Wi-Fi networks have seamlessly integrated into our lives, becoming as commonplace and expected as electricity flowing through an outlet. They're found everywhere: in homes, cafes, shopping centers, offices, public transport, and even in nature, with our phones often serving as personal hotspots. However, it's easy to overlook that Wi-Fi networks can be a vulnerable point through which cybercriminals might gain access to our devices.
In the context of home Wi-Fi, attackers often aim for personal data such as passwords, banking details, or personal information. Moreover, compromised home Wi-Fi networks can be leveraged for illicit online activities, including downloading pirated content or launching cyberattacks against other systems.
For business Wi-Fi networks, the stakes are higher. Attackers might target confidential corporate information, including financial records, customer data, or proprietary secrets, potentially disrupting business operations. Such breaches can lead to significant consequences, including data leaks, financial losses, or damage to the company's reputation.
The process of Wi-Fi hacking
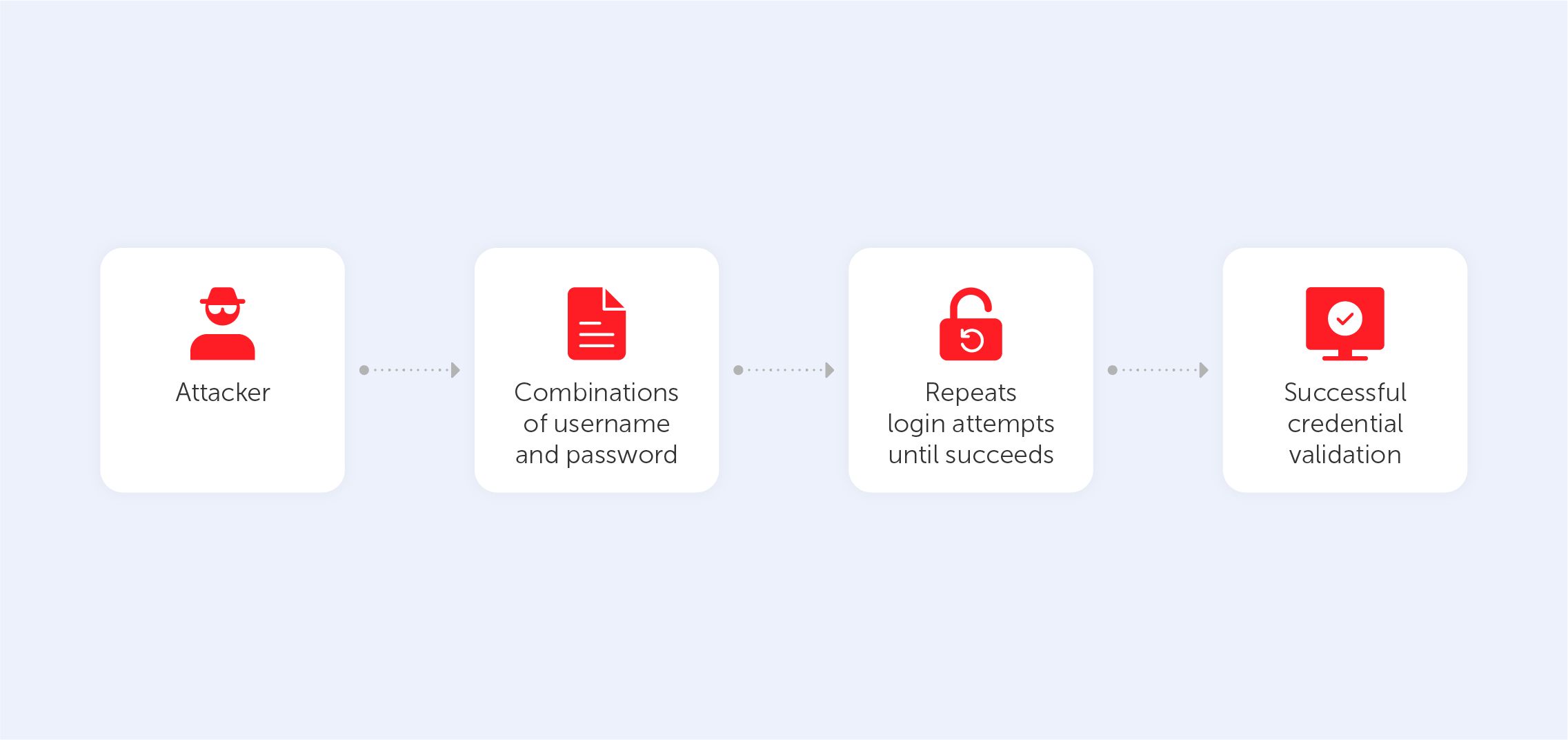
Wi-Fi hacking can be as simple as a neighbor or someone in a nearby office building not wanting to pay for their internet and attempting to use someone else's. Their goal isn't necessarily malicious; often, they just need the router's password, which can be obtained using specialized hacking software. It's important to note that accessing a network without permission is illegal, and such software should only be used for testing the security of one's own network.
Wi-Fi hacking tools typically employ a brute force attack, trying every possible combination of letters and numbers to crack the password. The complexity of the password directly affects the time required to breach it.
In homes, routers connect a wide array of devices, making them a prime target for hackers. Gaining access to a router can open up numerous possibilities for malicious activities, such as data theft, surveillance, or even using the devices for DDoS attacks or covert cryptocurrency mining.
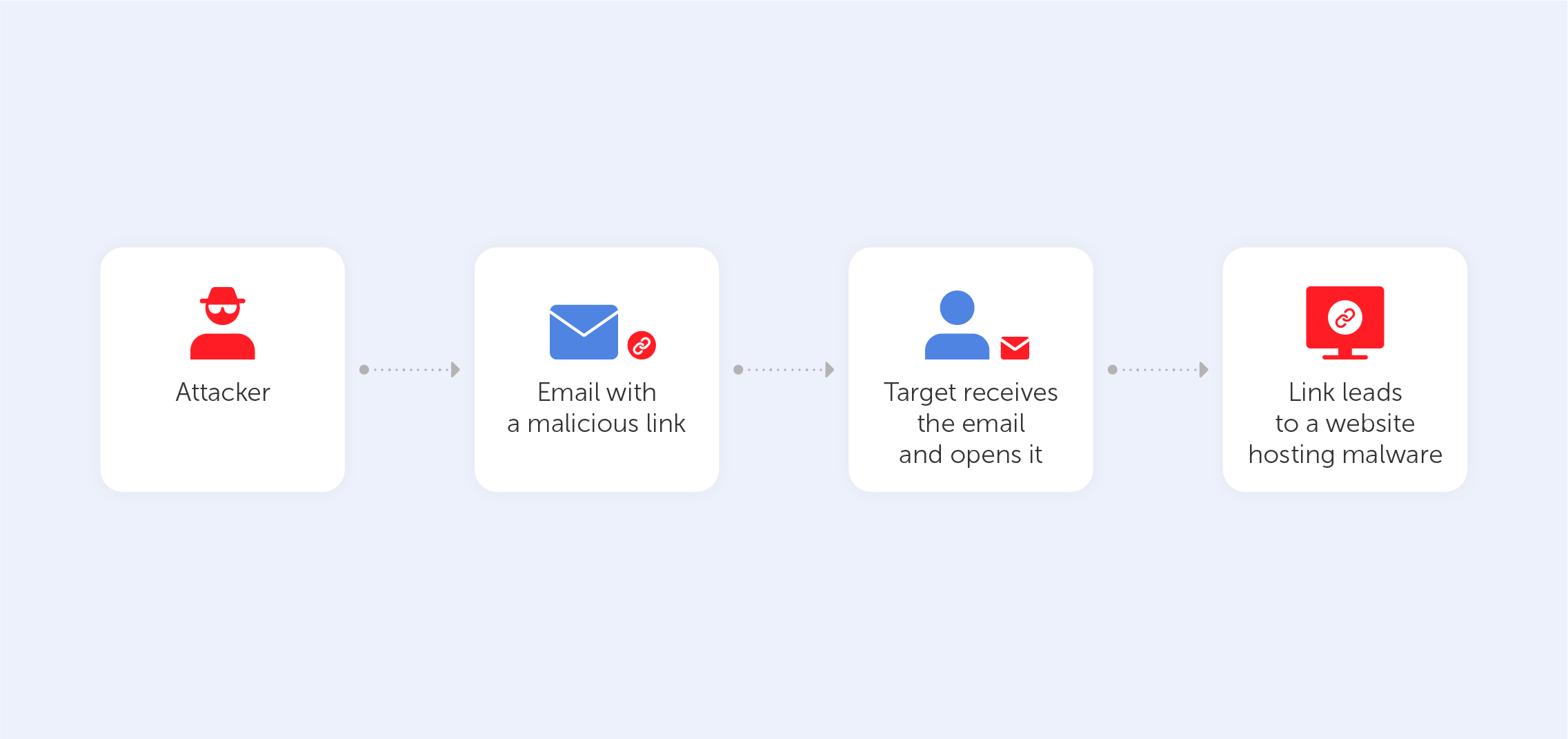
If direct password cracking fails, attackers might exploit security protocol vulnerabilities or create fake access points. For instance, vulnerabilities in WPA-2 security technology were exploited using Key Reinstallation Attacks (KRACK), and in 2024, new vulnerabilities were discovered in Wpa_supplicant software and the iNet Wireless Daemon (IWD).
Another method to gain network access involves social engineering, such as asking for the Wi-Fi password by pretending to be a client or employee.
Identifying a compromised network
The challenge of detecting a hacked network varies significantly between home and corporate environments due to the scale and complexity of the networks involved. For home networks, signs of unauthorized access can often be quite apparent. A sudden decrease in internet speed can indicate that outsiders are consuming bandwidth. Additionally, unfamiliar devices appearing in the router's connected devices list is a telltale sign of a security breach. These indicators are relatively easy to monitor and can quickly alert homeowners to potential security issues.
Corporate networks, however, present a more complex challenge. The sheer volume of devices and the breadth of network activity can obscure the signs of unauthorized access. Yet, there are nuanced indicators that IT professionals can monitor. Unexpected software installations can be a red flag, especially if the new software is unknown or unauthorized by the company's IT department. Similarly, unusual spikes in network traffic or abnormal data flows can indicate that an intruder is siphoning data or exploiting the network for malicious purposes. Monitoring for these signs requires a sophisticated approach, often involving advanced network monitoring tools and a keen understanding of normal network behavior to spot anomalies.
Fortifying Wi-Fi security: strategies and best practices
The first line of defense in network security is the router, serving as the gateway between the internet and the devices on the network. The market offers a wide range of routers, from basic models suitable for home use to advanced routers designed for the complex needs of businesses. The choice of router should be informed by the specific needs and security requirements of the user or organization.
For home networks, security experts advise against the complacency of sticking with the default settings provided by the router manufacturer. One of the simplest yet most effective security measures is changing the default password to a complex, unique one. This step alone can thwart a significant number of unauthorized access attempts. Renaming the network SSID to something generic that doesn't reveal personal information or the router model can also deter potential attackers. Additionally, disabling network discovery and enabling MAC address filtering can further secure the network by making it invisible to casual scans and ensuring that only devices with approved MAC addresses can connect.
Corporate networks require a more layered approach to security, given the higher stakes involved. Routers with advanced security features that can be integrated into a broader security framework are essential. These routers often come with the capability for regular security updates and can be configured to work with Security Incident and Event Management (SIEM) systems, providing real-time monitoring and analysis of security alerts generated by network hardware and applications. For businesses, the security of the router and the network it supports is not just about protecting data; it's also about safeguarding the company's reputation and financial well-being.
Beyond the technical configurations, both home users and businesses must adopt a proactive stance on network security. This includes staying informed about the latest security threats and trends, regularly updating router firmware and network security software, and educating all users about the importance of security practices such as using strong passwords and recognizing phishing attempts.
Conclusion
In 2024, the importance of securing our Wi-Fi networks cannot be overstated. The convenience and connectivity offered by these networks come with inherent risks, making them prime targets for cybercriminals. By understanding the methods employed by hackers and implementing robust security measures, individuals and businesses can significantly mitigate the risks associated with Wi-Fi usage. In the end, the key to safeguarding our digital domains lies in a combination of advanced technology, vigilant monitoring, and an unwavering commitment to cybersecurity.