
The IBM Cost of a Data Breach Report 2025 places the global average cost of a data breach at $4.4 million — a 9% decrease from the previous year but still a significant financial risk for organizations. Firewalls get patched. Systems get updated. But the person who picks up the phone, clicks a link, or holds the door open for a stranger — that attack surface doesn't shrink on its own.
Two terms dominate every cybersecurity conversation about human-targeted attacks: social engineering and phishing. They're often used interchangeably, which creates a dangerous blind spot. Understanding the distinction — and the relationship between them — is the first step toward building defenses that actually hold.
Social engineering is the overarching psychological manipulation strategy. Phishing is its most common digital delivery method. One is the playbook; the other is a specific play.
Main points:
- Social engineering exploits cognitive shortcuts to bypass security controls without touching a single line of code.
- Phishing is the most scalable form of social engineering: digital, repeatable, and increasingly automated. Its primary goal is credential theft, but it also delivers malware, ransomware, and fraudulent financial transfers.
- The two are not interchangeable. Every phishing attack is social engineering — but most social engineering attacks are not phishing. Defenses built only around email filters leave phone lines, physical access points, and in-person manipulation entirely unaddressed.
- Credential controls limit the blast radius. When manipulation succeeds role-based access, unique passwords per system, and full audit visibility determine how far an attacker can move. Tools like Passwork enforce these practices at the infrastructure level.
What is social engineering?
Social engineering is the practice of exploiting human psychology — rather than technical vulnerabilities — to gain unauthorized access to systems, data, or physical spaces. An attacker doesn't need to crack a password if they can convince someone to hand it over.

The discipline predates computers. Con artists, spies, and fraudsters have always relied on the same cognitive shortcuts that make humans predictable. What's changed is the scale and precision with which these techniques can now be deployed.
The psychological triggers that make it work
Every successful social engineering attack pulls on one or more of the following levers:
- Fear — "Your account will be suspended unless you act now."
- Urgency — "The wire transfer must go out before end of business today."
- Authority — Impersonating a CEO, auditor, or IT administrator.
- Curiosity — A USB drive labeled "Q4 Salary Review" left in a parking lot.
- Greed — A too-good-to-be-true offer, prize, or opportunity.
These aren't design flaws in human cognition — they're features. Attackers simply weaponize the same mental shortcuts that help people function efficiently under pressure.
Common social engineering techniques
Social engineers rely on several proven manipulation techniques. With pretexting, they fabricate believable scenarios to extract sensitive information. Another approach, baiting, dangles something tempting — like free software — in exchange for confidential details. Then there's impersonation: attackers pose as someone the victim knows to gain access to data or systems.
These methods exploit psychological triggers such as trust, urgency, and authority. They manipulate individuals into acting without considering security risks. Trust makes us comply with perceived superiors, urgency disables critical thinking, authority exploits our instinct to obey figures of power.
These triggers exploit social phenomena like obedience to authority (Milgram experiments) and scarcity/urgency (Cialdini). They bypass rational deliberation via amygdala-driven responses. When an email screams "URGENT," fear overrides rational thought — victims act before questioning.
The Verizon 2025 DBIR states that 24% of breaches involved social engineering tactics. This demonstrates their effectiveness in exploiting human behavior relative to technical defenses. Other techniques like tailgating (gaining physical access by following someone) and quid pro quo attacks (offering something in return for information) also bypass rational thinking and security protocols, making them difficult to detect.
- Urgent requests for sensitive information
- Unusual behavior from trusted sources
- Requests bypassing normal security protocols
What is phishing?
Phishing is a specialized digital subset of social engineering. It primarily uses electronic communication to deceive individuals into revealing sensitive information, such as login credentials.
Unlike traditional social engineering attacks, which may involve in-person interactions or phone calls, phishing is predominantly conducted through malicious emails, spoofed websites, or text messages. These attacks focus on credential harvesting and attempt to steal usernames, passwords, and other important data.
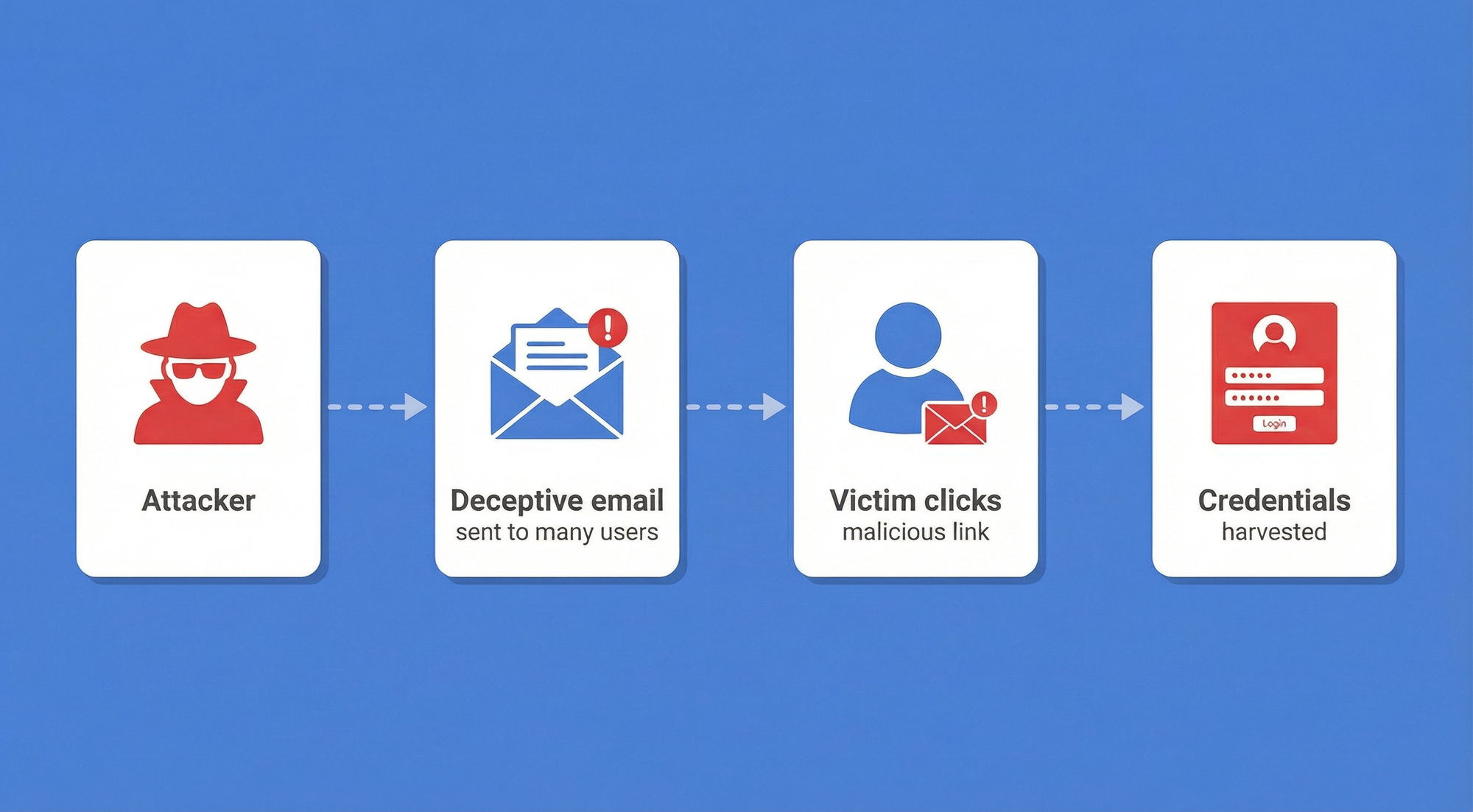
Phishing tactics rely heavily on deceptive messages. Often they are designed to look like legitimate communications from trusted sources, such as banks or IT departments. These attacks are implemented using technical methods like spoofed URLs, malicious links, and websites that mimic real ones.
Types of phishing attacks: basic, targeted, and highly sophisticated
Phishing is a specific subset of social engineering that uses deceptive digital messages — email, SMS, voice calls, or direct messages — to steal credentials, deploy malware, or manipulate targets into taking a harmful action.
If social engineering is the strategy, phishing is the most scalable tactic within it. It's digital, repeatable, and increasingly automated. IBM's 2025 Cost of a Data Breach Report identified phishing as the leading initial attack vector, responsible for 16% of breaches at an average cost of $4.4 million per incident.
The evolution of phishing attacks
- Spear phishing is targeted phishing. Instead of casting a wide net, attackers research a specific individual — their role, colleagues, recent projects — and craft a message that feels entirely legitimate. The personalization dramatically increases success rates.
- Whaling is spear phishing aimed at C-suite executives. The stakes are higher (executive credentials unlock more), and the lures are tailored to executive concerns: board communications, M&A activity, regulatory filings.
- Vishing (voice phishing) uses phone calls to manipulate targets. Detection of vishing attacks surged 442% in late 2024 and into 2025. AI voice cloning has made this category particularly dangerous — more on that below.
- Smishing (SMS phishing) exploits the higher open rates of text messages and the relative lack of security tooling on mobile devices. Fake delivery notifications, bank alerts, and two-factor authentication prompts are common lures.
The following table compares different phishing types:
| Phishing type | Characteristics | Typical targets | Difficulty to detect | Justification |
|---|---|---|---|---|
| Spear Phishing | Targeted, personalized emails | Specific individuals, businesses | High | Personalization bypasses generic filters |
| Whaling | Executive-focused, highly researched | C-suite, board members | Very High | Uses insider knowledge, targets people with override authority who face fewer checks |
| Smishing | Malicious links via SMS | Mobile users | High | No URL preview on mobile, bypasses email security stack entirely |
| Vishing | Voice calls with spoofed caller ID | Individuals, companies | High → Very High (with AI cloning) | No inspectable artifacts (no URL/domain to verify); real-time interaction pressures victim |
Common phishing tactics and red flags
AI enables personalized content generation. Attackers tailor their approaches to specific targets and fly under the radar of traditional security tools. Attackers now manipulate visuals and voices to create fraudulent communications that seem utterly legitimate — a trend the IBM Cost of Data Breach report flags as increasingly difficult to detect. For cybersecurity teams, this growing sophistication means defending against threats that look and sound real.
- Suspicious or mismatched URLs
- Unexpected urgent requests for information
- Emails from unfamiliar or incorrect domains
Social engineering vs. phishing: differences and relationship
Phishing is a specific form of social engineering focused on credential theft through deceptive digital communications. While social engineering encompasses a wide range of manipulative tactics, such as pretexting and baiting, phishing is primarily aimed at stealing login information, often via email, SMS, or voice channels.
The main difference lies in medium and focus: social engineering spans physical/digital tactics (e.g., in-person pretexting, tailgating), while phishing is digital-centric (email, SMS, voice via spoofed channels), always a subset of social engineering.
The relationship is hierarchical, not competitive. Phishing is one tool within the broader social engineering toolkit.
| Dimension | Social engineering | Phishing |
|---|---|---|
| Scope | Broad psychological manipulation strategy | Specific digital attack tactic |
| Medium | Physical, verbal, digital, or any combination | Email, SMS, voice calls, messaging platforms |
| Primary goal | Gain access, trust, information, or physical entry | Steal credentials, deploy malware, trigger financial transfers |
| Targeting | Can be highly targeted or opportunistic | Ranges from mass campaigns to surgical spear phishing |
| Technical requirement | None — can be entirely non-digital | Requires digital infrastructure |
| Examples | Pretexting, baiting, tailgating, quid pro quo | Spear phishing, whaling, vishing, smishing |
Is phishing a type of social engineering? Yes, definitively. Every phishing attack is social engineering, but most social engineering attacks are not phishing. Recognizing this hierarchy matters because defenses designed only to catch phishing emails will miss pretexting calls, baiting attempts, and physical intrusions entirely.
The 2025 threat landscape: How AI is changing the game
The advice that defined phishing awareness training for a decade — "look for bad grammar and spelling errors" — is now largely obsolete. Generative AI has eliminated the linguistic tells that once made phishing emails identifiable.
AI-generated phishing at scale
Large language models can produce grammatically flawless, contextually accurate, and deeply personalized phishing lures in seconds. What previously required a skilled attacker with language proficiency and hours of research can now be automated at industrial scale. IBM's 2025 report found that AI-generated phishing was the most common use of AI in attacks, appearing in 37% of AI-involved breaches.
The implication is direct: volume is no longer a constraint for attackers. Campaigns that once targeted thousands can now target millions with the same level of apparent personalization.
Deepfake vishing: when you can't trust the voice
In early 2024, engineering firm Arup lost $25.6 million after an employee was deceived by a deepfake video call impersonating the company's CFO and other colleagues. The attacker used AI-cloned voices and video to simulate a legitimate internal meeting. The employee transferred the funds believing they had received direct instructions from senior leadership.
This isn't an isolated incident — it's a preview of standard operating procedure. Voice cloning tools are widely available, require only a few seconds of audio to generate a convincing replica, and are increasingly indistinguishable from the real thing without technical verification.
MFA bypass: why multi-factor authentication isn't enough on its own
Multi-Factor Authentication (MFA) remains one of the most effective controls against credential theft. But social engineering has adapted.
- Prompt bombing (also called MFA fatigue) involves flooding a target with authentication push notifications until they approve one out of frustration or confusion. Attackers then use the approved session to gain access.
- Adversary-in-the-Middle (AiTM) attacks use reverse-proxy phishing kits to intercept authentication tokens in real time. The target completes a legitimate-looking login — including MFA — while the attacker captures the session token and uses it independently.
The takeaway: MFA is necessary but not sufficient. The type of MFA matters, and so does training employees to recognize manipulation attempts that target the authentication process itself.
How to defend against social engineering and phishing
Effective defense operates on two tracks simultaneously: human behavior and technical controls. Neither works without the other.
Human-centric defenses
This four-step framework gives employees a concrete mental model for handling suspicious situations:
- Feel — Notice the emotional trigger. Am I feeling rushed, scared, curious, or flattered? That sensation is the signal.
- Slow — Deliberately pause before acting. Urgency is a manipulation tool; legitimate requests can wait 60 seconds.
- Verify — Confirm the request through an independent channel. Don't reply to the suspicious email — call the sender on a known number.
- Act — Only proceed once the request is verified. If verification isn't possible, escalate to security.

The median time for a user to fall for a phishing email is under 60 seconds. This framework is designed to interrupt that reflex before it completes.
Out-of-band verification
Any request involving financial transfers, credential changes, or sensitive data access should require verification through a secondary, independent channel. If a "CFO" emails requesting a wire transfer, call the CFO directly using a phone number from the company directory — not one provided in the email. This single control would have prevented the Arup deepfake attack.
Continuous simulation over annual training
Annual security awareness training is insufficient. Attackers don't operate on an annual schedule. Regular, realistic phishing simulations — varied in format, lure type, and delivery channel — build the pattern recognition that one-time training cannot. The goal is reflex, not recall.
A no-blame reporting culture is equally important. Employees who fear punishment for clicking a link will hide incidents rather than report them, eliminating the early warning signal that security teams depend on.
Technical controls
Phishing-resistant MFA
Replace SMS-based and push-notification MFA with FIDO2/WebAuthn hardware security keys or passkeys. These are cryptographically bound to the legitimate domain, making them immune to AiTM attacks and prompt bombing by design. CISA explicitly recommends phishing-resistant MFA as the standard for high-value accounts.
Email and web security
Implement DMARC, DKIM, and SPF across all sending domains to prevent domain spoofing. Layer in advanced email filtering with link scanning, attachment sandboxing, and AI-based anomaly detection. These controls won't catch everything, but they significantly raise the cost of a successful campaign.
Zero Trust architecture
Zero Trust Network Access (ZTNA) operates on the principle of "never trust, always verify." Even if an attacker successfully compromises one employee's credentials, least-privilege access controls limit what they can reach. Segmentation contains the blast radius. This is the architectural response to the reality that some attacks will succeed.
Credential hygiene is foundational to any Zero Trust implementation — and it's one of the most overlooked gaps in social engineering defense. When employees reuse passwords across systems or store them in spreadsheets and chat logs, a single successful phishing attempt can cascade into a full breach.
Passwork addresses this directly. As a business password manager built for enterprise environments, it enforces role-based access controls, maintains a full audit log of who accessed which credentials and when, and eliminates the informal credential-sharing practices that attackers exploit. If a phishing attack does succeed and an employee's account is compromised, Passwork's access controls limit lateral movement — the attacker reaches only what that role legitimately touches, nothing more.
Conclusion

The gap between social engineering and phishing isn't semantic — it's strategic. Organizations that treat phishing as the whole problem will build email filters while leaving their phone lines, physical access points, and human psychology undefended.
Social engineering vs. phishing attacks requires a response that matches the full scope of the threat: technical controls that reduce the attack surface, and a security culture that turns employees from the most exploited vulnerability into an active layer of defense.
The 60% of breaches that involve the human element won't be solved by technology alone. They'll be solved by organizations that invest equally in systems and in the people who operate them — and who build the kind of trust where an employee feels safe saying, "Something about this request felt wrong, so I stopped and asked."
That instinct is the human firewall. It's worth building deliberately. And the technical foundation underneath it — controlled access, unique credentials, full audit visibility — is exactly what a tool like Passwork is designed to provide.
Frequently Asked Questions

Is phishing a type of social engineering?
Yes. Phishing is a specific tactic within the broader category of social engineering. All phishing attacks use psychological manipulation — the defining characteristic of social engineering — but delivered through digital channels. Social engineering also includes non-digital techniques like pretexting calls, physical tailgating, and in-person impersonation.
What is the difference between phishing and spear phishing?
Standard phishing is a mass-distribution attack: the same deceptive message sent to thousands of targets in the hope that some percentage will respond. Spear phishing is targeted — the attacker researches a specific individual or organization and crafts a message tailored to that person's role, relationships, and context. Spear phishing has a significantly higher success rate and is the technique of choice for high-value targets.
How do attackers bypass MFA using social engineering?
Two primary methods: prompt bombing (flooding the target with MFA push notifications until they approve one out of fatigue) and Adversary-in-the-Middle (AiTM) attacks (using reverse-proxy phishing kits to capture session tokens in real time as the target completes a legitimate-seeming login). Both methods exploit the human layer of the authentication process rather than the cryptographic layer. The defense is phishing-resistant MFA (FIDO2/WebAuthn), which is cryptographically bound to the legitimate domain and cannot be intercepted by AiTM proxies.
What are the most common social engineering techniques in 2026?
The most prevalent techniques include AI-generated spear phishing (personalized lures created at scale using large language models), deepfake vishing (AI-cloned voice calls impersonating executives or IT staff), Business Email Compromise (pretexting via email to authorize fraudulent transfers), and prompt bombing to defeat MFA. Physical techniques like tailgating remain relevant in environments with inadequate access controls.
How can organizations measure their exposure to social engineering?
Regular phishing simulations provide a quantifiable click rate and credential submission rate across the organization. Red team exercises that include physical and voice-based social engineering scenarios reveal gaps that email-only testing misses. Tracking incident reports — including near-misses — over time shows whether the security culture is improving. The metric that matters most isn't how many employees failed a simulation; it's how many reported it.
What role does credential management play in limiting social engineering damage?
Even when an attacker successfully manipulates an employee into revealing credentials, strong credential hygiene limits the damage. Unique passwords per system mean a single compromised credential doesn't cascade. Role-based access controls mean a compromised account can only reach what that role legitimately needs. Audit logs mean the intrusion is detectable. A password manager enforces these practices systematically rather than relying on individual discipline.


Table of contents
Table of contents
A self-hosted password manager for your business
Passwork provides an advantage of effective teamwork with corporate passwords in a totally safe environment
Learn more



