
Introduction
Data residency and data sovereignty sound almost like the same thing. But they aren't.
Many European organizations choose a US-based vendor, select the EU data center option, and consider the data residency question resolved. Legally, it isn't. The US CLOUD Act gives American federal authorities the power to compel any US-incorporated company to produce data stored anywhere in the world. The data is in Europe. The legal obligation is not.
This is the tension European businesses run into when choosing how to host a password manager. GDPR, NIS2, DORA, and the CLOUD Act create overlapping requirements that don't resolve by picking the nearest data center. The hosting model (who owns the infrastructure, under which jurisdiction, with what level of organizational control) is what actually determines the compliance picture.
This guide maps the hosting models available to European organizations, the regulatory framework that shapes each one, and the criteria that should drive the decision.
Key takeaways
- Choosing an EU data center does not resolve data sovereignty. If the vendor is US-incorporated, the CLOUD Act compels them to produce data for American authorities — regardless of where the servers physically sit.
- Four regulatory frameworks shape the hosting decision. GDPR, NIS2, DORA, and the US CLOUD Act create overlapping obligations that no data center selection alone can satisfy. The hosting model is what determines legal defensibility.
- On-premises is the only model that eliminates third-party access by design. It removes CLOUD Act exposure entirely and gives the organization full infrastructure control, but requires internal IT capacity to operate and maintain.
- Sovereign EU cloud is a credible middle ground. European spending on sovereign cloud IaaS is projected to reach $12.6 billion in 2026 — an 83% increase year-over-year (Gartner, 2026). The model delivers managed infrastructure without foreign jurisdiction risk.
- The right model depends on four variables. Sector classification, regulatory exposure, internal IT capacity, and total cost of ownership determine whether on-premises, sovereign EU cloud, or hybrid architecture is the defensible choice.
The European hosting spectrum
European organizations have five distinct hosting configurations available for a password manager. Two fall outside realistic compliance consideration for most EU businesses. Three are worth evaluating in depth.
US cloud with US data center sits outside the scope of this guide and, for most European organizations, outside the scope of realistic consideration. When servers are located in the United States and the parent company is US-incorporated, data physically resides outside the EU. That combination triggers GDPR transfer obligations under Articles 44–49 and creates full CLOUD Act exposure simultaneously.
US cloud with EU data center is a step closer to compliance — but not a clean solution. The password manager vendor operates servers in an EU region (e.g., Frankfurt, Dublin), so data physically resides in Europe. That satisfies GDPR data residency requirements on paper. However, when the parent company is US-incorporated, the US CLOUD Act applies regardless of where the servers sit. American authorities can legally compel access to that data without invoking EU legal channels. The risk is lower than the previous model, but sovereignty is not guaranteed
The three models worth evaluating:
- Sovereign EU cloud. The service runs on infrastructure owned and operated by EU-based providers, outside US or other foreign jurisdiction. This model addresses GDPR data residency requirements and eliminates CLOUD Act exposure.
- On-premises deployment. The password manager runs entirely within the organization's own infrastructure (physical servers, private cloud, or air-gapped environments). No third-party vendor has access to credential data. This is the only model that gives complete infrastructure control.
- Hybrid architecture. A combination of on-premises vaults for sensitive credentials and cloud-based access for distributed teams. Requires careful policy design to avoid creating compliance gaps between the two environments.
The choice between these models is a regulatory and risk management question.
How EU regulations dictate password manager hosting

GDPR, NIS2, DORA, and the US CLOUD Act each impose specific obligations that directly constrain which hosting model a European organization can defensibly choose. Understanding the interaction between these frameworks is the starting point for any deployment decision.
GDPR and data residency
The General Data Protection Regulation is the EU's primary legal framework governing the collection, storage, and transfer of personal data. It applies to any organization processing the personal data of EU residents, regardless of where that organization is based.
GDPR does not explicitly require data to be stored within the EU. What it requires is that personal data transferred outside the EU is protected to an equivalent standard — through Standard Contractual Clauses (SCCs), adequacy decisions, or other transfer mechanisms under Articles 44–49. For a password manager storing employee credentials and associated metadata (usernames, URLs, email addresses), GDPR applies directly.
"Any transfer of personal data which are undergoing processing or are intended for processing after transfer to a third country or to an international organisation shall take place only if, subject to the other provisions of this Regulation, the conditions laid down in this Chapter are complied with by the controller and processor." — GDPR, Article 44 (General principle for transfers)
The risk is not theoretical. In August 2024, the Dutch Data Protection Authority fined Uber €290 million for transferring the personal data of European taxi drivers to US servers without applying any of the safeguards required under GDPR Chapter V. No Standard Contractual Clauses, no adequacy decision, no alternative transfer mechanism. The violation spanned more than two years. The case directly illustrates what Article 44 enforcement looks like in practice: employee data, cross-border infrastructure, and a nine-figure penalty.
NIS2 and critical infrastructure
The NIS2 Directive (Network and Information Security Directive 2) is the EU's primary cybersecurity legislation, replacing the original NIS Directive from 2016. It establishes binding security requirements for organizations operating in critical sectors across EU member states, with a focus on risk management, incident reporting, and supply chain security.
NIS2 significantly expands the scope of organizations classified as "essential" or "important" entities. Sectors including energy, transport, banking, healthcare, digital infrastructure, and public administration must now treat their technology vendors as part of their security perimeter, not just their internal infrastructure.
A password manager storing credentials in a third-party cloud environment falls within that perimeter. It is a direct supplier of a security-critical service. NIS2 Article 21(2) requires covered entities to implement measures that include at least:
"Supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers." — NIS2 Directive, Article 21(2), Directive (EU) 2022/2555
Choosing a US-based cloud provider for credential storage without a documented risk assessment creates a concrete compliance gap. Under NIS2, national supervisory authorities can issue binding instructions and impose fines. For essential entities, Article 20 also establishes personal liability for members of the management body.
DORA and financial sector specifics
The Digital Operational Resilience Act (DORA) is the EU's regulatory framework for digital operational resilience in the financial sector. It sets requirements for how financial entities manage information and communication technology (ICT) risks, covering third-party dependencies, incident reporting, and resilience testing, to ensure the stability of financial services across the EU.
A cloud-hosted password manager qualifies as an ICT third-party service under DORA. That classification triggers specific contractual obligations — including a requirement to document where data is stored and processed. Article 30(2)(b) of Regulation (EU) 2022/2554 states:
"The locations, namely the regions or countries, where the contracted or subcontracted functions and ICT services are to be provided and where data is to be processed, including the storage location, and the requirement for the ICT third-party service provider to notify the financial entity in advance if it envisages changing such locations" — DORA, Article 30(2)(b), Regulation (EU) 2022/2554
If the password manager provider is US-based, the financial institution must document how it manages CLOUD Act exposure and ensure the contract meets DORA's requirements for data access, portability, and termination.
The US CLOUD Act
The Clarifying Lawful Overseas Use of Data Act (CLOUD Act, 2018) is a US federal law that allows law enforcement agencies to compel US-incorporated companies to produce data stored anywhere in the world, including servers located in EU data centers. The obligation applies regardless of where the data physically resides. The determining factor is the corporate jurisdiction of the provider.
The statute is unambiguous on this point:
"A provider of electronic communication service or remote computing service shall comply with the obligations of this chapter to preserve, backup, or disclose the contents of a wire or electronic communication and any record or other information pertaining to a customer or subscriber within such provider's possession, custody, or control, regardless of whether such communication, record, or other information is located within or outside of the United States." — 18 U.S.C. § 2713, Pub. L. 115–141, div. V, §103(a)(1), March 23, 2018
The company can challenge the order, but the legal obligation exists regardless of where the servers are located.
For European organizations handling sensitive credentials (privileged access, financial system passwords, infrastructure keys) this creates a structural risk that EU-region data centers alone do not resolve. Sovereign cloud or on-premises deployment are the only models that eliminate this exposure entirely.

Passwork is a European password manager built for exactly this regulatory environment with both on-premises and cloud options designed around GDPR and NIS2 compliance and data sovereignty. See how it works
Cloud password managers in Europe: Convenience vs control

Cloud hosting means the vendor's servers store and process your data — the organization accesses the service over the internet without managing any underlying infrastructure. For password managers, this means credentials, metadata, and access logs reside on servers owned and operated by a third party, in data centers the organization does not control.
Cloud-hosted password managers offer fast deployment, automatic updates, and no infrastructure overhead. For many European organizations, they are the default choice — 53% of EU enterprises used paid cloud computing services in 2025, up 7.4 percentage points from 2023 (Eurostat, 2026).
The appeal is straightforward: no servers to maintain, the vendor handles patching, and access works from any device. For SMBs without dedicated security teams, this lowers the barrier to deploying proper credential management.
Where cloud falls short for EU organizations
The shared responsibility model is the central issue. In a cloud deployment, the vendor controls the infrastructure, the encryption key management architecture, and the backup systems. The organization controls user access and policies but not the underlying data environment.
Zero-knowledge architecture partially addresses this: if the vendor never holds the decryption keys, a server-side breach cannot expose plaintext credentials. The ICO fine against LastPass illustrates the limits — the breach exposed metadata (names, emails, URLs) even though encrypted vault contents were protected. Metadata is personal data under GDPR.
AES-256 encryption at rest is a baseline requirement, not a differentiator. What matters is where keys are generated, stored, and who can access them and whether the vendor's architecture keeps those keys outside their own reach.
On-premises password managers: Maximum sovereignty

On-premises deployment means the password manager runs on servers the organization owns and operates — no vendor has network access to the credential store. All credentials, metadata, and access logs remain within the organization's own infrastructure perimeter.
This is the only hosting model that fully satisfies data sovereignty requirements and eliminates third-party exposure by design.
For organizations in regulated sectors (financial institutions, healthcare providers, critical infrastructure operators under NIS2) on-premises deployment removes an entire category of third-party risk from the compliance equation.
Where on-premises is the only viable option
Air-gapped environments represent the most secure variant: the password manager operates on a network with no internet connectivity. This is relevant for industrial control systems, classified environments, or any context where the credential store must be physically isolated from external networks.
As covered above, on-premises deployment with a non-US vendor is the only model that eliminates CLOUD Act exposure entirely by removing the US corporate jurisdiction that triggers the obligation in the first place.
On-premises deployment: Pros and cons
| Factor | Advantage | Limitation |
|---|---|---|
| Data sovereignty | Complete — no third-party access | Requires internal policy enforcement |
| Regulatory compliance | Eliminates CLOUD Act exposure; simplifies GDPR, NIS2, DORA audits | Compliance documentation still required |
| Security control | Full control over encryption, key management, access | Organization bears full responsibility for security hardening |
| Infrastructure | Runs in existing environment, including air-gapped networks | Requires server capacity and maintenance |
| Updates | Organization controls update schedule | Patching is an internal responsibility |
| Cost | No per-user SaaS fees at scale | Higher upfront setup cost; ongoing IT overhead |
| Availability | Dependent on internal infrastructure reliability | No vendor SLA for uptime |
| Deployment speed | Predictable, controlled rollout | Slower initial setup than cloud |
The TCO calculation shifts costs from recurring SaaS fees to internal IT labor and infrastructure. For organizations that already operate their own servers and have a security team in place, the marginal cost of adding a self-hosted password manager is often lower than it appears.
The real cost of on-premises is the operational discipline required to maintain it. Businesses that lack a dedicated security team or a mature patch management process will find the limitations column harder to manage than the advantages column suggests.
Passwork is available as a fully self-hosted solution: deployed on the organization's own servers, with no outbound connections. The source code is available for audit, and the platform supports air-gapped environments. For teams that need to demonstrate full data sovereignty to auditors or regulators, this is the deployment model that closes the argument.

Passwork on-premises gives your team full infrastructure control — no third-party access, no exceptions. Explore on-premises deployment
The sovereign cloud middle ground
Sovereign EU cloud providers offer a third path: managed infrastructure with cloud-style convenience, operated entirely within EU jurisdiction and outside the reach of foreign legal frameworks. European spending on sovereign cloud IaaS is projected to reach $12.6 billion in 2026, an 83% increase from 2025 (Gartner, 2026).
The growth is driven by geopolitical pressure. The US CLOUD Act, combined with high-profile incidents involving hyperscaler dependency, has pushed European organizations to reconsider their cloud vendor choices.
For a password manager deployed on sovereign cloud infrastructure, the hosting environment provides documented evidence that data stays within EU jurisdiction — directly relevant for NIS2 compliance documentation and DORA third-party risk assessments.
Sovereign cloud addresses jurisdiction and infrastructure control. It does not replace the need to evaluate the password manager application itself. The hosting layer and the application layer are separate security questions.
Hybrid architecture
A hybrid architecture combines on-premises vaults for sensitive credentials with cloud-based access for distributed teams. It is a policy and engineering decision that requires explicit boundaries between what stays local and what moves through external infrastructure.
The appeal is practical. Organizations with remote or internationally distributed teams cannot always route every authentication request through an on-premises system without introducing latency or availability risks. A hybrid setup lets security teams keep the most sensitive credential classes (privileged accounts, infrastructure secrets, compliance-sensitive credentials) in a locally controlled vault, while extending access to less sensitive resources through a cloud layer.
The compliance complexity, however, scales with the architecture. Every boundary between the on-premises and cloud components is a potential gap: in audit coverage, in access policy enforcement, in incident response scope. If the cloud layer falls under a foreign jurisdiction, the sovereignty protections of the on-premises component do not automatically extend to it.
Hybrid architecture is the most flexible model in this spectrum — and the most demanding to operate correctly. For organizations with the engineering capacity to manage it, it offers a workable balance between control and accessibility. For those without, on-premises or sovereign EU cloud is the more defensible choice.
Passwork for European businesses: Built for sovereignty from the start
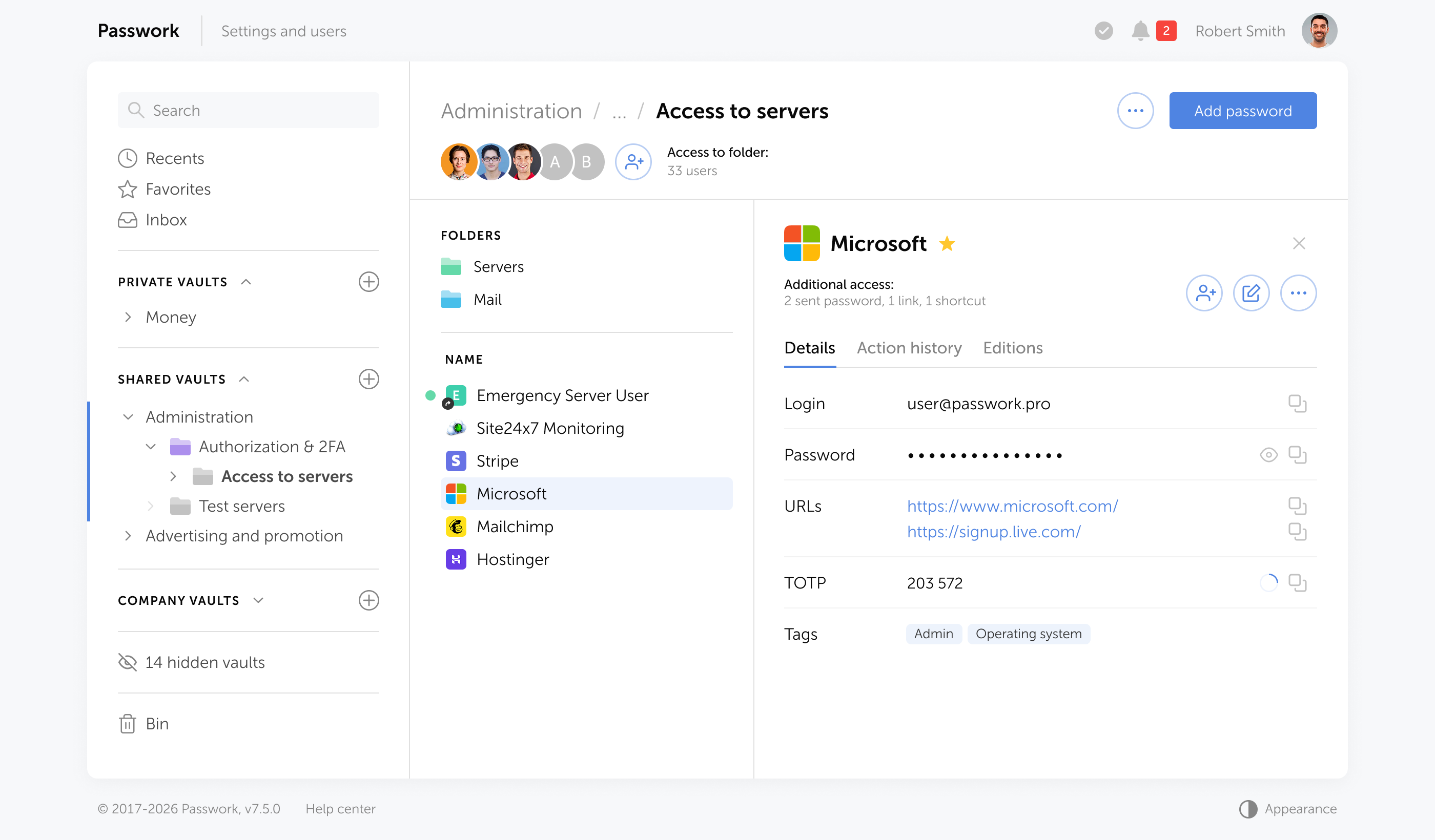
Passwork is a European password manager — incorporated and operated as a European company, with its legal base in Spain under EU law. It was built on-premises first, for organizations that need full infrastructure control, and has since added a cloud option hosted entirely within the EU.
This matters for European businesses because the vendor's own jurisdiction is part of the compliance picture. A European company operating under EU law does not carry US CLOUD Act exposure. Passwork's architecture and deployment options were designed with this regulatory context in mind.
On-premises deployment
Passwork on-premises runs entirely within the organization's own infrastructure. The vendor has no access to the credential store — no remote access, no telemetry, and no backdoor. All data, encryption keys, and backups remain inside the organization's systems.
Key capabilities for regulated environments:
- Full infrastructure control — deploy on your own servers, private cloud, or air-gapped networks. Supports environments with no internet connectivity.
- Zero-knowledge architecture — credentials are encrypted and decrypted on the client side. The server stores only ciphertext and never processes plaintext passwords, which means a compromised server exposes nothing readable.
- Role-based access control — granular permissions at vault, folder, and credential level. Integrates with Active Directory, Azure AD, LDAP, and SAML SSO for automated user provisioning and lifecycle management.
- Audit logs — complete activity history for every credential access, modification, and sharing event. Directly supports GDPR accountability requirements and NIS2 incident documentation.
- AES-256 encryption — credentials encrypted at rest and in transit. Keys stay within the organization's infrastructure.
- Compliance reports — built-in reporting for security audits, access reviews, and regulatory documentation.
- Scales from 10 to 30,000+ users — the same architecture works for a mid-market IT team and a large enterprise with complex permission structures.
The majority of Passwork's customers choose on-premises deployment, according to the company's internal data. This is especially true for large enterprises, government bodies, and organizations in highly regulated industries.
Passwork Cloud: EU-hosted, zero-knowledge
Passwork Cloud is hosted in Germany. All data stays within EU jurisdiction, processed and stored under EU law.
The architecture uses client-side encryption with zero-knowledge design: the server never sees plaintext credentials. Encryption and decryption happen on the client side, so even in the event of a server-side incident, credential data remains protected.
Passwork Cloud includes the full enterprise feature set:
- User management, Active Directory / LDAP integration, SSO
- Audit logs and compliance reports
- Advanced MFA and security policies
- Browser extensions, mobile apps, and REST API
- DevOps secrets management — CLI, Python library, Kubernetes integration, CI/CD pipeline support
Pricing starts at €3 per user per month (Standard) and €4.50 per user per month (Advanced). Long-term ownership costs run approximately 30% below the industry average.
Security posture
Passwork holds ISO 27001 certification across development, infrastructure, and operations. The company runs annual third-party penetration tests, including through HackerOne, and applies a DevSecOps approach with static and dynamic analysis integrated into every build.
This security posture is directly relevant for organizations that need to document their password manager vendor's security practices — a requirement under both NIS2 Article 21 and DORA's third-party risk management framework.
Decision framework: Choosing the right model for your organization
The right hosting model depends on four variables: regulatory exposure, sector classification, internal IT capacity, and total cost of ownership. The table below maps common organizational profiles to recommended deployment models.
| Organization profile | Recommended model | Key driver |
|---|---|---|
| SMB, no regulated sector, limited IT team | Sovereign EU cloud | Low overhead; EU jurisdiction without infrastructure investment |
| Mid-market, general enterprise | Sovereign EU cloud or hybrid | GDPR compliance without full infrastructure investment |
| Financial institution (DORA-regulated) | On-premises or sovereign EU cloud | DORA third-party risk requirements; need for audit and exit rights |
| Critical infrastructure (NIS2 essential entity) | On-premises or sovereign EU cloud | NIS2 supply chain security; documented ICT dependency management |
| Healthcare, public sector | On-premises or sovereign EU cloud | Sensitive data categories; national data localization requirements |
| Defense, classified environments | On-premises, air-gapped | Absolute isolation requirement; no external network connectivity |
| Multinational with distributed teams | Hybrid architecture | Balance between central control and remote access needs |
TCO considerations
Total cost of ownership for each model includes more than licensing or infrastructure costs. Compliance overhead is a real line item: the time spent on vendor risk assessments, audit documentation, and incident response planning varies significantly by model.
On-premises deployment concentrates compliance work internally — the organization controls the environment and can produce audit evidence directly. Cloud deployments shift some compliance work to vendor management: reviewing security certifications, negotiating DPA terms, maintaining a DORA third-party register entry.
For NIS2-regulated entities, the compliance overhead of a poorly documented cloud deployment can exceed the infrastructure cost of on-premises deployment. That calculation is worth running before defaulting to the lowest-friction option.
Conclusion

The hosting model for a password manager is an architectural decision with long-term compliance implications. GDPR, NIS2, DORA, and the US CLOUD Act create a regulatory environment where the wrong choice generates documented liability.
The model spectrum gives European organizations real options. The right choice depends on sector classification, regulatory exposure, internal IT capacity, and an honest TCO calculation that includes compliance overhead.
For organizations that need maximum control, on-premises deployment eliminates third-party exposure entirely. For those that need managed infrastructure without foreign jurisdiction risk, sovereign EU cloud is a credible path. Hybrid architectures work when neither extreme fits the operational reality.
Passwork is a European password manager that covers the full spectrum: on-premises deployment for organizations that require complete infrastructure control, and EU-hosted cloud for teams that want managed hosting without sacrificing data sovereignty. Both options are built on the same zero-knowledge encryption architecture and include the audit, access control, and compliance reporting features that regulated European businesses need.

Ready to take te frist step? Start your free Passwork trial to get complete control, automated credential management, and enterprise-grade data protection.
Frequently asked questions

Is a cloud password manager GDPR compliant?
A cloud password manager can be GDPR compliant if the vendor processes personal data under a valid legal basis, provides a Data Processing Agreement (DPA) meeting Article 28 requirements, and applies appropriate safeguards for any data transfers outside the EU. Compliance depends on the vendor's architecture and contractual terms — not cloud hosting alone.
Does GDPR require data to be stored in Europe?
GDPR does not mandate EU data storage. It requires that personal data transferred outside the EU is protected to an equivalent standard — through adequacy decisions, Standard Contractual Clauses, or other mechanisms under Articles 44–49. Storing data in the EU simplifies compliance but is not a legal requirement under the regulation itself.
What is the US CLOUD Act and why does it matter for EU businesses?
The US CLOUD Act (2018) allows US federal authorities to compel US-incorporated companies to produce data stored anywhere in the world, including EU data centers. For European organizations using US-based password manager vendors, this means credential data could be subject to US government access regardless of where the servers are physically located.
When does NIS2 apply to password manager hosting decisions?
NIS2 applies when the organization is classified as an "essential" or "important" entity — covering energy, transport, banking, healthcare, digital infrastructure, and public administration, among others. For these organizations, a password manager is part of the ICT supply chain, and Article 21 requires documented security measures for all supply chain components.
What does DORA require for cloud-hosted password managers in financial services?
DORA requires financial entities to maintain a register of ICT third-party service providers, conduct risk assessments of critical providers, and ensure contracts include rights to audit, data access, and exit. A cloud-hosted password manager used by a financial institution is an ICT third-party service under DORA — the institution must document and manage this dependency formally.
What is the difference between a sovereign EU cloud and a regular EU data center?
A regular EU data center operated by a US company is still subject to US jurisdiction through the CLOUD Act. A sovereign cloud provider is incorporated and operated entirely within the EU, with no legal obligation to comply with foreign government data requests. The distinction matters for GDPR transfer risk assessments and NIS2 supply chain documentation.
How does Passwork support compliance for European organizations?
Passwork is a European company under EU law, ISO 27001 certified, with on-premises and EU-hosted cloud deployment options. On-premises deployment eliminates third-party access entirely. The cloud version is hosted in Germany under EU jurisdiction with zero-knowledge encryption. Both options include audit logs, compliance reports, and role-based access control to support GDPR, NIS2, and DORA requirements.

Table of contents
- Introduction
- Key takeaways
- The European hosting spectrum
- How EU regulations dictate password manager hosting
- Cloud password managers in Europe: Convenience vs control
- On-premises password managers: Maximum sovereignty
- The sovereign cloud middle ground
- Hybrid architecture
- Passwork for European businesses: Built for sovereignty from the start
- Decision framework: Choosing the right model for your organization
- Conclusion
- Frequently asked questions
Table of contents
- Introduction
- Key takeaways
- The European hosting spectrum
- How EU regulations dictate password manager hosting
- Cloud password managers in Europe: Convenience vs control
- On-premises password managers: Maximum sovereignty
- The sovereign cloud middle ground
- Hybrid architecture
- Passwork for European businesses: Built for sovereignty from the start
- Decision framework: Choosing the right model for your organization
- Conclusion
- Frequently asked questions
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more



