path looks like, how systems are isolated, when regulators and affected parties must be notified, and how evidence is preserved for forensic analysis. GDPR Article 33 requires notification to supervisory authorities within 72 hours of becoming aware of a breach — a timeline that's impossible to meet without a pre-defined process.
Test the plan. A tabletop exercise run once a year reveals gaps that no amount of documentation can expose.
Conclusion

The threat landscape has moved decisively away from malware-based attacks toward identity exploitation, fileless techniques, and supply chain compromise. A signature-based antivirus product addresses none of these vectors effectively.
The 7-layer model above — anchored by phishing-resistant MFA, enterprise password management, and Zero Trust architecture — reflects how modern attacks actually work and where controls have the highest impact. Each layer addresses a specific stage of the attack chain. Together, they create defense in depth that legacy perimeter security cannot replicate.
Audit your current stack against these seven layers. Identify which controls are absent, which are partially implemented, and which are misconfigured. The gaps you find are the gaps an attacker will find first.

Passwork is available as a self-hosted and cloud solution with AES-256 encryption, AD/LDAP integration, full audit logging, and ISO 27001 certification. Try Passwork in your environment → passwork.pro
Frequently asked questions

What should businesses look for in an enterprise password manager?
Prioritize on-premise or self-hosted deployment so credential data stays within your infrastructure. Essential capabilities include zero-knowledge AES-256 encryption, Active Directory and LDAP integration for automated user provisioning, tamper-evident audit logs, and ISO 27001 certification. Passwork meets all of these requirements and deploys entirely within your own environment.
What is the most common cause of a data breach in 2026?
Stolen credentials remain the leading initial access vector. Verizon's 2025 DBIR found that compromised credentials were involved in roughly 30% of breaches. Attackers obtain them through phishing, leaked databases, or compromised vendors — then authenticate as legitimate users, bypassing signature-based defenses entirely.
Why is antivirus no longer sufficient for data breach prevention?
Antivirus relies on signature-based detection: it identifies threats by matching files against a database of known malware. According to CrowdStrike's 2026 Global Threat Report, 82% of detections in 2025 were malware-free — meaning attackers used credential abuse and fileless techniques that leave no binary footprint for antivirus to scan.
What is the difference between a security incident and a data breach?
A security incident is any event that threatens confidentiality, integrity, or availability — most never escalate further. A confirmed data breach means unauthorized access to data is established as fact. That distinction determines your legal exposure: GDPR Article 33 and NIS2 Article 23 require notification to supervisory authorities within 72 hours of confirming a breach.
What does Zero Trust architecture actually mean in practice?
Zero Trust means no user, device, or network segment is trusted by default — regardless of whether the request originates inside or outside the corporate perimeter. Every access request is verified against identity, device health, and behavioral context. Micro-segmentation limits lateral movement if one account or endpoint is compromised. NIST SP 800-207 provides the authoritative implementation framework.
What is a supply chain attack and how does it differ from a standard vendor breach?
A supply chain attack injects malicious code into software before it reaches the end user — through a compromised build pipeline, a tampered package repository, or a hijacked update. Unlike a vendor breach, where attacker access is the threat, a supply chain attack weaponizes the software itself. By the time the payload arrives, it already appears legitimate.
What is the mean time to detect and contain a data breach?
According to IBM's Cost of a Data Breach Report 2025, the mean time to identify and contain a breach is 241 days. Organizations with a tested incident response plan contain breaches significantly faster. That speed difference directly reduces financial and regulatory exposure — including the 72-hour notification window required under GDPR Article 33.
What should an enterprise password manager include to support compliance?
On-premise deployment so credential data stays within your infrastructure, AES-256 zero-knowledge encryption, Active Directory and LDAP integration for automated provisioning and deprovisioning, tamper-evident audit logs, and ISO 27001 certification. These capabilities directly address access control and audit requirements under GDPR, NIS2, and SOC 2. Passwork meets all of these requirements and deploys entirely within your own environment.
How does Privileged Access Management reduce breach risk?
PAM controls access to high-value accounts — domain controllers, cloud consoles, database servers — and enforces Just-In-Time provisioning: admin rights are granted for a defined window and automatically revoked. This eliminates standing privileges that attackers exploit after initial compromise. The principle of least privilege limits the blast radius of any single compromised account.



Table of contents
- Introduction
- Key takeaways
- What is a data breach? (The modern definition)
- Why antivirus is no longer enough for data breach prevention
- The 7-layer data breach prevention strategy for 2026
- How compliance frameworks impact data breach prevention
- Developing an incident response plan (assume breach)
- Conclusion
- Frequently asked questions
Table of contents
- Introduction
- Key takeaways
- What is a data breach? (The modern definition)
- Why antivirus is no longer enough for data breach prevention
- The 7-layer data breach prevention strategy for 2026
- How compliance frameworks impact data breach prevention
- Developing an incident response plan (assume breach)
- Conclusion
- Frequently asked questions
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more



