Energy. Transport. Health. Digital infrastructure. You are in scope.
organizations across the EU now subject to NIS2
EU member states have transposed NIS2 into national law
organizations across the EU now subject to NIS2
EU member states have transposed NIS2 into national law
Leaders are personally liable under NIS2. Insurance may not cover it. Documented access control is your first line of defense.
Maximum fine under NIS2
88% of web app attacks start with stolen credentials. NIS2 Art. 21 requires organizations to control and monitor access to credentials
breaches involve stolen credentials
The guide hands your team the controls, evidence, and 5-phase deployment plan to achieve full NIS2 compliance

Download, configure, import, go live. Passwork runs on PHP and MongoDB with installation via Docker, Windows Server, or Linux. No third-party dependencies. No vendor access required. Your team controls every server from day one.

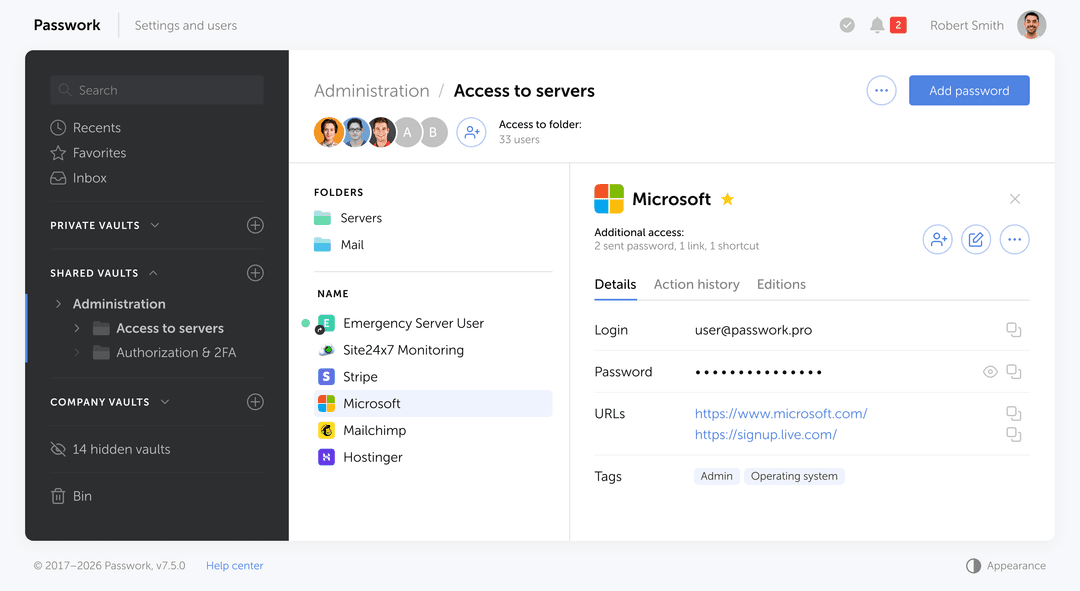
Custom user roles, TOTP, hardware-key MFA, and granular permission matrices — built to meet NIS2 Art. 21. Passwork integrates with Active Directory, Azure AD, LDAP, and SAML SSO, mapping your existing identity structure to credential access automatically. Every action is recorded. Auditors see exactly who did what.

NIS2 Article 21 requires access control. GDPR requires data protection and audit logs. Passwork covers both in one deployment with full REST API for automation via Python, CLI, and Docker.
I can't afford to fail an audit because of missing logs
Passwork logs are forensically sound and exported in formats regulators expect. Your audit preparation time drops from weeks to days.
I need to deploy fast without disrupting production
Install via Docker, Windows Server, or Linux. LDAP group mapping auto-syncs your Active Directory structure. No vendor engagement needed — your team controls the rollout.
I need to remove personal liability from my shoulders now
Documented, auditable password controls shift risk from you to proven technical infrastructure. Regulators see compliance. Lawyers see evidence.
I need confidence that passwords never leave our servers
Data is encrypted client-side with AES-256 before it ever leaves your environment. Zero-knowledge architecture guarantees no external access to your credentials. Self-hosted, EU-compliant, and ISO 27001:2022 certified.
I need one tool I can confidently recommend across all my NIS2 clients
Passwork works for companies of all sizes in your portfolio. One solution. Consistent training. Lower support burden.
Get secrets for deployment without storing them in CI/CD system environment variables. The CLI passwork automatically substitutes the actual secrets at runtime.
All DevOps features →Get secrets programmatically in your Python apps. Library handles auth, encryption and token caching.
All DevOps features →Use Passwork CLI image to deliver secrets into containers. Secrets are never stored in images or logs.
All DevOps features →Create Kubernetes secrets from Passwork automatically and integrate with GitOps workflows.
All DevOps features → pipelines: default: - step: name: Deploy with Passwork credentials image: passwork/passwork-cli:latest script: - passwork-cli exec --password-id 'deploy_credentials' -- ./deploy.sh environment: - PASSWORK_HOST=https://your-passwork.domain - PASSWORK_TOKEN=$PASSWORK_TOKEN - PASSWORK_MASTER_KEY=$PASSWORK_MASTER_KEY from passwork_client import PassworkClient # Client initialization passwork = PassworkClient("https://your-passwork.domain") passwork.set_tokens("your_access_token", "your_refresh_token") passwork.set_master_key("your_master_key") # Getting secrets database_item = passwork.get_item(item_id=PASSWORD_ID) database_password = database_item['password'] # Using in application db_connection = connect_to_database( host="prod-db.company.com", password=database_password ) # Running container with access to secrets docker run --rm \ -e PASSWORK_HOST=https://your-passwork.domain \ -e PASSWORK_TOKEN=your_access_token \ -e PASSWORK_MASTER_KEY=your_master_key \ passwork/passwork-cli:latest \ exec --folder-id FOLDER_ID --tags "production" -- python app.py # Or in docker-compose services: app: image: passwork/passwork-cli:latest command: exec --folder-id ${FOLDER_ID} --tags "production" -- ./start-app.sh environment: - PASSWORK_HOST=https://your-passwork.domain - PASSWORK_TOKEN=${PASSWORK_TOKEN} - PASSWORK_MASTER_KEY=${PASSWORK_MASTER_KEY} # Via YAML manifest passwork-cli exec --folder-id FOLDER_ID --tags "production" -- sh -c " cat <<EOF | kubectl apply -f - apiVersion: v1 kind: Secret metadata: name: app-production-config namespace: production type: Opaque stringData: database-url: \"postgresql://\$DB_USERNAME:\$DB_PASSWORD@\$DB_HOST:5432/app\" redis-url: \"redis://:\$REDIS_PASSWORD@redis:6379\" api-key: \"\$API_KEY\" webhook-secret: \"\$WEBHOOK_SECRET\" EOF" Every encryption operation happens on your device. Passwork never sees your data in plaintext.
All encryption runs client-side. Passwork servers store only encrypted data and cannot access your credentials.
Credentials encrypted with AES-256 before leaving your browser. Industry-standard key derivation protects the master key.
TOTP authenticator apps, dedicated Passwork 2FA, and hardware security keys. Enforce MFA organization-wide.
Run Passwork on your own EU-based servers for total data sovereignty. No data ever leaves your infrastructure.
Source code available for independent review. External researchers regularly evaluate the platform.
Every action logged: who accessed which credential, when, and from where. Export for compliance audits.
A partnership‑first approach: no pressure, no hassle — just genuine support, and a team that treats you like a true partner, from your first demo to long‑term success.
Passwork recognized for its unified password and secrets management, business-first design, and focus on data sovereignty.
OWASP training and threat modeling in every development team
Static & dynamic analysis, SCA, IaC scanners integrated into every build
No direct pushes to main branch, mandatory security code review
Annual penetration testing and security audits by independent experts
Features | |
|---|---|
| Auditable source code | |
| Prompt tech support | |
| Centralized user management | |
| Fine-tuning of access rights | |
| Role-based user rights management | |
| Group-based access control | |
| Auditable source code | |
| Prompt tech support | |
| Centralized user management | |
| Fine-tuning of access rights | |
| Role-based user rights management | |
| Group-based access control | |
| Event logging and user activity tracking | |
| SIEM integration via syslog | |
| Password audit after staff changes | |
| Password complexity analysis | |
| Secrets Manager is included by default | |
| API for integration with third-party systems | |
| Cross-platform apps (Browser extensions, Desktop apps, Mobile apps) | |
| Failsafe solution with data replication | |
Every team manages credentials differently. See how companies across industries use Passwork to secure access, streamline collaboration, and maintain full control. From small IT teams to enterprise-wide deployments.
Search, autofill, and create credentials without leaving the browser. Works with Chrome, Firefox, Edge, and Safari.
Quick access to your corporate passwords from your mobile device
Convenient login verification using the Passwork authenticator app
Full password management functionality in a native desktop application
Essential features for small and medium businesses to support secure growth
Advanced capabilities for complex security and management needs in large organizations
Book a demo to see your compliance roadmap. Or start a free 14-day trial and deploy Passwork on your own servers today.
Search, autofill, and create credentials without leaving the browser. Works with Chrome, Firefox, Edge, and Safari.
Quick access to your corporate passwords from your mobile device
Convenient login verification using the Passwork authenticator app
Full password management functionality in a native desktop application
Essential features for small and medium businesses to support secure growth
Advanced capabilities for complex security and management needs in large organizations
Book a demo to see your compliance roadmap. Or start a free 14-day trial and deploy Passwork on your own servers today.
Passwork helps organizations implement key security and governance measures expected under NIS2 by centralizing password and access management, reducing credential sprawl, and improving accountability across teams.
Passwork is not a substitute for a full compliance program, but it helps implement several technical and organizational controls relevant to NIS2.
Organizations affected by NIS2 need stronger control over access to critical systems, clearer accountability, and more resilient security processes. Passwork is designed to support these needs in environments where security, control, and auditability matter.
Yes. Passwork helps organizations enforce structured access control by assigning permissions based on roles, teams, vaults, and folders, instead of relying on informal credential sharing.
This helps reduce excessive access and supports the principle of controlled access to critical assets.
Passwork provides activity logging and administrative visibility that help organizations investigate incidents, review user actions, and demonstrate internal control over credential access.
For NIS2-focused organizations, this is important because accountability and traceability are central to effective security governance.
Passwork integrates with common enterprise identity systems to align password access with existing user lifecycle and authentication processes.
This reduces manual administration and helps ensure that access reflects the current organizational structure.
Passwork is built to protect credentials through encryption, controlled access, and secure operational practices.
These measures help reduce the risk of credential compromise and unauthorized access to critical systems.
Yes. Passwork helps security and IT teams respond more effectively to credential-related incidents by giving them a centralized system for access review, password rotation workflows, and event analysis.
This is especially relevant for organizations that need more mature incident handling processes under NIS2.
NIS2 places strong emphasis on resilience and continuity. Passwork supports these goals with deployment and backup options suitable for enterprise environments.
This helps organizations design a credential management environment that remains available and recoverable during disruptions.
Yes. Passwork is suitable for organizations that need strict control over infrastructure, storage location, and internal access boundaries.
This makes Passwork relevant for organizations where cloud-only password storage is not acceptable from a risk or policy perspective.
A major security weakness in many organizations is uncontrolled password sharing through documents, spreadsheets, email, or chat. Passwork replaces these practices with structured, permission-based access.
This helps organizations move from informal password practices to a governed access model aligned with NIS2 expectations.
No. Passwork can support compliance efforts, but NIS2 compliance depends on a broader set of technical, organizational, legal, and operational measures.
A correct positioning statement is: Passwork helps organizations implement credential security controls that support NIS2 compliance efforts.
Please click the button below to change the language
Switch to EnglishFill out the form below to get your copy of the report
Fill out the form below to get your copy of the NIS2 guide